Thinking about where your company stands with its security is a big deal. It’s not just about having some antivirus software; it’s a whole picture. This article looks at how to figure out how good your security really is, using something called security maturity benchmarking. We’ll break down the different areas you need to think about, from the basics to how you handle things when something goes wrong. It’s all about getting a clear view and making things better, step by step.
Key Takeaways
- Building a strong security foundation means getting the basics right, like knowing what weaknesses you have and how to fix them, managing risks, and following the rules.
- Protecting your digital borders involves smart network setups, making sure only the right people have access, and giving them only the access they absolutely need.
- Keeping your data safe means knowing what data you have, how sensitive it is, and using tools like encryption to keep it private and unchanged.
- When it comes to your apps and development, building security in from the start is way better than trying to patch it up later.
- As you look at your overall security, think about how people use systems, how you train them, and how leadership can make security a normal part of how everyone works.
Establishing Foundational Security Controls
Getting the basics right is the first step in building a strong security posture. It’s like building a house; you need a solid foundation before you start worrying about the fancy roof tiles. Without these core controls, everything else you try to build on top is going to be shaky.
Vulnerability Management and Testing
This is all about finding the weak spots before the bad guys do. You can’t fix what you don’t know is broken, right? So, we’re talking about regularly scanning your systems and applications for known weaknesses. Think of it as a regular check-up for your digital assets. This includes things like penetration testing, which is basically hiring someone to try and break into your systems to see where they succeed. It’s not about finding every single flaw, but about understanding your biggest risks and having a plan to deal with them. Continuous assessment is necessary due to evolving threats.
Here’s a quick look at the process:
- Identification: Finding the vulnerabilities through scans and tests.
- Assessment: Figuring out how serious each vulnerability is.
- Prioritization: Deciding which ones to fix first based on risk.
- Remediation: Actually fixing the problems, usually through patching or configuration changes.
Risk Management and Mitigation
Once you know about the vulnerabilities, you need to figure out what they mean for your business. Risk management is about looking at the likelihood of something bad happening and how much it would hurt if it did. Then, you decide what to do about it. Sometimes you can avoid the risk, sometimes you can reduce it, sometimes you pass it on (like with insurance), and sometimes you just have to accept it because the cost to fix it is too high. It’s all about making smart decisions that align with what the organization can handle. Reducing your attack surface is a big part of this.
Compliance and Standards
This part is about meeting the rules. There are lots of regulations and industry standards out there, like NIST or ISO, that give you a roadmap for good security. Following these standards doesn’t automatically make you secure, but not following them definitely makes you more exposed. It’s about having documented controls and being able to prove you’re doing what you’re supposed to. Think of it as having a checklist to make sure you haven’t missed anything important.
Establishing these foundational controls isn’t just a technical exercise; it’s a business imperative. It requires clear ownership, consistent processes, and a commitment to ongoing improvement. Without this bedrock, efforts in more advanced security areas will likely falter.
Securing the Digital Perimeter
Think of your digital perimeter as the outer wall of your organization’s network and systems. It’s where you meet the outside world, and it’s absolutely critical to get this right. If your walls are weak, attackers can walk right in. We’re talking about making sure only the right people and systems can get in, and that they can only access what they absolutely need. It’s about building strong defenses at every entry point.
Network Segmentation and Isolation
One of the most effective ways to secure your perimeter is by breaking your network into smaller, isolated zones. This is called network segmentation. Instead of one big, open space, imagine a building with many locked rooms. If someone gets into one room, they can’t just wander into all the others. This limits the damage an attacker can do if they manage to breach one part of your network. It’s a core part of a zero trust architecture, where trust is never assumed, even for internal traffic. This approach means that even if a device on your network is compromised, the threat is contained and can’t easily spread to other critical systems.
- Micro-segmentation: Isolating individual workloads or applications.
- VLANs: Dividing a physical network into multiple logical networks.
- Firewalls: Acting as gatekeepers between network segments.
Identity and Access Governance
Who is allowed to access what? That’s the heart of identity and access governance. It’s not just about passwords anymore. We need strong ways to verify who someone is (authentication) and then control what they can do once they’re in (authorization). This includes things like multi-factor authentication (MFA), which requires more than just a password, and making sure that access is reviewed regularly. Weak identity systems are often the first place attackers look to get in, so getting this right is a big deal.
| Control Area | Key Components |
|---|---|
| Authentication | Multi-factor Authentication (MFA), SSO |
| Authorization | Role-Based Access Control (RBAC), Attribute-Based Access Control (ABAC) |
| Access Review | Periodic audits, Just-in-Time (JIT) provisioning |
| Identity Lifecycle Mgmt | Onboarding, offboarding, role changes |
Strong identity and access controls are the bedrock of perimeter security. They prevent unauthorized access by verifying users and systems rigorously before granting entry and defining precisely what actions are permitted.
Least Privilege and Access Minimization
Once someone or something is inside your network, they should only have access to the bare minimum they need to do their job. This is the principle of least privilege. If an account or system doesn’t need access to sensitive data, it shouldn’t have it. Giving out too many permissions, often called over-permissioning, is like leaving doors unlocked all over your building. It creates a much larger attack surface and makes it easier for attackers to move around your network if they gain a foothold. Limiting access to only what’s necessary significantly reduces the potential impact of a compromise.
Protecting Data Integrity and Confidentiality

Keeping your data safe and sound is a big deal, right? It’s not just about stopping hackers from getting in; it’s also about making sure the information you have is accurate and hasn’t been messed with. This section looks at how we actually do that.
Data Classification and Control
First off, you can’t protect what you don’t know you have. That’s where data classification comes in. It’s like sorting your mail – you put the important bills in one pile, junk mail in another. We sort data based on how sensitive it is. Is it public info, or is it something that could cause real trouble if it got out, like customer Social Security numbers? Once you know what’s what, you can put the right locks on it. This means setting up rules so only certain people or systems can even see or touch specific types of data. It’s a pretty straightforward idea, but doing it well across a whole company takes some effort.
- Identify and categorize all data assets.
- Assign sensitivity levels (e.g., public, internal, confidential, restricted).
- Implement access controls based on classification.
- Regularly review and update classifications.
Encryption and Integrity Systems
Okay, so you’ve sorted your data. Now, how do you scramble it so nobody can read it without the right key? That’s encryption. We use it for data both when it’s sitting still (at rest) and when it’s moving around (in transit). Think of it like sending a coded message. But encryption is only half the story. We also need to make sure the data hasn’t been changed without permission. This is where integrity checks come in. They’re like a digital seal of approval, letting you know if a file has been tampered with. Without both, you’re leaving the door open for snooping and sneaky alterations. It’s a core part of keeping your digital information trustworthy.
Protecting data integrity and confidentiality means more than just preventing unauthorized access; it’s about maintaining the accuracy and trustworthiness of information throughout its lifecycle.
Secrets and Key Management
This is where things can get a bit tricky. ‘Secrets’ are basically the keys to the kingdom – things like API keys, passwords, and certificates that let systems talk to each other or access sensitive resources. If these get into the wrong hands, it’s game over. So, we need super secure ways to store them, rotate them often (like changing your locks periodically), and keep an eye on who’s using them. A lot of security problems happen because these secrets are left lying around or are used for too long. Proper management of these sensitive credentials is vital to prevent things like credential replay attacks.
| Secret Type | Storage Method | Rotation Frequency | Auditing Frequency |
|---|---|---|---|
| API Keys | Vault/Secrets Manager | Monthly | Daily |
| Database Passwords | Vault/Secrets Manager | Quarterly | Weekly |
| SSL Certificates | Secure Key Store | Annually | Monthly |
Enhancing Application and Development Security
When we talk about making sure our software is safe, it really comes down to building it right from the start. It’s not just about fixing things after they break; it’s about preventing problems before they even show up. This means thinking about security at every single step, from when someone first draws up the plans for an app to when it’s actually out there being used.
Secure Software Development Practices
This is where the rubber meets the road for building secure apps. It’s about baking security into the whole process, not just tacking it on at the end. Think of it like building a house – you wouldn’t wait until the roof is on to think about the foundation, right? The same applies here. We need to train developers on how to write code that doesn’t have obvious holes. This includes things like:
- Code Reviews: Having other developers look over the code to spot potential issues.
- Threat Modeling: Thinking like an attacker to figure out where the weak spots might be before anyone else does.
- Dependency Management: Keeping track of all the outside libraries and tools used in the project and making sure they’re safe.
- Secure Coding Standards: Following established guidelines for writing code that avoids common mistakes.
The goal is to catch and fix vulnerabilities early, ideally before the code is even deployed.
Application Security Testing
Even with the best practices, sometimes flaws slip through. That’s where testing comes in. We need to actively look for weaknesses in our applications. There are a few main ways we do this:
- Static Application Security Testing (SAST): This is like a spell-checker for code, looking for security bugs without actually running the application.
- Dynamic Application Security Testing (DAST): This involves testing the application while it’s running, trying to poke and prod it to see if it breaks or reveals sensitive information.
- Interactive Application Security Testing (IAST): This combines aspects of both SAST and DAST, often using agents within the running application to find issues.
Regular testing helps us find problems like SQL injection or cross-site scripting before attackers can exploit them. It’s a continuous effort, not a one-time check.
DevSecOps Maturity
DevOps is all about speeding up how we build and release software by breaking down walls between development and operations teams. DevSecOps takes that a step further by bringing security into the mix from the very beginning. It’s about making security a shared responsibility, not just the job of a separate security team.
As organizations mature in DevSecOps, they start to automate security checks within their development pipelines. This means security tests run automatically every time code is changed, providing quick feedback. It’s a shift towards making security a natural part of the development workflow, rather than an afterthought. This integration helps reduce the time it takes to find and fix security issues, leading to faster and safer software releases.
Navigating Cloud and Edge Computing Security
Moving workloads and data to the cloud or to edge devices introduces a whole new set of security puzzles. It’s not just about setting up firewalls anymore; we’re talking about protecting systems that are often distributed and accessed over the internet.
Cloud Security Controls
When you put your stuff in the cloud, remember that security is a shared deal. The cloud provider handles some things, but you’re still on the hook for how you set things up and manage access. Misconfigurations are a huge problem here, often leading to data leaks or unauthorized access. It’s really about making sure your settings are locked down tight and that you’re watching what’s going on.
- Identity and Access Management (IAM): This is your first line of defense. Who gets to see what? IAM systems manage that. Think strong passwords, multi-factor authentication, and making sure people only have the access they absolutely need.
- Data Encryption: Keep your data safe, both when it’s moving (in transit) and when it’s just sitting there (at rest).
- Configuration Management: Regularly check that your cloud services are set up securely. Automated tools can help catch mistakes before they become problems.
- Monitoring and Logging: Keep an eye on activity. Logs can tell you if something weird is happening, which is key for spotting trouble early.
Cloud Access Security Brokers (CASBs)
CASBs act like a security guard for your cloud apps. They give you a way to see what cloud services people are using and to enforce your company’s rules. This is super helpful because employees might use cloud apps without IT even knowing about it.
- Visibility: CASBs show you which cloud apps are being used, whether they’re approved or not.
- Data Protection: They can help stop sensitive data from being uploaded to unapproved cloud services.
- Threat Detection: CASBs can spot risky user behavior or signs of malware.
- Compliance: They help make sure your cloud usage meets regulatory requirements.
The shift to cloud environments means traditional security perimeters are less relevant. Instead, security often centers around verifying identities and controlling access to resources, regardless of location.
Edge Computing Security
Edge computing means processing data closer to where it’s generated, like on IoT devices or local servers. This creates a lot of distributed points that need protection. Unlike a central data center, these edge devices might be in less secure physical locations and harder to manage.
- Device Security: Each edge device needs to be secured, often with strong authentication and regular updates.
- Network Isolation: Keep edge devices separate from your main network to limit the damage if one gets compromised.
- Data Protection: Sensitive data processed at the edge needs to be protected, often through encryption.
- Monitoring: Keeping an eye on edge devices for unusual activity is important, even though they are spread out.
The complexity of managing security across both cloud and edge environments requires a unified approach to visibility and control.
Strengthening Incident Response and Resilience
When a security incident happens, and it will, how quickly and effectively your organization can bounce back is what really matters. It’s not just about stopping the bad guys; it’s about getting back to normal operations with minimal disruption. This section looks at how to build that capability.
Incident Response Governance
Having a clear plan for who does what during a security event is key. This means defining roles, setting up communication channels, and knowing who has the authority to make decisions. Without this structure, things can get chaotic fast. Think of it like a fire drill – everyone knows their part, so the response is coordinated and swift. Good governance means you’re not figuring things out for the first time when the alarm is blaring. It also involves having playbooks and runbooks ready, which are step-by-step guides for common incidents. These documents help speed up response and reduce errors, especially when dealing with things like token hijacking methods.
Business Continuity and Disaster Recovery
This is about keeping the lights on, even when things go sideways. Business continuity planning focuses on maintaining essential functions during a disruption, while disaster recovery is about getting systems back up and running after a major event. It’s a two-pronged approach to resilience. This involves identifying critical business processes and having backup plans in place. Regular testing of these plans, like tabletop exercises, is super important to make sure they actually work when you need them.
| Critical Function | Recovery Time Objective (RTO) | Recovery Point Objective (RPO) |
|---|---|---|
| Customer Support | 4 hours | 1 hour |
| Financial Systems | 8 hours | 30 minutes |
| Core Operations | 2 hours | 15 minutes |
Security Metrics and Monitoring
You can’t improve what you don’t measure. Tracking key metrics helps you understand how well your incident response is working. This includes things like how long it takes to detect an incident (Mean Time To Detect – MTTD) and how long it takes to get things back to normal (Mean Time To Recover – MTTR). Continuous monitoring is also vital. It means constantly watching your systems for unusual activity, not just waiting for an alert. This helps catch issues early and adapt to new threats.
Effective incident response isn’t just about having tools; it’s about having well-rehearsed processes and clear accountability. Regular drills and post-incident reviews are non-negotiable for building true resilience.
Leveraging Threat Intelligence and Collaboration
Understanding what’s happening out there in the digital world is pretty important for staying safe. It’s not just about fixing your own systems; it’s about knowing what the bad guys are up to. That’s where threat intelligence comes in. It’s basically information about potential or current threats to your organization. This can include details about new malware, attack methods, or groups that are targeting businesses like yours.
Threat Intelligence and Information Sharing
Collecting threat intelligence on your own can be a lot of work. That’s why sharing this information with others is becoming a bigger deal. When organizations share what they know, everyone gets a bit smarter and better prepared. It’s like a neighborhood watch for the internet. You report a suspicious car, and your neighbors are more aware. Platforms for sharing this kind of data are popping up, making it easier for companies to contribute and benefit.
- Sharing threat data helps build a stronger collective defense.
- It allows for quicker identification of emerging threats.
- Collaboration can lead to the development of better defensive strategies.
Threat Evolution
The people trying to break into systems aren’t standing still. They’re getting more organized, using automation, and are often motivated by money. Attacks aren’t usually just one simple trick anymore; they’re often a mix of different tactics. They might try to trick you into giving up your password, use stolen credentials, or even use tools already built into your systems to hide their tracks. It’s a constant game of catch-up.
Ransomware Evolution
Ransomware has gotten pretty nasty. It’s not just about locking up your files anymore. Now, attackers might steal your data first and then threaten to release it if you don’t pay (that’s double extortion). Sometimes, they’ll even try to hit you with a third type of demand. The availability of ransomware as a service also means that people who aren’t super technical can get in on the action, leading to more attacks overall.
Staying ahead means understanding not just the technical side of attacks, but also the motivations and evolving tactics of threat actors. This knowledge is key to adapting defenses before an attack happens.
Addressing Human Factors in Security
When we talk about security, it’s easy to get caught up in firewalls, encryption, and all the technical stuff. But let’s be real, a lot of security issues pop up because of us, the people using the systems. It’s not always about bad guys breaking in; sometimes, it’s just a simple mistake or a lack of awareness that opens the door. We need to think about how people actually work and interact with technology, not just how we wish they would.
Security Usability
Security controls that are too complicated or get in the way of daily tasks often get bypassed. People find workarounds, which can actually make things less secure. Think about a password policy that requires a new, complex password every week – people will just write it down somewhere obvious or use a predictable pattern. Making security tools and processes easier to use, without sacrificing protection, is key. When security fits into the workflow, people are more likely to use it correctly.
Human Factors and Security Awareness
This is where training comes in, but it’s got to be more than just a yearly checkbox. We need ongoing education that actually sticks. This means teaching people how to spot phishing emails, why reusing passwords is a bad idea, and what to do if they suspect something is wrong. It’s about building a habit of thinking securely.
Here are some common areas where human behavior impacts security:
- Phishing and Social Engineering: Attackers often trick people into giving up information or clicking malicious links by pretending to be someone trustworthy. This relies on human psychology, like urgency or authority.
- Credential Management: Weak passwords, password reuse, and insecure storage of login details are huge risks. People often do this for convenience, not malice.
- Insider Threats: This can be accidental (like misconfiguring a setting) or intentional (like stealing data). Understanding motivations and providing clear guidelines helps.
- Reporting Incidents: People need to feel comfortable reporting suspicious activity without fear of getting in trouble. A clear, simple reporting process is vital.
Security isn’t just about technology; it’s about people. When we design systems and processes with the user in mind, and provide clear, consistent education, we build a stronger defense. Ignoring the human element is like leaving the front door unlocked.
Reporting Security Incidents
Having a process for reporting security issues is one thing, but making sure people actually use it is another. If reporting an incident means filling out a ten-page form or waiting on hold for an hour, people won’t do it. We need simple, accessible ways for anyone to report something that seems off. This could be a dedicated email address, a button in an application, or a quick chat message. The faster an incident is reported, the quicker we can deal with it and limit any potential damage. It’s a critical part of our overall defense strategy.
Integrating Security into Organizational Culture
Making security a part of how everyone works, not just a task for the IT department, is a big deal. It’s about shifting mindsets so that security is considered from the start, not as an afterthought. This isn’t just about following rules; it’s about building a shared responsibility for protecting our digital assets.
Leadership Influence
Leaders play a huge role here. When executives visibly support and prioritize security, it sends a clear message throughout the company. This means allocating resources, talking about security in meetings, and holding people accountable. It’s not enough for security to be a checkbox item; it needs to be woven into the fabric of business decisions.
Security Champions
Think of security champions as the go-to people for security questions within their own teams. They aren’t necessarily security experts, but they understand the importance of security and can help bridge the gap between the security team and the rest of the organization. They can spot potential issues early and help spread best practices.
Here’s a look at how champions can help:
- Awareness: They remind colleagues about security policies and best practices.
- Feedback: They gather input from their teams about security challenges and relay it to the security department.
- Advocacy: They promote security initiatives and encourage adoption of new tools or processes.
Continuous Behavioral Improvement
Security isn’t a one-time training session. It’s an ongoing process that requires constant attention and adaptation. We need to look at how people actually behave and find ways to encourage secure actions. This might involve making security tools easier to use or providing feedback when mistakes happen, focusing on learning rather than blame.
Security is a human endeavor. Technical controls are important, but they only go so far. If people don’t understand why security matters or find it too difficult to follow, they’ll find ways around it. Building a strong security culture means making security practical, understandable, and a shared goal for everyone.
Adapting to Evolving Regulatory Landscapes
Staying on top of the rules and laws that govern cybersecurity can feel like a full-time job on its own. Regulations aren’t static; they’re constantly changing, often becoming more complex and demanding. This means organizations can’t just set up their security and forget about it. They need to actively monitor what’s happening in the legal and compliance world.
Regulatory Expansion
Globally, we’re seeing a definite increase in cybersecurity regulations. It’s not just about data protection anymore; it’s also about operational resilience and reporting requirements. This expansion means more paperwork, more audits, and a greater need for clear documentation of security practices. Failure to keep pace can lead to significant fines and reputational damage. For instance, new rules might require specific types of data encryption or mandate how quickly a breach must be reported. It’s a lot to track.
Compliance and Regulatory Requirements
Meeting these requirements involves more than just ticking boxes. It means understanding the intent behind the regulations and integrating them into your actual security operations. This often involves:
- Mapping existing controls to regulatory mandates.
- Conducting regular gap analyses to identify areas needing improvement.
- Implementing new technologies or processes to meet specific compliance needs.
- Training staff on relevant policies and procedures.
It’s about building a security program that is not only effective against threats but also demonstrably compliant with legal obligations. This often means aligning with established frameworks like NIST or ISO 27001, which provide a solid foundation for managing compliance.
Privacy and Data Governance
Privacy is a huge part of the regulatory puzzle. Laws like GDPR and CCPA dictate how personal data must be handled, stored, and protected. This ties directly into cybersecurity because protecting data from unauthorized access is a core tenet of privacy. Organizations need robust data governance programs that define:
- How data is collected and used.
- Who has access to it.
- How long it’s retained.
- How it’s secured throughout its lifecycle.
The intersection of privacy and cybersecurity demands a proactive approach. It’s not enough to secure data; you must also ensure its use aligns with legal and ethical standards, especially concerning personal information.
This requires careful planning and ongoing vigilance to ensure that data handling practices are both secure and compliant with the ever-shifting legal landscape.
Managing Third-Party and Supply Chain Risks
It’s easy to think of security as just what happens inside your own walls, but that’s not the whole story. A big chunk of risk comes from outside, specifically from the vendors, partners, and software providers you rely on. Think of it like this: you might have the strongest locks on your doors, but if you let someone with a weak lock into your house, your whole place is vulnerable. That’s the essence of third-party and supply chain risk.
Vendor and Third-Party Behavior
When you bring in a vendor or partner, you’re essentially extending your own security perimeter. If their security is shaky, it becomes a weak point that attackers can target to get to you. This isn’t just about big software companies; it includes everything from your cloud service provider to the company that cleans your office. We need to look at how these external entities handle security. Are they patching their systems? Do they have basic access controls in place? Understanding their security posture is just as important as managing your own.
Here are some common areas where third-party risk shows up:
- Compromised Software Updates: Attackers inject malicious code into legitimate software updates, which then get distributed to all users.
- Third-Party Libraries: Applications often use code from external sources. If one of these libraries has a vulnerability, it can affect all applications using it.
- Managed Service Providers (MSPs): MSPs often have broad access to client systems. A compromise here can lead to widespread impact.
- Cloud Service Providers: While generally secure, misconfigurations or breaches within a cloud provider’s infrastructure can affect many customers.
Supply Chain Attacks
Supply chain attacks are a specific, and often devastating, type of third-party risk. Instead of attacking you directly, attackers go after a weaker link in your supply chain – maybe a software vendor, a hardware manufacturer, or even a service provider. They compromise that link, and then use it as a pathway to reach their ultimate target: your organization. This can happen through compromised software updates, malicious hardware components, or even through compromised credentials of a vendor employee who has access to your systems. The impact can be huge, affecting many organizations at once because they all rely on the same compromised source.
The interconnected nature of modern business means that a security lapse in one organization can ripple outwards, affecting numerous others. This interconnectedness, while driving efficiency, also creates a larger attack surface that spans beyond direct organizational control. It requires a shift in perspective from solely internal defense to a more holistic view of the entire ecosystem.
Measuring and Improving Security Posture
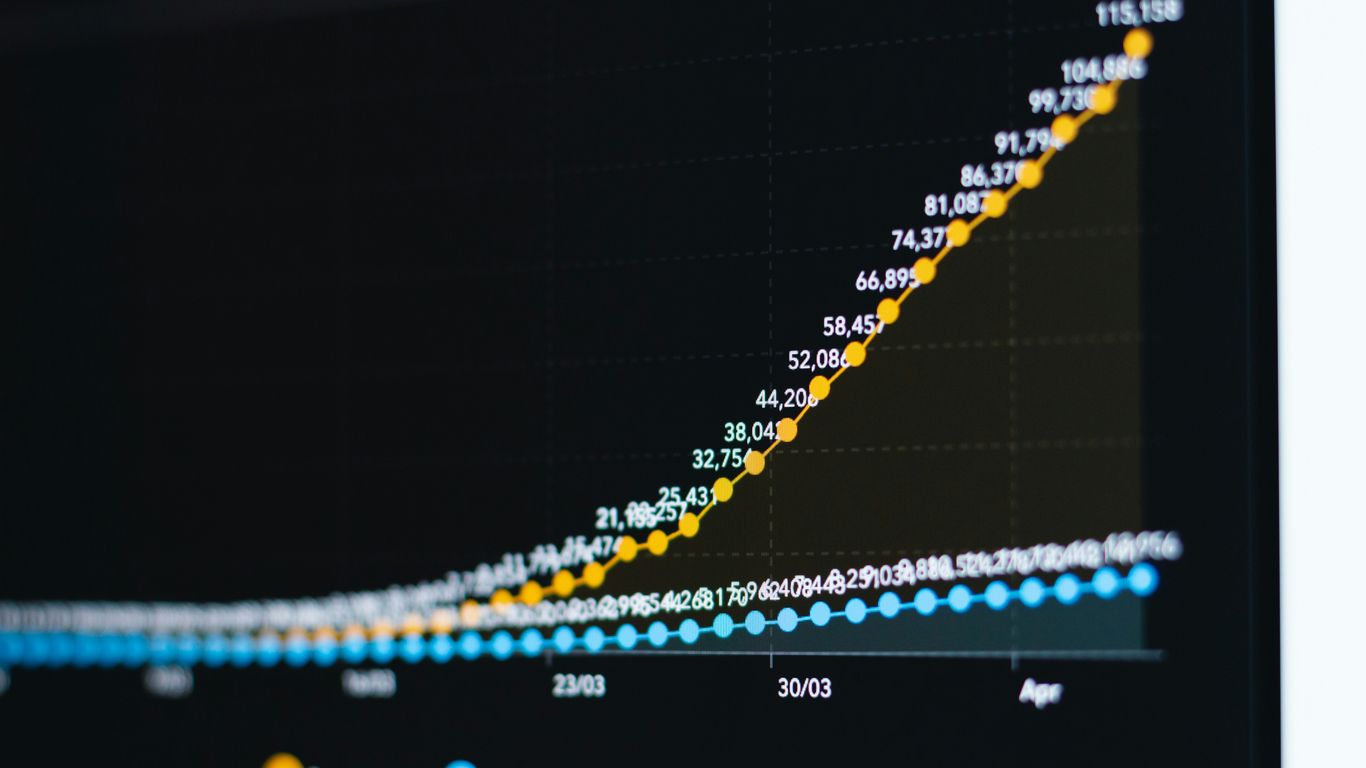
Measuring Security Performance
Knowing where you stand is the first step to getting better. We need to look at how well our security is actually working, not just what we think is in place. This means tracking things that show us what’s happening. Are we seeing fewer security events? How fast can we fix problems when they pop up? These aren’t just numbers; they tell a story about our defenses.
Here are some key areas to measure:
- Incident Frequency: How often do security incidents occur? A lower number here is good.
- Mean Time to Detect (MTTD): How long does it take us to notice a problem after it starts?
- Mean Time to Respond (MTTR): Once we know about an issue, how quickly can we fix it?
- Vulnerability Patching Rate: How fast are we applying fixes to known weaknesses?
- Security Control Coverage: What percentage of our systems and assets are protected by key security controls?
Tracking these metrics helps us see trends over time. If our MTTD is going up, something’s wrong with our detection systems or processes. If MTTR is increasing, our response teams might be overloaded or lack the right tools.
Cybersecurity as Continuous Governance
Security isn’t a project you finish; it’s something you have to keep doing. Think of it like maintaining a house. You can’t just fix the roof once and forget about it. New threats pop up, technology changes, and our own business grows, all of which can create new risks. This is where continuous governance comes in. It’s about having a system in place that constantly checks if our security is still doing its job and adapts when it needs to.
This means:
- Regular Reviews: Periodically checking policies, procedures, and controls to make sure they’re still relevant and effective.
- Adaptation: Being ready to change our security approach when new technologies emerge or when we learn about new attack methods.
- Accountability: Making sure people know who is responsible for what aspects of security and that they are held to it.
Security as Code
This is where we get technical about making security more reliable and repeatable. ‘Security as Code’ means treating our security configurations, policies, and even some testing like software code. We write it down, put it in a system where we can track changes, and automate its deployment. This helps us avoid mistakes that happen when people manually set things up, and it makes sure our security is applied consistently everywhere.
For example, instead of manually configuring firewalls on a dozen servers, we can write a script that does it for all of them. If we need to change a rule, we update the script and re-deploy it. This is much faster and less error-prone.
| Area | Traditional Approach | Security as Code Approach |
|---|---|---|
| Firewall Rules | Manual configuration | Automated script deployment |
| Access Controls | Manual user provisioning | Policy-driven automation |
| Security Audits | Periodic manual checks | Automated compliance checks |
| Vulnerability Scan | Manual trigger | Scheduled, automated scans |
Looking Ahead
So, we’ve talked a lot about where security stands right now, looking at things like how we manage software updates, how we control who gets into what, and even how people behave online. It’s clear that keeping things secure isn’t just about buying the latest tech; it’s a whole mix of technology, smart processes, and, honestly, getting people to do the right thing. As technology keeps changing, like with more cloud use and new ways to connect devices, the risks change too. Staying on top of this means we can’t just set and forget. We need to keep checking how well our security is working, learn from mistakes, and adjust our plans. It’s a constant effort, but building a strong security setup helps keep businesses running smoothly and protects what matters.
Frequently Asked Questions
What does it mean to have strong security?
Having strong security means your digital stuff, like computers and information, is well-protected from bad guys trying to steal or mess with it. It’s like having strong locks and guards for your house, but for your online world.
Why is it important to test for security weaknesses?
Imagine knowing where the weak spots in your fence are before a burglar does. Testing for security weaknesses is like that – it helps you find and fix problems before they can be used to break in and cause trouble.
What’s the point of ‘least privilege’?
Least privilege means giving people and computer programs only the access they absolutely need to do their job, and nothing more. This way, if one part gets messed up, it can’t easily spread and cause bigger problems.
How does encrypting data help?
Encryption is like scrambling a secret message so only someone with the special key can unscramble and read it. It keeps your information private, even if someone manages to get their hands on it.
What is DevSecOps?
DevSecOps is a way of building software where security is thought about from the very beginning, not just at the end. It means developers, security experts, and operations teams work together closely to build safer programs faster.
Why is cloud security different from regular security?
Cloud security is about protecting information and systems that are stored and run on computers owned by someone else (like Google or Amazon). It involves different rules and tools because you don’t have direct control over the physical machines.
What happens if a security problem occurs?
If a security problem happens, having a good plan (like an incident response plan) helps you deal with it quickly and effectively. It’s about knowing who to call, what steps to take, and how to get things back to normal as fast as possible.
How do people play a role in security?
People are a big part of security! Being aware of risks, like not clicking on suspicious links or sharing passwords, makes a huge difference. Training and clear rules help everyone be a good digital citizen and protect themselves and the organization.
