Thinking about getting your organization set up with Zero Trust? It sounds like a big deal, and honestly, it is. But it’s not some futuristic concept anymore; it’s a practical way to handle security in today’s world. This guide breaks down what you need to know to get started with a solid zero trust adoption strategy. We’ll cover the basics, the building blocks, and how to actually make it work without making things impossible for your team.
Key Takeaways
- Zero Trust means trusting no one by default, not even people inside your network. You always check who’s accessing what, and why.
- Your zero trust adoption strategy needs to focus on who people are (identity) and if their devices are safe, checking them all the time.
- Give people only the access they absolutely need for their job. No more, no less.
- Keep your network and systems divided up. This stops attackers from moving around easily if they get in.
- Always check how well your Zero Trust setup is working and be ready to change things as threats change.
Understanding the Zero Trust Paradigm
The way we think about security has really changed. For a long time, it was all about building a strong wall around our network, like a castle with a moat. If you were inside the walls, you were generally trusted. But that model doesn’t really work anymore with cloud services, remote work, and all sorts of devices connecting from everywhere. That’s where Zero Trust comes in. It’s a different way of looking at things.
Defining Zero Trust Security
Zero Trust is a security strategy that operates on a simple, yet powerful, idea: never trust, always verify. It means we don’t automatically assume anyone or anything is safe, even if they’re already inside our network. Instead, every access request is treated as if it’s coming from an untrusted source. This approach is a big shift from older methods that relied heavily on network perimeters. The goal is to limit the damage if a breach does happen, by making sure people and devices only get access to exactly what they need, and nothing more. It’s about assuming that breaches are not a matter of if, but when, and preparing accordingly. This helps reduce the impact of any security incident, improves how well we can see what’s going on, and makes it easier to meet compliance rules. Zero Trust architectures are built on this principle.
Core Principles of Zero Trust
There are a few main ideas that make up the Zero Trust model:
- Verify Explicitly: Always authenticate and authorize based on all available data points, including user identity, location, device health, service or workload, and data classification. Don’t rely on implicit trust based on network location.
- Use Least Privilege Access: Grant users and devices only the access they need to perform their specific tasks, for the shortest time necessary. This minimizes the potential damage if an account or device is compromised.
- Assume Breach: Operate as if attackers are already inside your network. This means segmenting access, continuously monitoring for threats, and designing your security to limit the
Foundational Pillars of Zero Trust Adoption Strategy
Moving to a Zero Trust model isn’t just about new tech; it’s about rethinking how we approach security from the ground up. Instead of assuming everything inside our network is safe, we operate on the principle that threats can come from anywhere, at any time. This shift requires building our defenses on a few key pillars that support continuous verification and strict access controls.
Identity as the New Perimeter
Forget the old idea of a strong network wall keeping threats out. In a Zero Trust world, your users and their identities are the new perimeter. Every access request, no matter where it originates, must be verified. This means robust identity and access management (IAM) is no longer just an IT function; it’s a core security strategy. We need to know who is asking for access and why. This involves strong authentication methods and making sure that access is granted based on roles and context, not just network location. Strong identity controls are the first line of defense against many common threats.
- Multi-Factor Authentication (MFA): Requiring more than just a password is a must. Think passwords plus a code from a phone, a fingerprint, or a security key. This makes it much harder for attackers to use stolen credentials.
- Role-Based Access Control (RBAC): Assigning permissions based on a user’s job function rather than granting broad access.
- Continuous Authentication: Re-evaluating trust throughout a user’s session, not just at the initial login.
The focus shifts from ‘trust but verify’ to ‘never trust, always verify.’ This constant re-evaluation is key to limiting the impact of any potential breach.
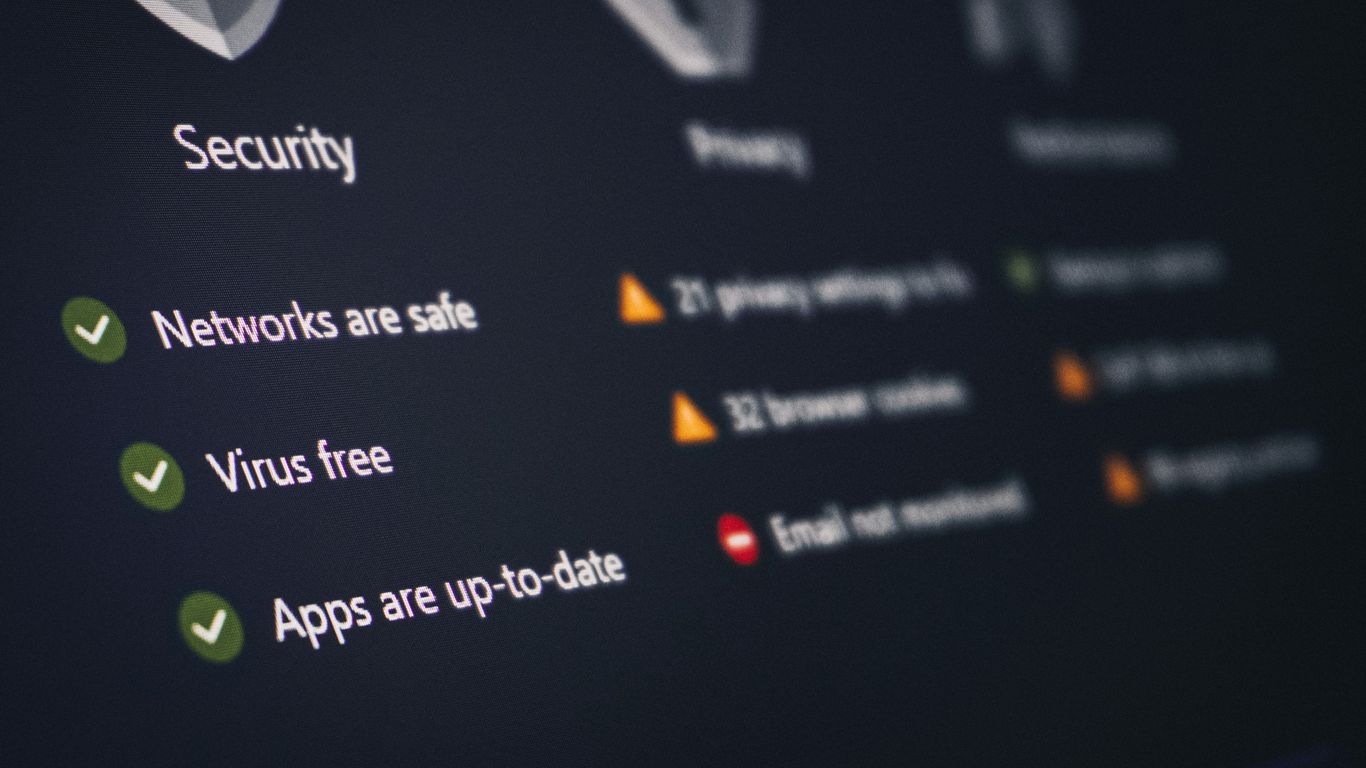
Device Health and Continuous Verification
Just verifying a user’s identity isn’t enough. We also need to know that the device they’re using is healthy and secure. Is the operating system up-to-date? Is the antivirus software running? Are there any signs of malware? Zero Trust demands continuous assessment of device posture. If a device’s health status changes, access can be automatically adjusted or revoked. This is especially important with the rise of remote work and the use of personal devices.
- Endpoint Detection and Response (EDR): Tools that monitor endpoints for suspicious activity.
- Mobile Device Management (MDM): Policies and controls for smartphones and tablets.
- Patch Management: Regularly updating software to fix known vulnerabilities. Maintaining an accurate asset inventory is critical for this.
Least Privilege Access Enforcement
This principle is straightforward: users and systems should only have the minimum level of access necessary to perform their specific tasks. No more broad, standing permissions. If an account is compromised, the damage an attacker can do is significantly limited if that account only had access to a small subset of resources. Implementing least privilege requires careful planning and ongoing management of permissions, but it’s a cornerstone of reducing your attack surface.
- Just-in-Time (JIT) Access: Granting elevated privileges only for a limited time when needed.
- Just-Enough-Access (JEA): Ensuring that even temporary elevated access is restricted to the absolute minimum required actions.
- Regular Access Reviews: Periodically checking who has access to what and removing unnecessary permissions.
These three pillars—identity, device health, and least privilege—form the bedrock of any successful Zero Trust strategy. They work together to create a dynamic and adaptive security posture that’s far more resilient than traditional perimeter-based defenses. Adopting recognized security frameworks can provide a structured approach to implementing these principles.
Implementing Robust Identity and Access Management
In a Zero Trust world, identity isn’t just a factor; it’s the new perimeter. This means we have to get really serious about how we manage who is who and what they can do. It’s not enough to just have a password anymore. We need multiple layers of checks to make sure the right person is accessing the right thing at the right time.
Leveraging Multi-Factor Authentication
Multi-factor authentication, or MFA, is a big deal. It’s like having a security guard check your ID, then ask for a special key, and maybe even a fingerprint. This makes it much harder for attackers who steal passwords to get in. Think about it: if someone gets your password, they still can’t access your account without that second factor, like a code from your phone or a fingerprint scan. It’s a pretty straightforward way to stop a lot of common attacks.
- MFA requires at least two distinct forms of verification.
- It significantly reduces the risk of account takeover.
- It’s a foundational control for any modern security setup.
Implementing Privileged Access Management
Some accounts have way more power than others – think administrator accounts. These are prime targets for attackers. Privileged Access Management (PAM) is all about controlling and watching these super-accounts very closely. We want to make sure only the people who absolutely need these high-level permissions have them, and that we know exactly what they’re doing with them. This often involves things like just-in-time access, where permissions are granted only when needed and for a limited time, and detailed session monitoring. This helps prevent privilege misuse, which is a major concern, especially with insider threats [1a70].
Establishing Strong Identity Governance
Identity governance is the overarching system that makes sure our identity and access controls are working correctly and efficiently. It’s about having clear policies, managing user lifecycles (from onboarding to offboarding), and regularly checking that everyone still has the right access. This includes things like role-based access control (RBAC) and making sure permissions are reviewed periodically. Without good governance, even the best technical controls can fall apart. It’s about having a structured approach to managing who has access to what, aligning with frameworks like NIST [9818].
Strong identity governance ensures that access is granted based on defined roles and policies, and that these permissions are regularly reviewed and adjusted. This continuous oversight is key to maintaining a secure posture in dynamic environments.
Securing Endpoints and Devices
Endpoints and devices are often the first point of entry for attackers. In a Zero Trust model, we can’t just assume these devices are safe, even if they belong to the organization. We need to actively verify their health and security posture before granting access to anything.
Enforcing Device Encryption Standards
Making sure all devices, from laptops to smartphones, have their data encrypted is a basic but really important step. This protects your information if a device gets lost or stolen. It’s not just about setting a password; it’s about making sure the entire storage is scrambled. This is a standard practice that helps prevent unauthorized access to sensitive data stored locally. It’s a foundational element for any security strategy, especially when dealing with remote workers or mobile teams.
Mobile Device Management for Zero Trust
Mobile devices are everywhere now, and they access company resources. We need a way to manage them, even if they’re personal devices used for work (BYOD). Mobile Device Management (MDM) solutions help enforce security policies, like requiring strong passcodes, controlling app installations, and even remotely wiping a device if it’s lost or compromised. This helps maintain a consistent security baseline across all devices accessing your network, aligning with the principles of identity-centric security.
Continuous Device Posture Assessment
Just checking a device’s security once isn’t enough. Things change – software gets outdated, new malware appears, or settings get misconfigured. Continuous device posture assessment means constantly checking if a device meets your security requirements. This includes looking at things like:
- Is the operating system up-to-date?
- Is antivirus software running and updated?
- Are there any known vulnerabilities?
- Is the device jailbroken or rooted?
If a device fails these checks, access can be limited or revoked automatically. This dynamic approach is key to Zero Trust, as trust is never permanent. Regularly assessing device health is a critical part of monitoring security controls.
The goal here is to treat every device as if it could be a potential risk, and to continuously validate that it’s not. This shifts security from a static check to an ongoing process, making it much harder for attackers to exploit vulnerabilities on compromised endpoints.
Network Segmentation and Micro-perimeters
Think of your network like a big office building. In the old days, we just had a strong front door (the firewall), and once you were inside, you could pretty much wander anywhere. That’s not how we do things anymore. Zero Trust means we need to put up walls and doors inside the building, too. That’s where network segmentation comes in.
Limiting Lateral Movement with Segmentation
Segmentation is basically dividing your network into smaller, isolated zones. If a bad actor gets into one zone, they can’t just easily hop over to another. This is super important because it stops them from moving around freely, which is what they love to do to find more valuable stuff. It’s like having separate secure areas for different departments. This approach is key to reducing the impact of breaches.
Here’s why it’s so effective:
- Containment: It keeps security incidents localized, preventing them from spreading across the entire network.
- Reduced Attack Surface: By limiting access between segments, you shrink the areas an attacker can target.
- Improved Monitoring: Smaller, defined zones are easier to monitor for suspicious activity.
Creating Micro-perimeters for Workloads
Now, let’s talk about micro-perimeters. This is taking segmentation to an even finer level. Instead of just segmenting departments, we’re segmenting individual applications or even specific workloads. Imagine each server or application having its own little security bubble. This means even if someone gets into a server, they can’t automatically access the database it talks to unless explicitly allowed. This is especially relevant in cloud environments where workloads can be very dynamic. For instance, securing containerized applications requires careful attention to these micro-perimeters, as attackers might try to break out of the container itself. Verifying each layer is critical.
Enforcing Strict Communication Policies
Once you’ve got your segments and micro-perimeters set up, you need rules. These are your strict communication policies. They dictate exactly what kind of traffic is allowed between these zones and workloads. It’s not just about blocking bad stuff; it’s about explicitly allowing only the necessary communication. This means defining:
- Source and Destination: Which systems can talk to each other?
- Protocols and Ports: What methods can they use to communicate?
- Timing: When is this communication allowed?
Implementing these policies requires a clear understanding of your network traffic flows and dependencies. It’s an ongoing process, not a one-time setup. You’ll need to regularly review and update these rules as your environment changes.
This granular control is what makes Zero Trust work. It moves away from the idea of a trusted internal network and treats every connection as potentially risky, requiring verification and strict policy enforcement at every step. It’s a significant shift from older security models, but it’s necessary for today’s complex threat landscape.
Data Protection in a Zero Trust Environment
In a Zero Trust world, the idea that you can just put a strong wall around your data and call it a day is long gone. Instead, we’re talking about protecting data wherever it lives, assuming that threats could be anywhere, even inside. This means we need to be smarter about how we handle sensitive information.
Data Classification and Sensitivity Labeling
First off, you can’t protect what you don’t know you have. That’s where data classification comes in. It’s about figuring out what data is sensitive, what’s not, and how sensitive it is. Think of it like putting labels on everything. You’ve got your public stuff, your internal memos, your confidential client lists, and then your super-secret R&D plans. Each label tells you how much care and protection that data needs. This isn’t just a nice-to-have; it’s a core part of securing your digital perimeter. Without knowing what’s what, you’re essentially flying blind.
Here’s a quick look at how you might categorize data:
- Public: Information meant for general consumption, like marketing materials.
- Internal: Data for employees only, such as company policies or internal announcements.
- Confidential: Sensitive information that, if exposed, could cause moderate harm, like customer contact details or financial reports.
- Restricted: Highly sensitive data where exposure could cause severe damage, such as intellectual property, personal health information, or trade secrets.
Implementing Encryption for Data at Rest and in Transit
Once you know what data needs protecting, encryption is your next big tool. It’s like putting your data in a locked box. Data at rest is data stored on hard drives, servers, or cloud storage. Data in transit is data moving across networks, like emails or file transfers. Both need protection. Using strong encryption algorithms means that even if someone gets their hands on the data, they can’t read it without the right key. This is a fundamental step to prevent unauthorized access and reduce the impact of breaches. It’s also vital for meeting compliance requirements.
Managing encryption keys is just as important as the encryption itself. If keys are lost or stolen, your encrypted data becomes useless or vulnerable. Secure key management practices are non-negotiable.
Data Loss Prevention Strategies
Data Loss Prevention (DLP) tools are designed to stop sensitive data from leaving your organization’s control. They monitor data as it moves and can block or alert on suspicious activity. This could be someone trying to email a large amount of customer data, upload confidential files to a personal cloud storage, or copy sensitive information to a USB drive. DLP systems work based on the classification labels you’ve applied, enforcing policies to prevent data exfiltration. It’s about setting up guardrails to keep your sensitive information safe and sound, and it’s a key component in responsible data privacy and compliance.
Key aspects of DLP include:
- Monitoring: Watching where data is going and how it’s being used.
- Blocking: Preventing unauthorized transfers of sensitive information.
- Alerting: Notifying security teams when potential data loss events are detected.
- Reporting: Providing insights into data movement and policy violations.
Automating Security Operations for Zero Trust
Implementing Zero Trust means a lot of moving parts need to work together, and doing it all manually just isn’t practical. That’s where automation comes in. It’s not just about making things faster; it’s about making them more reliable and scalable, which is pretty important when you’re dealing with security.
Automated Workflows for Response
When a security event happens, every second counts. Automated workflows can kick in immediately to start the response process. Think about it: instead of a security analyst having to manually check logs, isolate a device, or block an IP address, an automated system can do it in seconds. This drastically cuts down the time it takes to contain a threat, limiting the potential damage. These workflows can be set up to handle common scenarios, like detecting a suspicious login attempt and automatically requiring re-authentication or even temporarily disabling the account until a human can review it. This kind of rapid, automated response is a cornerstone of effective Zero Trust security operations.
Scalability Through Automation
As your organization grows and your digital footprint expands, the number of security events and access requests will naturally increase. Trying to manage this with manual processes simply won’t scale. Automation allows your security operations to keep pace with business growth without a proportional increase in staff. For instance, automated policy enforcement ensures that as new users or devices are added, they are immediately subject to the correct Zero Trust controls. This means you can expand your infrastructure and user base with confidence, knowing that your security posture remains consistent and robust. Automating security governance is key here.
Integrating Security Tools and Workflows
Zero Trust isn’t a single product; it’s a strategy that relies on multiple tools working together. Automation is what bridges these tools and makes them function as a cohesive unit. By integrating your Identity and Access Management (IAM) system, endpoint detection and response (EDR) tools, network security devices, and Security Information and Event Management (SIEM) platform, you can create powerful automated workflows. For example, an alert from an EDR tool about a compromised endpoint could automatically trigger a request to the IAM system to isolate that user’s account and instruct the network firewall to block traffic from the affected device. This kind of integration is vital for achieving a truly effective Zero Trust posture and assessing your security posture effectively.
Automation in security operations isn’t just a nice-to-have; it’s a necessity for modern Zero Trust environments. It allows for faster, more consistent responses to threats, enables security teams to handle increasing workloads without proportional staff growth, and ensures that disparate security tools can work together effectively. Without it, the complexity of Zero Trust can become unmanageable.
Here’s a look at how automation can streamline common Zero Trust tasks:
- Policy Enforcement: Automatically applying access policies based on real-time user and device context.
- Threat Triage: Automatically analyzing and prioritizing security alerts to reduce analyst fatigue.
- Incident Containment: Automatically isolating compromised systems or revoking access upon threat detection.
- Compliance Monitoring: Automatically checking configurations and access logs against defined compliance standards.
Addressing Human Factors in Zero Trust

When we talk about Zero Trust, it’s easy to get caught up in the technology – the firewalls, the identity management, the encryption. But let’s be real, technology is only part of the picture. People are involved in pretty much every step, and that’s where things can get tricky. Ignoring the human element is like building a fortress with a secret, unlocked back door. We need to think about how people interact with our systems and what that means for security.
Cultivating a Strong Security Culture
A strong security culture isn’t just about having policies; it’s about making security a shared responsibility. It means everyone, from the intern to the CEO, understands why security matters and feels empowered to do their part. This involves consistent communication about threats and best practices. It’s about creating an environment where reporting suspicious activity is encouraged, not feared.
- Regular, engaging training: Move beyond the annual click-through modules. Use real-world scenarios and interactive exercises to make learning stick.
- Leadership buy-in: When leaders visibly prioritize security, it sends a powerful message throughout the organization.
- Feedback mechanisms: Allow employees to provide input on security processes. They often have valuable insights into what works and what doesn’t on the ground.
Security isn’t just an IT problem; it’s an organizational challenge that requires everyone’s participation. When security is woven into the fabric of how we work, it becomes a natural part of our daily operations.
Managing Human-Related Vulnerabilities
Let’s face it, humans make mistakes. We get tired, we get distracted, and sometimes we just want to get our work done quickly. This can lead to vulnerabilities like using weak passwords, falling for phishing scams, or misconfiguring systems. In a Zero Trust model, where trust is never assumed, these human-related vulnerabilities become even more critical to manage. We need to build systems that are forgiving of minor errors but also robust enough to detect and block malicious actions. This is where things like security awareness training become really important, helping people recognize threats before they become incidents.
User Behavior Analytics for Anomaly Detection
This is where we start using technology to help us understand human behavior in a security context. User Behavior Analytics (UBA) tools can monitor how users interact with systems and flag anything that looks out of the ordinary. For example, if someone who normally only accesses files in the marketing department suddenly starts trying to access sensitive financial data late at night, UBA can flag that as an anomaly. This isn’t about spying; it’s about identifying potential risks, whether they stem from a compromised account or an insider threat. It’s a proactive way to catch issues that might otherwise go unnoticed. This approach is a key part of a robust insider risk program, helping to mitigate both accidental and intentional security breaches.
Integrating Zero Trust with Cloud and Modern Architectures
Moving to the cloud and adopting modern architectures like microservices and containers changes how we think about security. The old way of building a strong perimeter around everything just doesn’t work when your resources are spread across different cloud providers or running in dynamic, ephemeral environments. Zero Trust fits right into this new landscape because it doesn’t rely on a fixed network boundary. Instead, it focuses on verifying every access request, no matter where it comes from or where it’s going.
Cloud-Native Security for Zero Trust
Cloud platforms offer a lot of built-in security features, but they need to be configured correctly to support a Zero Trust model. This means using identity and access management (IAM) tools provided by the cloud vendor to enforce least privilege access. Think about it: instead of giving broad access to a whole cloud account, you’re granting specific permissions to individual services or functions. This approach aligns perfectly with the Zero Trust principle of explicit verification. We also need to pay close attention to cloud misconfigurations, which are a leading cause of breaches. Tools that continuously monitor cloud settings are really important here.
Securing Dynamic Cloud Environments
Cloud environments are constantly changing. New services are spun up, scaled, and torn down all the time. Traditional security tools that rely on static IP addresses or network segments struggle to keep up. Zero Trust helps by making access decisions based on identity and context, not just network location. This means that even if a workload’s IP address changes, access can still be granted or denied based on verified identity and device health. It’s about making security dynamic, just like the cloud itself. This also means we need to think about how we secure things like APIs and integrations between different cloud services, as these can become new attack vectors.
Adapting Zero Trust for Remote Work
Remote work has become the norm for many organizations, and it further blurs the lines of the traditional network perimeter. Employees are accessing resources from various locations and devices, many of which are outside the corporate network. Zero Trust is ideal for this scenario. By treating every access request as potentially hostile, it provides a consistent security posture whether an employee is in the office or working from home. This involves strong multi-factor authentication for all users and continuous assessment of device health. It’s about making sure that access is granted only when the user and their device meet specific security requirements, regardless of their physical location. This helps reduce the risk associated with compromised credentials and unmanaged devices, which are common issues in remote work setups. For organizations looking to bolster their remote access security, exploring solutions like Zero Trust Network Access (ZTNA) can be a significant step.
The shift to cloud and remote work means security can no longer be about building walls. It has to be about verifying trust at every single interaction, continuously. This requires a fundamental change in how we architect our systems and manage access.
Measuring Success and Continuous Improvement
So, you’ve put in the work to adopt Zero Trust. That’s great! But how do you know if it’s actually working? It’s not enough to just implement the controls; you need to track progress and keep making things better. Think of it like training for a marathon – you don’t just run one long race and call it a day. You measure your pace, track your mileage, and adjust your training plan based on how you’re doing.
Defining Key Security Metrics
To really understand your Zero Trust posture, you need to look at specific numbers. These aren’t just random stats; they should tell you something important about how well your security is holding up. For instance, tracking how long it takes to grant or revoke access for users is a good indicator of your identity management efficiency. Another useful metric is the adoption rate of multi-factor authentication (MFA) across your organization. A higher MFA adoption means fewer accounts are vulnerable to simple password theft.
Here are some areas to focus on:
- Identity and Access Management:
- Time to provision/deprovision user accounts.
- MFA adoption rate.
- Frequency of privileged access reviews.
- Endpoint Security:
- Percentage of devices meeting compliance standards (e.g., encryption enabled, up-to-date OS).
- Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) for endpoint threats.
- Network Security:
- Number of unauthorized access attempts blocked by segmentation policies.
- Percentage of network traffic inspected.
- Data Protection:
- Number of sensitive data access policy violations detected.
- Percentage of critical data encrypted at rest and in transit.
It’s important to remember that metrics should drive action. If a metric shows a weakness, you need a plan to address it. Simply collecting data without acting on it won’t improve your security.
Leveraging Security Frameworks
Frameworks like NIST or CISA provide a structured way to think about security. They offer guidance on what controls to implement and how to measure their effectiveness. Using these frameworks can help you ensure you’re not missing any critical areas and that your Zero Trust implementation aligns with industry best practices. They provide a roadmap, so you’re not just guessing what to do next. For example, NIST SP 800-207 specifically outlines the core concepts and implementation guidance for Zero Trust architectures, helping you build a solid foundation. You can find more details on NIST’s Zero Trust guidance.
Adapting to Evolving Threat Landscapes
The bad guys aren’t standing still, so neither can your security. What works today might not be enough tomorrow. You need to constantly watch what’s happening in the world of cyber threats and adjust your Zero Trust strategy accordingly. This means staying informed about new attack methods, understanding how they might affect your environment, and updating your policies and controls. It’s a continuous cycle of assessment, adaptation, and improvement. Regularly reviewing security incidents and updating your metrics based on new threats is key to maintaining a strong security posture. This proactive approach helps you stay ahead of potential problems before they become major issues.
Moving Forward with Zero Trust
So, we’ve talked a lot about Zero Trust. It’s not really a single product you buy, but more of a way of thinking about security. Instead of assuming everything inside your network is safe, you constantly check who’s accessing what, and from where. This means things like making sure users have strong passwords, or even better, using multi-factor authentication, and checking that devices are healthy before letting them connect. It’s about limiting access to only what’s needed, which can really cut down on the damage if something bad does happen. Implementing it takes time and planning, but it’s becoming pretty standard for good reason. It’s a shift, for sure, but one that makes a lot of sense in today’s world.
Frequently Asked Questions
What is Zero Trust, and why is it important?
Zero Trust is like having a security guard who checks everyone’s ID every time they enter any room, not just the front door. It’s important because it stops bad actors, even if they somehow get inside your network, from moving around and causing more damage. It assumes no one is automatically safe, even if they are already logged in.
How is Zero Trust different from old security methods?
Old security was like a castle with a strong wall and moat. Once you were inside, you were mostly trusted. Zero Trust is like a modern office building where you need a keycard for every door, and the system constantly checks if you should still be there. It focuses on verifying who you are and what you’re doing all the time, not just at the entrance.
What are the main parts of a Zero Trust plan?
Think of it as building blocks. You need to know exactly who your users are and make sure they are who they say they are (Identity). You also need to check that the devices they’re using are safe and up-to-date (Device Health). Finally, you only give people access to the exact things they need to do their job, and nothing more (Least Privilege).
Why is ‘Identity’ so important in Zero Trust?
In Zero Trust, your identity is like your passport. It’s the main way we know who is trying to access something. We use things like passwords combined with codes from your phone (Multi-Factor Authentication) to be really sure it’s you. This stops someone from using stolen passwords to get in.
How does Zero Trust protect data?
Zero Trust protects data by first figuring out how sensitive it is (like marking it ‘Confidential’). Then, it uses special codes (encryption) to scramble the data so no one can read it without the right key, whether it’s stored on a computer or being sent over the internet. It also has systems to stop sensitive data from leaving the company.
Can Zero Trust help with remote work?
Absolutely! With more people working from home or on the go, the old ‘office network’ idea doesn’t work. Zero Trust is perfect because it checks every user and device, no matter where they are. It makes sure that even when you’re not in the office, your access is still secure and verified.
Does Zero Trust mean I have to log in all the time?
It might feel like it sometimes, but it’s more about continuous checking than constant re-logins. The system constantly looks at things like who you are, the health of your device, and what you’re trying to do. If anything looks risky, it might ask for another check or even stop your access to keep things safe.
Is Zero Trust hard to set up?
Setting up Zero Trust can be a journey, not a quick fix. It involves changing how you think about security and using new tools. But by breaking it down into steps, like focusing on identity first, and using automation to help manage things, it becomes much more manageable and effective over time.
