Assessing your security posture is kind of like checking the locks on your house and making sure the windows are shut before you leave. You want to know what’s strong and what might be a weak spot. It’s not just about the fancy firewalls, either. People play a big role, and so do the everyday tools we use. This article looks at different ways to figure out how well your defenses are holding up. We’ll cover how to spot issues, fix them, and keep things secure as the world of threats keeps changing. It’s all about getting a clear picture so you can make smart choices.
Key Takeaways
- Understanding human behavior is key. Things like how aware people are of threats, how easily they might fall for scams, and how they handle sensitive information all impact your security. Training and clear processes help here.
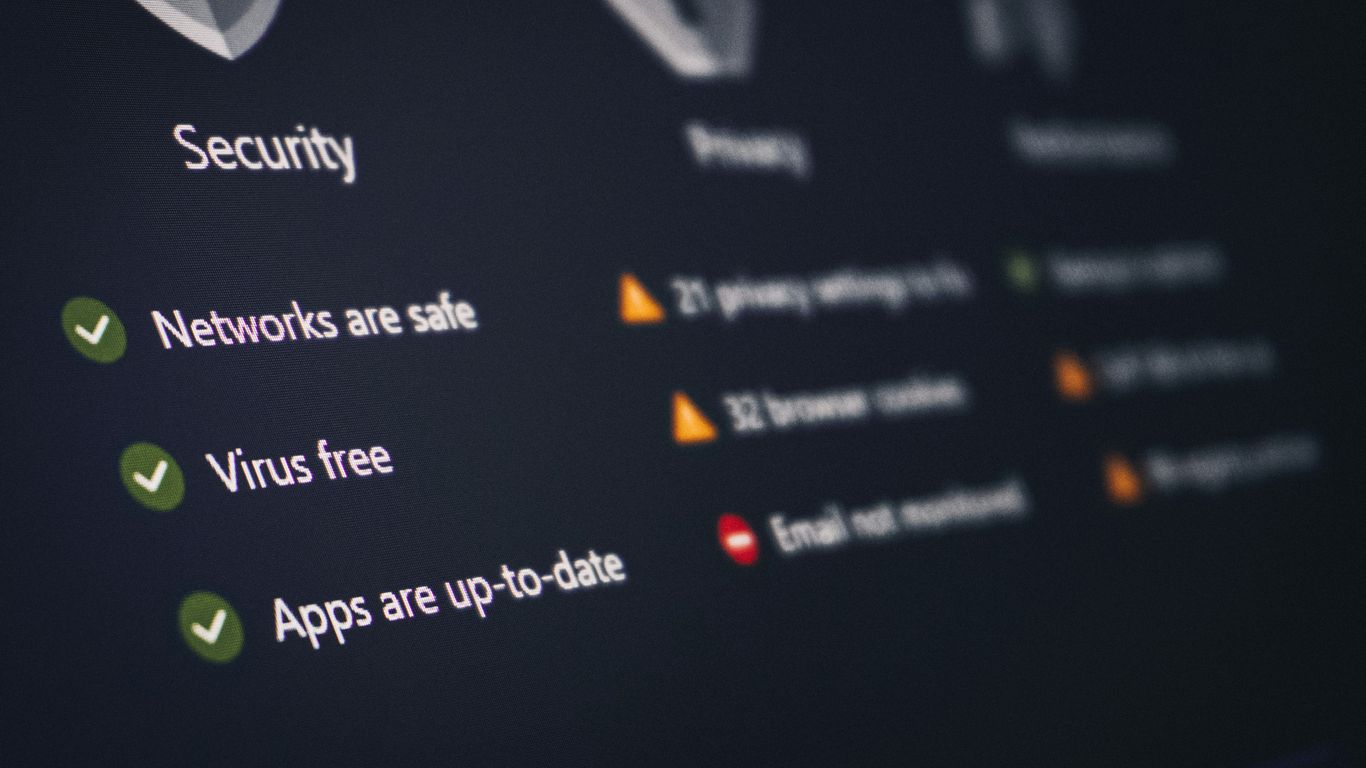
- Technical defenses need to be solid. This means keeping software updated, making sure systems are set up right, and building security into how applications are made. Testing these applications is also a must.
- Cloud and network security are big areas. You need to know how to set up controls in the cloud, use tools that help manage cloud access, and design your network to be secure from the start.
- Making security easy to use and part of the company culture matters. If people can easily report problems and feel supported, they’re more likely to do the right thing. Leadership really sets the tone.
- Keeping up with new threats is non-negotiable. Attackers are always finding new tricks, especially with things like ransomware and AI-powered scams. Your security posture assessment methods need to account for these evolving risks.
Understanding Human Factors in Security
When we talk about security, it’s easy to get caught up in firewalls, encryption, and all the technical stuff. But honestly, a lot of security issues boil down to people. How we act, what we know, and even how we feel can make or break our defenses. It’s about recognizing that the human element isn’t just a weak link; it’s a critical part of the whole security picture.
Security Awareness Programs
These programs are basically about teaching folks what to look out for. Think of it like teaching someone to spot a scam. We cover things like recognizing suspicious emails, keeping passwords safe, and knowing what to do if something seems off. The goal is to make security a normal part of everyone’s day, not just some IT chore. A good program isn’t a one-off lecture; it’s ongoing, and it needs to be relevant to what people actually do at work. We’re trying to build better habits, plain and simple. For instance, a well-designed security awareness program can significantly cut down on accidental breaches.
Social Engineering Susceptibility
This is where attackers play on our natural tendencies – like wanting to be helpful, trusting authority, or feeling rushed. They might pretend to be someone important, or create a sense of urgency to get us to do something we shouldn’t. It’s a bit like a con artist working on your emotions. Some people are naturally more trusting, or maybe they’re just having a busy day and aren’t thinking clearly. The trick is to make people pause and question things, even when they feel pressured. Regular training helps people spot these tactics before they fall for them.
Phishing Behavior Analysis
Phishing is a big one. It’s those fake emails or messages trying to trick you into clicking a bad link or giving up your login details. We look at how people react to these. Do they click the link? Do they report it? Understanding these patterns helps us figure out where our training needs to be stronger. It’s not about blaming individuals, but about seeing where the system or our education might be falling short. We track things like click rates on simulated phishing emails to see if our awareness efforts are actually working.
Insider Threat Behavior Mitigation
Sometimes, the risk comes from within the organization. This isn’t always malicious; it can be accidental, like someone making a mistake or not following procedures. But it can also be intentional. Managing this involves a few key things. First, making sure people only have access to what they absolutely need – that’s the principle of least privilege. Second, having clear processes for when people leave the company to make sure their access is removed promptly. And third, building a culture where people feel comfortable reporting concerns without fear of reprisal. It’s a delicate balance of trust and controls.
Ultimately, technology alone can’t solve security problems. People are involved in almost every step, from making mistakes to being tricked by attackers. Focusing on how humans interact with security systems and processes is just as important as the technology itself.
Implementing Robust Technical Controls
When we talk about security, it’s easy to get lost in the human element – training people, making them aware. And that’s important, no doubt. But you can’t stop there. You’ve got to build a strong technical foundation to back up those efforts. This means putting in place the actual tools and systems that block threats before they even get close to your users or your data.
Patch Management Strategies
Keeping software up-to-date is one of those things that sounds simple but is often a huge headache. Think of it like fixing that leaky faucet; you know you should do it, but life gets in the way. In the tech world, those "leaks" are vulnerabilities that attackers are just waiting to exploit. A solid patch management strategy means you’re not just hoping for the best. It’s about having a plan to find out what needs updating, testing those updates to make sure they don’t break anything important, and then getting them rolled out across your systems quickly. Automation is your friend here; manual patching is slow and prone to mistakes. We need to make sure our systems are protected against known exploits, and that means staying on top of those updates. It’s a continuous cycle, not a one-off task.
Configuration Management Enforcement
This is about making sure your systems are set up the way they’re supposed to be, securely. It’s like building a house with a blueprint; you don’t just wing it. Default settings are often weak, and leaving them as-is is like leaving your front door unlocked. Configuration management means defining what a "secure" setup looks like for your servers, your network devices, your applications – everything. Then, you need to enforce it. This involves setting up baselines and using tools to constantly check if anything has drifted from that secure state. If a setting gets changed accidentally or maliciously, you need to know about it and fix it fast. This helps reduce the chances of attackers finding easy entry points through misconfigurations. It’s a big part of reducing your overall attack surface.
Secure Software Development Practices
If you’re building your own software, security can’t be an afterthought. It needs to be baked in from the very beginning. This means developers need to be thinking about security as they write code, not just when the QA team starts testing. Practices like secure coding standards, regular code reviews where security is a focus, and managing third-party libraries carefully are all part of this. It’s about catching vulnerabilities early in the development lifecycle, when they are much cheaper and easier to fix. Ignoring this is like building a car with a faulty brake system and only finding out when it’s already on the road. We need to integrate security into the entire software lifecycle.
Application Security Testing Methodologies
Even with secure development practices, bugs happen. That’s where application security testing comes in. This isn’t just about finding functional bugs; it’s about actively looking for security flaws. There are different ways to do this, like static analysis (looking at the code without running it), dynamic analysis (testing the running application), and interactive testing. Regularly testing your applications helps you find weaknesses before attackers do. It’s about understanding how your applications might be attacked and making sure they can withstand those attempts. This is a key part of making sure your software is resilient. For example, testing can reveal issues like SQL injection or cross-site scripting vulnerabilities that could lead to serious problems. A good approach involves a mix of automated tools and manual testing to cover different types of flaws. You can find more details on security controls that help in this area.
Technical controls are the backbone of a strong security posture. While human factors are vital, they must be supported by well-implemented and maintained technical safeguards. Neglecting these controls leaves systems vulnerable to exploitation, regardless of user awareness levels. Continuous assessment and adaptation of these controls are necessary to keep pace with evolving threats.
Securing Cloud and Network Environments
When we talk about securing our digital spaces, the cloud and our networks are pretty big pieces of the puzzle. It’s not just about having a firewall anymore; things have gotten way more complex. We need to think about how data moves, who can access what, and how our systems are set up in the first place.
Cloud Security Control Implementation
Cloud environments, while offering flexibility, come with their own set of security challenges. The shared responsibility model means we can’t just assume the cloud provider handles everything. We need to actively implement controls for identity management, monitor configurations closely, and make sure our data is protected. It’s about understanding what’s ours to secure and doing it right. Misconfigurations are a huge reason why cloud breaches happen, so staying on top of settings is key.
Cloud Access Security Broker Utilization
To get a better handle on what’s going on in our cloud services, a Cloud Access Security Broker (CASB) can be a real help. Think of it as a gatekeeper that gives us visibility and control over how cloud apps are being used. It helps enforce our security policies, spots risky behavior, and can even protect sensitive data as it moves around. This is especially useful when employees are using a lot of different cloud tools.
Secure Network Architecture Design
Designing a network with security in mind from the start is way better than trying to bolt it on later. This means thinking about layered defenses, so if one part gets compromised, the whole thing doesn’t fall apart. It also involves segmenting the network, which limits how far an attacker can move if they get in. We’re talking about building a network that’s tough to break into and can bounce back if something bad happens. A well-designed network can significantly reduce the impact of an attack.
Here’s a quick look at some common network security elements:
- Firewalls: These are the basic gatekeepers, controlling traffic based on rules. Modern ones do more than just block ports; they can understand applications.
- Network Segmentation: Dividing the network into smaller, isolated zones. This stops an attacker from easily moving from one part to another.
- Intrusion Detection/Prevention Systems (IDPS): These tools watch network traffic for suspicious activity and can alert you or even block it.
Building a secure network isn’t a one-time project. It requires ongoing attention, regular checks, and adapting to new threats. Ignoring it is like leaving your front door wide open.
When we look at securing our cloud and network environments, it’s clear that a proactive and layered approach is necessary. We need to understand the specific risks associated with cloud services and design our networks to be resilient. This involves not just implementing technical controls but also having clear policies and procedures in place. For organizations looking to better manage their vendor relationships and associated risks, understanding third-party risk management is also a critical component of a robust security posture.
Enhancing Security Usability and Culture
Making security work for people, not against them, is a big part of the puzzle. When security tools and processes are hard to use, people tend to find ways around them. This often creates more risk than it solves. We need to think about how people actually interact with security measures day-to-day.
Reporting Security Incidents Effectively
Getting people to report suspicious activity quickly is key. If reporting is complicated or if people fear getting in trouble, they’ll hesitate. A simple, clear process encourages timely notifications, which can significantly limit the damage from an incident. It’s about making it easy and safe to speak up.
- Establish clear, accessible reporting channels.
- Provide regular training on what and how to report.
- Acknowledge and act on reports promptly.
- Avoid blaming individuals for reporting genuine concerns.
Managing Change Resistance
Introducing new security measures often meets resistance. People are used to their routines, and change can be disruptive. To overcome this, clear communication about why changes are necessary is important. Showing how new controls benefit everyone, not just the security team, can help. Leadership support also plays a big role in getting people on board.
| Change Initiative | Initial Resistance Level | Adoption Rate (Post-Training) |
|---|---|---|
| New Password Policy | High | 75% |
| MFA Rollout | Medium | 88% |
| Phishing Simulation | Low | 92% |
| Data Handling Update | Medium | 80% |
Fostering Ethical Decision-Making
Security isn’t just about rules; it’s about making the right choices, especially when things aren’t black and white. Training that focuses on ethical scenarios helps employees understand the impact of their decisions. This builds a stronger sense of responsibility. When people understand the ‘why’ behind security policies, they’re more likely to act ethically. This is especially important when dealing with sensitive data, like personal information that needs careful handling privacy and data governance.
Ethical decision-making in security means considering the potential harm to individuals and the organization. It requires a clear understanding of policies and a commitment to doing the right thing, even when it’s difficult.
Leadership Influence on Security Culture
Leaders set the tone for the entire organization. When leaders visibly prioritize security and follow the rules themselves, it sends a powerful message. Their actions speak louder than any policy document. This commitment helps build a culture where security is seen as everyone’s job, not just an IT problem. It makes security a normal part of how business gets done.
Addressing Evolving Cybersecurity Trends
The digital world doesn’t stand still, and neither do the folks trying to break into it. We’re seeing attackers get smarter, faster, and frankly, more creative. It’s not just about random hackers anymore; we’re dealing with organized groups who are really good at what they do. They’re using new tools and techniques all the time, which means we have to keep up.
Threat Evolution and Actor Sophistication
Attackers are getting more organized. Think less lone wolf, more well-funded operation. They’re automating a lot of their work, which lets them launch more attacks. They’re also combining different methods, like tricking people with social engineering and then using stolen login details. It’s a multi-pronged approach that can be tough to defend against. Understanding these evolving risks is key for any business, as they’re not just IT problems anymore. They can shut down operations and cost a lot of money. It’s important to get a handle on how cyber risk impacts your business.
Ransomware Evolution and Tactics
Ransomware used to just lock up your files. Now, it’s a lot more complicated. Attackers might encrypt your data and threaten to leak it if you don’t pay. Sometimes, they’ll even hit you a third time, maybe by disrupting your operations directly. This ‘double’ or ‘triple’ extortion makes paying up seem more appealing, but it’s a dangerous game. Defense strategies have to focus on having solid backups and making sure your systems can bounce back quickly.
AI-Driven Social Engineering
Artificial intelligence is changing the game for social engineering. Imagine getting an email or even a voice message that sounds exactly like someone you know, perfectly mimicking their tone and style. AI can create highly personalized phishing attempts that are much harder to spot. This makes human vulnerability an even bigger target. We need to be extra careful about what we click on and what information we share, even if it seems to come from a trusted source. It’s a constant battle to stay ahead of these new methods.
Mastering Incident Detection and Response
When a security incident happens, knowing it’s happening and what to do next is super important. It’s not just about having fancy tools; it’s about having a plan and people who know how to use it. This section looks at how we get good at spotting trouble and then dealing with it before it gets too bad.
Security Awareness Training Effectiveness
We talk a lot about training users to spot phishing emails or not click on weird links. But how do we actually know if that training is working? It’s more than just checking a box. We need to see if people are actually changing their behavior. This means looking at things like how often users report suspicious emails, or if phishing simulation results get better over time. If people are still falling for the same old tricks, the training isn’t hitting the mark. We need to adjust our approach, maybe make it more hands-on or focus on specific risks that are actually happening to us. It’s about making sure the training sticks and makes a real difference in how people act when faced with a threat.
Incident Detection Mechanisms
Spotting an incident is the first hurdle. This involves a lot of watching what’s going on across our systems and networks. We’re talking about logs from servers, network traffic, and even what users are doing. Tools like SIEM systems help pull all this data together, looking for patterns that don’t look right. But it’s not all automated. Sometimes, a human needs to look at an alert and decide if it’s a real problem or just noise. The goal is to catch things early, when they’re small, so they don’t turn into a big mess. Weak monitoring allows insider threats to escalate unnoticed. Insiders can conduct reconnaissance or prepare for significant actions without raising flags due to a lack of visibility. To prevent this, implement robust logging on critical systems, regularly audit log data for anomalies, and consistently enforce security controls across the entire environment. robust logging
Incident Triage and Prioritization
Once we detect something, we get a flood of alerts. Not all of them are emergencies. Triage is about sorting through these alerts quickly to figure out what’s most important. Is it a minor glitch or a full-blown attack that could bring everything down? We need to prioritize based on how bad it could be and how likely it is to be a real threat. Getting this wrong means we might waste time on fake alarms or, worse, ignore something serious. A good triage process helps the security team focus their energy where it’s needed most.
Incident Containment and Eradication
If we find a real problem, the next step is to stop it from spreading. This is containment. Think of it like putting out a small fire before it engulfs the building. We might disconnect a compromised computer from the network or disable a user account that’s been taken over. The tricky part is doing this fast enough without breaking essential business operations. After we’ve contained it, we need to get rid of the cause. Eradication means removing the malware, fixing the vulnerability, or whatever allowed the attacker in. If we don’t fully remove the threat, it can come back. Effective cyber crisis management requires comprehensive incident response capabilities. This involves establishing clear roles, escalation paths, and communication protocols. Key steps include early incident identification, validation, and containment to limit damage. Following containment, eradication of the threat, fixing the root cause, and remediation to restore systems are crucial. Addressing third-party risks and ensuring rapid, coordinated action are vital for minimizing impact and preventing future attacks. coordinated action
Here’s a quick look at the incident response steps:
- Detection: Spotting the suspicious activity.
- Containment: Stopping the spread of the incident.
- Eradication: Removing the root cause of the problem.
- Recovery: Getting systems back to normal.
- Review: Learning from what happened to get better next time.
Designing Resilient Systems and Architectures
Building systems that can bounce back after something goes wrong is a big deal in security. It’s not just about stopping attacks before they happen, but also about having a plan for when they do. Think of it like building a house that can withstand an earthquake – you want it to stand, or at least be repairable, after the shaking stops.
Secure Development and Application Architecture
This is about baking security into software right from the start. Instead of trying to bolt it on later, we build it in. This means thinking about potential threats while we’re still designing the application and writing the code. It’s a lot easier to fix a problem when it’s just an idea on paper than when it’s live and causing trouble. We look at things like how data flows, who can access what, and what could go wrong at each step. This approach helps reduce the chances of vulnerabilities making it into the final product. It’s about making sure the software itself is strong.
Cryptography and Key Management
Cryptography is what keeps our data secret and makes sure it hasn’t been messed with. But it’s only as good as the keys used to lock and unlock it. Managing these keys is super important. We need to make sure they are created safely, shared only with those who need them, changed regularly, and properly gotten rid of when they’re no longer needed. If key management is weak, all the fancy encryption in the world won’t help much. It’s like having a super strong lock but leaving the key under the doormat.
Cloud and Virtualization Security
When we move things to the cloud or use virtual machines, we get a lot of flexibility, but also new security challenges. We need to make sure that different users and applications in the cloud can’t see or mess with each other’s stuff. This involves setting up controls correctly and keeping an eye on how things are configured. A common problem is misconfiguration, where settings are left open that shouldn’t be. We also need to think about securing the virtual environments themselves, like containers, to prevent attackers from jumping between them. It’s about keeping things separate and secure in a shared space.
Security Telemetry and Monitoring
This is all about collecting information from our systems – logs, network traffic, user actions – and putting it together. The goal is to spot unusual patterns that might mean something bad is happening. If we can see what’s going on, we can react faster. It’s like having a security camera system for your entire digital environment. The more data we collect and the better we are at analyzing it, the quicker we can find and deal with threats. Visibility is key to knowing if you’re under attack.
Here’s a quick look at what we collect:
| Data Source | Purpose |
|---|---|
| System Logs | Records events on servers and workstations |
| Network Traffic | Monitors data flow between systems |
| Application Logs | Tracks user activity within applications |
| Authentication Logs | Records login attempts and access grants |
| Endpoint Activity | Monitors actions on user devices |
The ability to detect a security incident is directly tied to the quality and breadth of the telemetry we gather. Without good data, detection becomes a guessing game, and response times suffer significantly.
Establishing Governance and Compliance Frameworks
Setting up solid governance and compliance frameworks is like building the rules of the road for your security. Without them, things can get pretty chaotic, especially when you’re dealing with a lot of different systems and people. It’s all about making sure everyone knows what they’re supposed to do, how they’re supposed to do it, and why it matters.
Incident Response Governance
When a security incident happens, you don’t want to be figuring out who’s in charge or how to talk to people on the fly. Incident response governance lays out the plan. This means defining clear roles, like who makes the big decisions and who handles the technical cleanup. It also sets up communication channels so everyone stays informed, from the IT team to the executive suite. Having this structure in place, as outlined in a good incident response governance framework, helps keep things orderly and accountable during a stressful event.
Crisis Management and Disclosure
Beyond just fixing the immediate problem, you need a plan for what happens next. This covers how you’ll manage the broader crisis and what you’ll tell people. If sensitive data is involved, there are often legal and regulatory requirements for disclosure. A well-thought-out plan helps manage reputational damage and ensures you meet those obligations. It’s about being transparent when you need to be, but also strategic about how you communicate.
Business Continuity and Disaster Recovery
Security incidents can sometimes shut down operations. Business continuity planning is about keeping the lights on, even when things go wrong. Disaster recovery focuses specifically on getting your systems back up and running after a major disruption. These plans aren’t just about technology; they involve people, processes, and facilities too. Regularly testing these plans is key to making sure they actually work when you need them.
Security Metrics and Monitoring
How do you know if your security efforts are actually working? That’s where metrics come in. You need ways to measure both how well your security is performing day-to-day and what your actual risk exposure looks like. These numbers help you see where you’re strong and where you need to improve. They also provide a way to report progress to leadership, showing that security isn’t just an IT problem, but a business concern. Good monitoring provides the data needed for these metrics.
Here’s a look at some common areas these frameworks cover:
- Policy Development: Creating clear, understandable security policies that everyone can follow.
- Risk Assessment: Regularly identifying and evaluating potential threats and vulnerabilities.
- Control Implementation: Putting the right technical and procedural safeguards in place.
- Auditing and Testing: Verifying that controls are working as intended.
- Training and Awareness: Making sure employees understand their role in security.
Governance and compliance aren’t just about checking boxes. They’re about building a security program that’s aligned with the business, adaptable to new threats, and understood by everyone involved. It’s an ongoing effort, not a one-time project.
Foundational Cybersecurity Architecture
Building a solid cybersecurity foundation is like laying the groundwork for a secure building. You can’t just start putting up walls; you need a strong base. This means thinking about how everything fits together from the start, not as an afterthought. It’s about creating a structure that’s inherently resistant to problems and easy to manage.
Enterprise Security Architecture
This is the big picture, the blueprint for how security works across your entire organization. It’s not just about firewalls and antivirus; it’s about making sure your security measures actually support what your business is trying to do. Think of it as aligning your security strategy with your business goals. It involves putting different security tools and processes in place at various levels – like on your networks, with your employees’ devices, in your applications, and for your data. The goal is to have a coordinated defense that makes sense for your specific risks and how much risk you’re willing to accept.
Defense Layering and Segmentation
This is where we get into the "defense in depth" idea. Instead of relying on one big security gate, you put up multiple layers of protection. If one layer fails, others are still there. Network segmentation is a big part of this. It means dividing your network into smaller, isolated zones. If one part gets compromised, it’s much harder for an attacker to move around and access other areas. This limits the damage, or "blast radius," of any security incident. It’s like having bulkheads on a ship; if one compartment floods, the whole ship doesn’t sink.
Identity-Centric Security Models
In today’s world, we can’t just assume everything inside our network is safe. The old idea of a strong perimeter with a weak inside is outdated. Modern security models focus more on identity. Who is trying to access what? We need to verify identities rigorously, not just once, but continuously. This involves things like multi-factor authentication and making sure that even if an account is compromised, the damage is limited. Identity is really becoming the new security perimeter. Identity and Access Management systems are key here.
Access Governance and Privilege Management
Once we know who someone is, we need to control what they can do. This is where access governance comes in. The principle of "least privilege" is super important: people should only have access to the absolute minimum they need to do their job, and nothing more. Giving too much access, or "over-permissioning," is a common mistake that attackers love to exploit. It makes it easier for them to move around your network if they get in. Privilege management systems help keep track of and control who has elevated access, like administrator rights, and make sure it’s used appropriately and only when needed.
Managing Cyber Risk and Compliance
Dealing with cyber risk and making sure we’re following all the rules can feel like a constant juggling act. It’s not just about having the latest tech; it’s about understanding what could go wrong and having a plan. We need to figure out what’s most important to protect and what threats are actually likely to hit us. This isn’t a one-and-done thing, either. The landscape changes so fast, what was a big worry last year might be less of a concern now, and new risks pop up all the time.
Risk Quantification and Prioritization
First off, we have to get a handle on what our actual risks are. This means looking at our systems, our data, and our processes to see where the weak spots are. Then, we need to think about what would happen if those spots got hit. Would it just be a minor inconvenience, or could it shut down the whole operation? Quantifying these risks helps us decide where to put our limited resources. We can’t fix everything at once, so we have to prioritize. This often involves looking at the likelihood of an event happening and the potential impact it would have. It’s about making smart choices based on data, not just gut feelings.
Here’s a quick look at how we might break down risk assessment:
| Risk Area | Likelihood (Low/Med/High) | Impact (Low/Med/High) | Priority (1-5) |
|---|---|---|---|
| Unpatched Servers | High | High | 1 |
| Phishing Attacks | High | Medium | 2 |
| Insider Data Theft | Low | High | 3 |
| DDoS Attack | Medium | Medium | 4 |
| Cloud Misconfig. | Medium | High | 1 |
Security Governance Frameworks
Once we know what we’re up against, we need a solid structure to manage it. This is where security governance comes in. Think of it as the rulebook and the decision-making process for our security efforts. It defines who is responsible for what, how decisions get made, and how we make sure everyone is on the same page. A good governance framework aligns our security goals with the overall business objectives. It’s not just an IT problem; it’s a business problem. We need clear policies and procedures that everyone can understand and follow. This also helps us when we need to show that we’re taking security seriously, which is where compliance comes in.
Key elements of security governance include:
- Defining clear roles and responsibilities.
- Establishing risk tolerance levels.
- Setting security policies and standards.
- Ensuring regular audits and assessments.
- Integrating security into overall enterprise risk management.
Compliance and Regulatory Requirements
Staying compliant with all the relevant laws and regulations is non-negotiable. Depending on our industry and where we operate, there are different rules we have to follow, like GDPR for data privacy or HIPAA for health information. These aren’t just suggestions; they come with real penalties if we don’t meet them. Compliance often means having specific controls in place, documenting everything, and being ready for audits. It’s a lot of paperwork, sure, but it’s also about protecting our customers and our reputation. We need to keep a close eye on changes in the regulatory landscape because what’s required today might be different tomorrow. Staying on top of these requirements is a big part of managing our overall cyber risk. You can find more information on security operations governance.
Compliance is a baseline, not the ceiling. Meeting regulatory requirements is necessary, but it doesn’t automatically mean an organization is secure. True security requires going beyond minimum standards to address specific threats and vulnerabilities relevant to the business.
Cyber Insurance and Risk Transfer
Sometimes, even with the best controls and plans, things can still go wrong. That’s where cyber insurance can play a role. It’s not a magic bullet, but it can help transfer some of the financial burden of a major incident. This could cover costs like incident response, legal fees, or business interruption. However, insurance companies are getting smarter. They often require us to demonstrate a certain level of security maturity before they’ll offer coverage, and even then, the policies have limits and exclusions. So, while it’s a piece of the puzzle, it doesn’t replace the need for strong internal security practices. It’s more about having a safety net for the risks we can’t fully eliminate.
Core System Architecture and Data Control
When we talk about the guts of our digital defenses, we’re really looking at how systems are built and how data is handled. It’s not just about firewalls; it’s about the foundational design that keeps things secure from the ground up. Think of it like building a house – you need a solid foundation, strong walls, and secure locks on the doors and windows. If any of those are weak, the whole place is at risk.
Security as Boundary Control
This is all about setting clear lines for who and what can get in, or access certain information. We define boundaries for identities (who are you?), networks (where are you connecting from?), and data itself (what can you see or do?). The idea is to get away from just trusting things because they’re ‘inside’ the network. Every interaction needs to be checked.
Identity and Access Governance
This is where we manage who people are and what they’re allowed to do. It involves making sure someone is who they say they are (authentication) and then giving them only the access they need (authorization). If your identity systems are shaky, it’s like leaving the front door wide open for attackers. Using things like multi-factor authentication is a big step in the right direction. It’s a foundational control for modern security programs. Identity and access management governs user identities, credentials, and permissions.
Least Privilege and Access Minimization
This principle is pretty straightforward: give people and systems only the access they absolutely need to do their job, and nothing more. If someone has access to way more than they need, it just creates more opportunities for mistakes or for an attacker to move around if they get that person’s account. Providing access only when it’s needed, like for a specific task, helps cut down on those standing privileges.
Data Classification and Control
Not all data is created equal. We need to sort our data based on how sensitive it is. Is it public information, or is it highly confidential customer data? Once classified, we can put the right controls in place, like access restrictions or encryption. This helps make sure we’re protecting the most important stuff with the most robust measures.
Here’s a quick look at how data classification might work:
| Classification Level | Description |
|---|---|
| Public | Information intended for public release. |
| Internal Use Only | Information for internal company use. |
| Confidential | Sensitive information requiring protection. |
| Restricted | Highly sensitive, legally protected data. |
Proper data classification is the first step in effective data protection. Without knowing what you have, you can’t protect it properly. This means understanding where sensitive information lives and who should have access to it.
Vulnerability Management and Testing
Keeping systems and software secure means we have to constantly look for weak spots. It’s like checking your house for unlocked windows or doors before you go to bed. Vulnerability management is basically that process, but for computers and networks. It’s not a one-and-done thing; it’s something you have to do regularly because new weaknesses pop up all the time. Attackers are always looking for these flaws, so we need to find and fix them before they do.
Vulnerability Identification and Assessment
First off, we need to know what we have. This means keeping an accurate list of all your systems, applications, and devices. Once you know what’s out there, you can start scanning it for known issues. Tools can help with this, looking for things like unpatched software or misconfigurations. It’s a bit like a doctor giving you a check-up, looking for any signs of trouble. The goal here is to get a clear picture of where the potential problems lie. We’re trying to map out the attack surface so we know what needs attention.
Penetration Testing Methodologies
Scanning is good, but sometimes you need to see if someone can actually break in. That’s where penetration testing comes in. Think of it as hiring a security expert to try and break into your systems, just like a real attacker would. They use various techniques to find ways in, testing your defenses. This isn’t just about finding flaws; it’s about understanding how an attacker might chain different weaknesses together to achieve their goals. Different methods exist, from trying to guess passwords to exploiting specific software bugs.
Risk Management and Mitigation Strategies
Once we find vulnerabilities, we can’t fix everything at once. We have to figure out which ones are the most dangerous. This involves looking at how likely it is that a vulnerability will be exploited and what kind of damage it could cause. A small issue on a non-critical system might be less urgent than a major flaw on a server holding sensitive customer data. Based on this risk assessment, we decide how to handle it. Options include fixing it right away (mitigation), accepting the risk if it’s low, or sometimes transferring the risk, perhaps through insurance.
Here’s a look at how we might prioritize risks:
| Risk Level | Likelihood | Impact | Action | Example |
|---|---|---|---|---|
| Critical | High | High | Immediate Remediation | Unpatched critical server with known exploit |
| High | High | Medium | Prioritized Remediation | Misconfigured firewall rule |
| Medium | Medium | Medium | Scheduled Remediation | Outdated but not actively exploited software |
| Low | Low | Low | Monitor or Accept | Minor configuration deviation on non-sensitive system |
Measuring Security Performance
How do we know if our vulnerability management efforts are actually working? We need to measure it. This means tracking things like how quickly we find and fix vulnerabilities, how many critical vulnerabilities are outstanding, and how often our penetration tests find the same issues. These metrics help us see if our processes are effective and where we need to make improvements. It’s about making sure our security posture is actually getting stronger over time, not just staying the same.
It’s easy to get caught up in the technical details of scanning and patching, but the real goal is to reduce the chances of a successful attack. This requires a consistent effort, not just a one-off project. We need to treat it like ongoing maintenance for our digital house.
Wrapping Up Your Security Assessment
So, we’ve talked a lot about how to check up on your security. It’s not just about the fancy tech, though that’s a big part of it. We also looked at how people mess things up, sometimes without even meaning to, like clicking on a bad link or not updating software. Things like regular training, making sure people know what to do, and having clear rules really help. It’s like keeping your house tidy – you have to do it regularly, not just once. Remember, security isn’t a one-and-done deal. It’s an ongoing thing, always changing as new threats pop up. Staying on top of it means checking in often, fixing what’s broken, and making sure everyone’s on the same page. That’s how you build a stronger defense.
Frequently Asked Questions
What is a security posture and why is it important?
Think of your security posture like the overall health of your digital defenses. It’s how well your systems and data are protected against online threats. Keeping it strong is super important because it helps prevent bad guys from stealing your information or messing up your computer systems.
How do people affect cybersecurity?
People are a big part of cybersecurity! Sometimes, people make mistakes that open the door for attackers, like clicking on a bad link or using a weak password. That’s why learning about online safety and being careful is key to staying secure.
What is a ‘phishing’ attack?
Phishing is like a trick where scammers pretend to be someone trustworthy, like a bank or a popular website, to get you to share secret information like your passwords or credit card numbers. They often send fake emails or messages to fool you.
Why is keeping software updated so important?
Software updates, often called ‘patches,’ fix security holes that attackers could use to get into your systems. It’s like fixing a broken window in your house before a burglar can climb through it. Keeping things updated is a simple but powerful way to stay safe.
What does ‘least privilege’ mean in security?
The ‘least privilege’ idea means giving people and computer programs only the access they absolutely need to do their job, and nothing more. This way, if an account gets hacked, the attacker can’t do as much damage because they won’t have access to everything.
How can companies protect their information in the cloud?
Protecting data in the cloud involves using special security tools and settings, like making sure only the right people can access the data. It’s also about setting up strong security rules for cloud services and keeping an eye on who is accessing what.
What happens when a security incident occurs?
When a security incident happens, like a computer virus or a data breach, the first step is to find out what’s going on. Then, teams work quickly to stop the problem from spreading, fix it, and get everything back to normal, while also learning how to prevent it from happening again.
How does a company’s culture impact its security?
A company’s culture is like its personality. If a company values security and everyone takes it seriously, from the boss to the newest employee, it creates a much safer environment. When security is a team effort, it’s much harder for attackers to succeed.
