When we talk about keeping our digital stuff safe, there’s a lot that goes into it. It’s not just about having a strong password, though that’s part of it. We’re talking about a whole bunch of different checks and tests to make sure everything is as secure as it can be. This whole process, the security assurance testing, is like giving your systems a thorough check-up to find any weak spots before the bad guys do. It covers everything from how apps are built to how people use them, and even how we react when something does go wrong.
Key Takeaways
- Security assurance testing is a broad field that involves many different methods to find weaknesses in systems and applications.
- Testing covers the entire lifecycle, from how software is developed to how users interact with systems.
- Regular testing, like vulnerability scanning and penetration testing, is vital for staying ahead of threats.
- Focusing on principles like least privilege and defense-in-depth helps build more resilient systems.
- Human factors and user awareness are just as important as technical controls in maintaining security.
Principles of Security Assurance Testing
Security assurance testing isn’t just about finding bugs; it’s about making sure our systems and data are actually protected. It’s built on a few core ideas that guide how we approach testing and build defenses. Think of it like building a house – you don’t just slap walls up, you think about where the doors and windows go, who has keys, and how to stop someone from just walking in.
Trust Boundaries and Authorization
This is all about defining who or what is allowed to interact with different parts of your system. We draw lines, or ‘boundaries,’ around sensitive areas. When something tries to cross one of these lines, it needs to prove it’s allowed. This means strong authentication (proving who you are) and then authorization (proving what you’re allowed to do). Without clear boundaries, an attacker who gets into one part of the system might be able to access everything else too easily. It’s about making sure that just because someone can access the front door, doesn’t mean they can walk into the master bedroom.
- Verify identity at every boundary.
- Implement strict authorization checks for all resource access.
- Regularly review and update access control lists.
Least Privilege Enforcement
This principle is pretty straightforward: give users and systems only the minimum access they need to do their jobs, and nothing more. If an account only needs to read data, it shouldn’t have permission to delete it. This limits the damage an attacker can do if they manage to compromise an account. It also makes it harder for attackers to move around within the system once they’re in. Imagine giving a temporary contractor access to only one specific room in a building, rather than the whole floor.
Over-permissioning is a common mistake that significantly widens the attack surface and enables attackers to move laterally within a network more easily.
- Grant permissions based on job function, not convenience.
- Use just-in-time (JIT) access for elevated privileges.
- Regularly audit permissions to remove unnecessary access.
Defense-in-Depth Approaches
This is the idea of having multiple layers of security, so if one layer fails, others are still in place. It’s like wearing a belt and suspenders. You might have a firewall at the network edge, then intrusion detection systems, then access controls on servers, and finally, application-level security. Each layer adds a hurdle for an attacker. The goal is to make it as difficult and time-consuming as possible for an attacker to succeed. This approach acknowledges that no single security control is perfect. You can explore different security frameworks that guide this layered approach.
| Security Layer | Example Controls |
|---|---|
| Network | Firewalls, Intrusion Detection Systems (IDS) |
| Endpoint | Antivirus, Endpoint Detection and Response (EDR) |
| Application | Web Application Firewalls (WAF), Input Validation |
| Data | Encryption (at rest and in transit), Access Controls |
| Identity | Multi-Factor Authentication (MFA), Role-Based Access |
Vulnerability Management and Assessment
Keeping your systems secure means you’ve got to know where the weak spots are. That’s where vulnerability management and assessment come in. It’s not a one-and-done thing; it’s an ongoing process. You’re basically looking for holes in your defenses before the bad guys do.
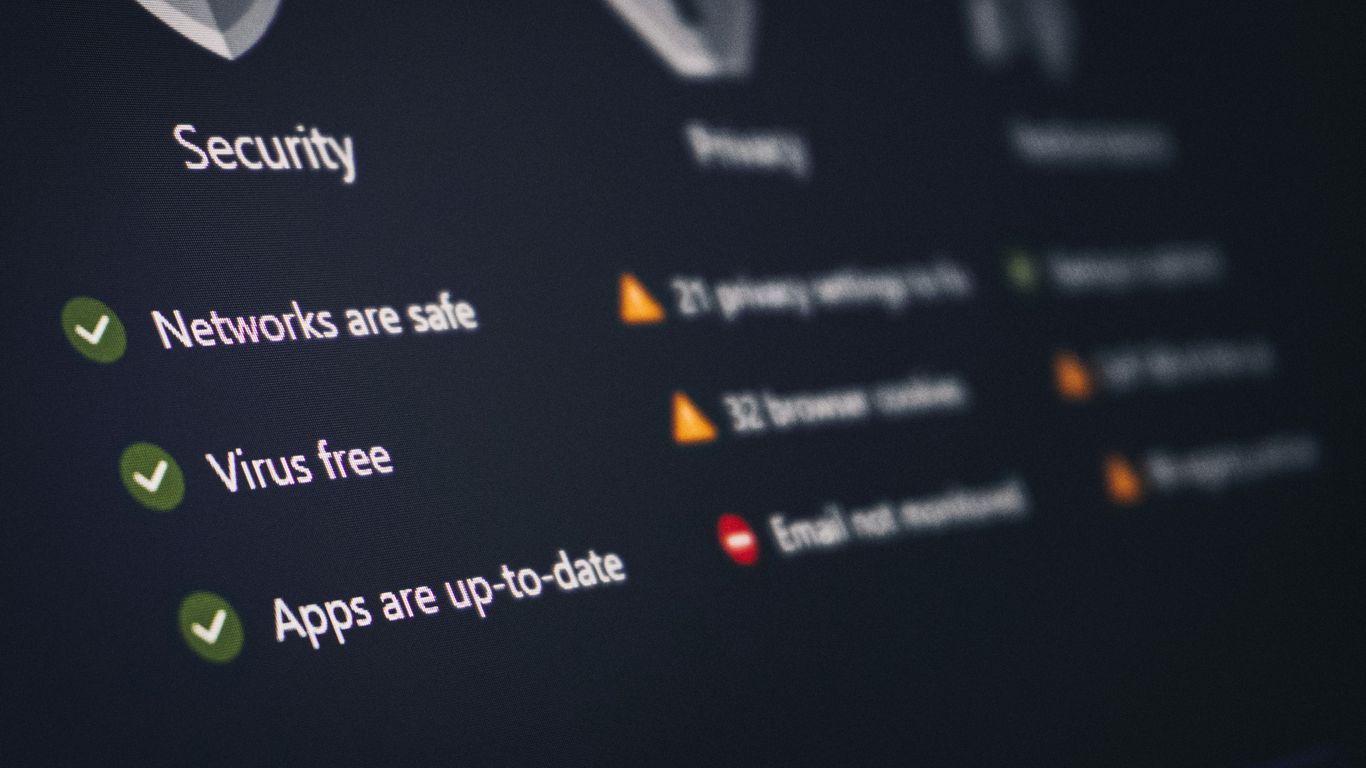
Automated Vulnerability Scanning
This is your first line of defense. Automated scanners are tools that poke around your network and applications, looking for known weaknesses. Think of it like a regular check-up for your IT infrastructure. They can spot things like outdated software, missing security patches, or common misconfigurations. The trick is to run these scans regularly, not just once in a while. This helps you catch issues early, before they become big problems. It’s a pretty standard practice for most organizations these days, and there are tons of tools out there to help you get started with scanning.
Patch Management Practices
Once you find a vulnerability, you need to fix it, right? That’s where patch management comes in. Patches are essentially updates released by software vendors to fix bugs and security flaws. A solid patch management process means you’re applying these updates promptly. This isn’t just about ticking a box; it’s about actively reducing your attack surface. Delays in patching are a common way attackers get in, so having a system for testing and deploying patches efficiently is key. It often involves:
- Identifying all your assets and the software they run.
- Testing patches in a non-production environment first.
- Deploying approved patches across your systems on a schedule.
- Verifying that patches were applied successfully.
Continuous Remediation Techniques
Finding vulnerabilities is one thing, but fixing them all can be a challenge. Continuous remediation is about making the fixing process as smooth and ongoing as the scanning. This means not just patching, but also reconfiguring systems, updating access controls, or even decommissioning old software that can’t be patched. It’s about having a plan to address the findings from your scans and assessments in a structured way. Sometimes, you might not be able to fix a vulnerability immediately. In those cases, you’ll need to implement compensating controls to reduce the risk until a permanent fix is possible. This whole cycle of finding, assessing, and fixing is what helps you stay ahead of threats and maintain a strong security posture. It’s a core part of effective risk management.
Penetration Testing and Red Team Exercises
When we talk about really digging into how secure our systems are, penetration testing and red team exercises are where the rubber meets the road. These aren’t just about finding a few bugs; they’re about simulating real-world attacks to see how well our defenses actually hold up. Think of it like a controlled invasion to test your castle’s walls, gates, and guards.
Simulating Realistic Attack Scenarios
This is where we get creative. Instead of just running automated scans, we’re trying to think like an attacker. This could involve anything from trying to trick an employee into clicking a bad link – a classic social engineering tactic – to finding a way into the network through an overlooked vulnerability. The goal is to mimic the steps a real adversary might take, from the initial reconnaissance, where attackers probe technical systems for weaknesses, all the way through to achieving their objective. We’re looking for those unexpected ways in, the ones that standard security tools might miss. It’s about understanding the full attack surface.
Evaluating Detection and Response
Finding a vulnerability is one thing, but how quickly do we notice it? And once we do, how effective is our response? Penetration tests and red team exercises are fantastic for this. We can see if our security monitoring systems are flagging suspicious activity, if our alerts are getting to the right people, and if those people know what to do next. It’s a test of our entire security operations center (SOC) and incident response team. We want to know if our detection and response capabilities are up to snuff. A key part of this is understanding how long it takes to detect an intrusion, which is often measured in days or even weeks if things aren’t configured correctly.
| Metric | Target Time | Actual Time (Example) |
|---|---|---|
| Detection Time | < 24 hours | 72 hours |
| Containment Time | < 4 hours | 12 hours |
| Eradication Time | < 8 hours | 24 hours |
| Recovery Time | < 48 hours | 36 hours |
Reporting and Prioritizing Findings
After the exercise, we get a detailed report. This isn’t just a list of "what went wrong." It’s a narrative of the attack, highlighting the specific paths taken, the vulnerabilities exploited, and the impact achieved. More importantly, it helps us prioritize what needs fixing first. Some findings might be critical, like gaining administrative access, while others might be less severe. We use this information to make smart decisions about where to invest our time and resources to improve our security posture. It’s about making sure we’re fixing the most important things before they can be exploited by actual attackers. This kind of testing is vital for validating controls and ensuring that our security investments are effective. For more on how attackers gather information, you can look into spear phishing reconnaissance.
The effectiveness of these exercises hinges on their realism and the thoroughness of the post-exercise analysis. Without clear objectives and a structured approach to reporting, the value can be diminished. It’s not just about breaking things; it’s about learning how to build them back stronger.
Application Security Testing Methods
When we talk about keeping our software safe, application security testing is a big piece of the puzzle. It’s all about finding weaknesses in the code before the bad guys do. Think of it like checking your house for unlocked windows and doors before you leave for vacation. There are a few main ways we do this, and they all have their own strengths.
Static Application Security Testing (SAST)
SAST tools look at your application’s source code, byte code, or binary code without actually running the application. It’s like a proofreader for your code, scanning for known patterns that indicate security flaws. This method is great because it can find vulnerabilities early in the development cycle, sometimes even as developers are writing the code. This means you can fix issues before they ever make it into a deployed product. Some common issues SAST can spot include SQL injection flaws and cross-site scripting vulnerabilities.
- Early detection of vulnerabilities
- Identifies flaws in source code
- Supports secure coding practices
Dynamic Application Security Testing (DAST)
DAST, on the other hand, tests the application while it’s running. It acts like an automated attacker, sending various inputs and requests to the application to see how it responds. This approach is really good at finding runtime vulnerabilities, like issues with authentication or session management, that SAST might miss because it’s not executing the code. It simulates how a real attacker might interact with your web application.
- Tests running applications
- Simulates external attacks
- Identifies runtime vulnerabilities
Interactive Application Security Testing (IAST)
IAST tries to combine the best of both worlds. It uses agents or instrumentation within the running application to monitor its behavior from the inside. As the application runs, the IAST tool observes the code execution and data flow, identifying vulnerabilities in real-time. This can provide more accurate results than DAST alone and can pinpoint the exact line of code causing the problem, making remediation quicker. It’s a more modern approach that’s gaining traction.
IAST offers a middle ground, providing insights into how code behaves during execution while also pinpointing specific code locations for fixes. This can significantly speed up the remediation process compared to methods that only identify the vulnerable endpoint.
- Combines SAST and DAST benefits
- Monitors application behavior internally
- Provides real-time feedback and code-level detail
Each of these methods plays a role in building more secure applications. Using a combination of SAST, DAST, and IAST gives you a much better picture of your application’s security posture and helps you address potential risks before they become major problems. It’s all part of a larger effort to assess security posture effectively.
Identity and Access Controls Evaluation

Evaluating identity and access controls is a big part of making sure systems are secure. It’s all about checking who can get into what and making sure they should be able to. We’re not just talking about passwords here; it’s a whole system of checks and balances.
Multi-Factor Authentication Verification
This is a pretty standard check these days, but it’s still super important. We look at how multi-factor authentication (MFA) is set up and if it’s actually working as intended. This means checking if users are being prompted for that second factor – like a code from their phone or a fingerprint scan – after they enter their password. We also check for common bypass methods, like MFA fatigue attacks where attackers try to overwhelm users with login requests. Strong MFA is one of the best ways to stop unauthorized access from stolen credentials. It’s a foundational control for modern security programs, and we need to make sure it’s implemented correctly. You can find more on how MFA works and its benefits here.
Access Reviews and Privilege Management
This is where we get into the nitty-gritty of who has access to what. We review user permissions to make sure they follow the principle of least privilege. That means people only have access to the systems and data they absolutely need to do their jobs, and nothing more. Overly broad permissions are a huge risk, as they can allow attackers to move around a network easily if they compromise an account. We also look at how access is granted and revoked, especially for privileged accounts. Things like just-in-time access, where permissions are granted only for a limited time, are good practices to check for. Regular access reviews are key to catching any outdated or excessive permissions.
Credential and Session Security
This section focuses on how user credentials, like passwords and API keys, are handled and protected. We check if credentials are stored securely, if they’re rotated regularly, and if there are audits in place to track their usage. Secrets management is a big deal here; if an attacker gets hold of credentials, it can lead to a full system compromise. We also look at session management. This includes how user sessions are established, maintained, and terminated. Things like session timeouts and preventing session hijacking are important checks. A table summarizing common threats and prevention methods might look like this:
| Threat Category | Common Threats | Prevention Methods |
|---|---|---|
| Credential Compromise | Stolen passwords, weak authentication | MFA, strong password policies, credential rotation, secrets management |
| Session Hijacking | Cross-site scripting (XSS), insecure cookies | Secure cookie flags, session timeouts, re-authentication for sensitive actions |
| Privilege Abuse | Unauthorized access to sensitive functions | Least privilege, PAM, access reviews, activity monitoring |
Evaluating identity and access controls isn’t just about ticking boxes; it’s about understanding the flow of access and identifying potential weak points before they can be exploited. It requires a detailed look at policies, technologies, and human processes.
Cloud Security Assurance Testing
Testing security in cloud environments is a bit different than with your own servers. You’ve got shared responsibility, which means the cloud provider handles some security, and you handle the rest. It’s important to know where those lines are drawn and make sure you’re covering your part.
Configuration Baseline Reviews
This is all about making sure your cloud setup follows a secure blueprint. Think of it like building a house – you need a solid foundation and walls before you start adding furniture. In the cloud, this means checking that services like storage buckets, virtual machines, and databases are set up according to best practices and your organization’s security policies. We’re looking for things like overly permissive access settings, unencrypted data, or exposed management interfaces. It’s easy to make a mistake when you’re spinning up resources quickly, and these reviews catch those slip-ups before they become a problem.
- Key areas to check include:
- Identity and Access Management (IAM) policies
- Network security group rules
- Storage bucket permissions and encryption
- Logging and monitoring configurations
- Compute instance security settings
Cloud Access Security Broker Integration
Cloud Access Security Brokers, or CASBs, act like a security guard for your cloud apps. They sit between your users and the cloud services, giving you visibility and control. Testing here involves making sure the CASB is properly integrated and configured to enforce your organization’s policies. This could mean checking if it’s correctly identifying sensitive data, blocking access to risky apps, or monitoring user activity for suspicious behavior. It’s about making sure that tool you bought is actually doing its job and not just sitting there.
CASBs help organizations maintain control over data and applications used in cloud environments, especially when dealing with a mix of sanctioned and unsanctioned services.
Shared Responsibility Validation
This is where we confirm that both you and your cloud provider are doing what you’re supposed to. The provider secures the underlying infrastructure, but you’re responsible for securing your data, applications, and how you configure access. Testing involves reviewing documentation, checking your own configurations against the provider’s responsibilities, and verifying that your security controls align with the shared model. It’s a bit like a handshake agreement – you need to be sure the other party is holding up their end, and that you’re not leaving any gaps.
| Area of Responsibility | Cloud Provider’s Role | Your Role |
|---|---|---|
| Physical Infrastructure | Secures data centers | N/A |
| Network Infrastructure | Manages network hardware | Configures network security groups, firewalls |
| Identity Management | Provides IAM services | Configures user roles, permissions, MFA |
| Data Security | Offers encryption services | Manages encryption keys, data classification |
| Application Security | N/A | Secures application code, dependencies |
Network and Endpoint Security Testing
When we talk about keeping our digital stuff safe, we can’t forget about the network and the devices connected to it. This is where network and endpoint security testing comes in. It’s all about making sure the pathways our data travels on, and the computers and phones that access it, are locked down tight.
Firewall and Segmentation Testing
Firewalls are like the gatekeepers of your network, deciding what traffic gets in and out. Testing them involves making sure those rules are actually doing their job. We’re not just checking if they’re on, but if they’re configured correctly to block unwanted access and allow only necessary communication. This also ties into network segmentation, which is like building internal walls within your network. If one part gets compromised, the damage stays contained. Testing this means verifying that these segments are isolated and that traffic can’t just hop from one zone to another without proper checks. It’s a key part of a good defense-in-depth strategy.
Endpoint Protection Validation
Your endpoints – laptops, desktops, servers, even mobile devices – are often the first place attackers try to get in. So, validating endpoint protection is super important. This isn’t just about having antivirus software. It’s about checking if your Endpoint Detection and Response (EDR) tools are actually detecting suspicious behavior, if devices are getting their security updates on time, and if they’re configured securely. We want to make sure that if something does slip through, it gets caught quickly before it can spread. Think of it as checking the locks on every single door and window of your house, not just the front door.
Intrusion Detection Verification
Even with the best defenses, sometimes bad actors try to sneak in. Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) are designed to spot and stop these attempts. Verification here means testing if these systems are actually flagging suspicious network activity and if they’re correctly configured to alert you or even block the malicious traffic. It’s like having a security camera system that not only records but also has an alarm that goes off when someone tries to break in. We need to know that these systems are working and not just making noise or, worse, missing the actual threat. Measuring things like the number of alerts generated and how quickly they are investigated can give us a good idea of their effectiveness, helping to track key security metrics.
Testing network and endpoint security isn’t a one-time thing. Threats change, and so do our networks. Regular checks and updates are needed to stay ahead. It’s about building a resilient system that can withstand attacks and recover quickly if something goes wrong.
Supply Chain and Third-Party Risk Assessment
When we talk about security, it’s easy to just focus on what’s inside our own walls. But these days, a lot of what we do relies on other companies, whether it’s the software we use, the cloud services we depend on, or even the hardware components that make up our systems. This is where supply chain and third-party risk assessment comes in. It’s about looking at the security of those external partners and making sure they aren’t bringing hidden dangers into our environment.
Software Dependency Analysis
Think about all the open-source libraries and third-party components that go into building modern applications. Each one is like a small piece of code that we trust. But what if one of those pieces has a flaw? Attackers can exploit these dependencies to get into systems. We need ways to track what we’re using and check if those components are safe. Tools that scan for known vulnerabilities in libraries, like Software Composition Analysis (SCA), are really helpful here. It’s about knowing what you’re bringing into your house, so to speak.
Vendor Security Audits
Beyond just the code, we also need to look at the companies themselves. Are they taking security seriously? This involves doing some homework before we partner with them. It means asking tough questions about their security practices, looking at their certifications, and understanding how they handle our data. A good vendor security audit goes beyond a simple questionnaire; it might involve reviewing their policies, checking their incident response plans, and even looking at their own third-party relationships. This is a key part of vendor security due diligence.
Update and Patch Integrity Checks
One of the most common ways attackers get in is by compromising legitimate software updates. They might sneak malicious code into an update that gets pushed out to thousands of users. So, it’s not enough to just apply patches; we need to be sure the patches themselves are legitimate and haven’t been tampered with. This involves verifying digital signatures and looking for any unusual behavior in the update process. It’s a constant battle to make sure the updates you’re installing are actually helping, not hurting.
The interconnected nature of modern business means that a security weakness in one organization can quickly become a problem for many others. Understanding and managing these external risks is no longer optional; it’s a core part of a robust security strategy.
We need to be smart about who we work with and what we use. It’s a complex area, but ignoring it leaves us wide open to attacks that can be incredibly damaging. Effectively reporting on these risks to leadership is also important, using methods that clearly communicate potential threats, whether through qualitative or quantitative assessments, to support better cyber risk reporting.
User Awareness and Human Factors Testing
When we talk about security, it’s easy to get caught up in firewalls, encryption, and all the technical stuff. But let’s be real, a lot of security incidents happen because of people. That’s where testing user awareness and human factors comes in. It’s about understanding how people interact with security systems and policies, and where those interactions might create weak spots.
Phishing Simulation Campaigns
Phishing is still a huge problem. Attackers send fake emails or messages trying to trick people into clicking bad links, downloading malware, or giving up sensitive information. Running simulated phishing campaigns is a smart way to see how well your team can spot these tricks. We send out fake phishing emails that look pretty real, and then we track who clicks on them, who opens attachments, and who might have given away their login details. It’s not about shaming anyone; it’s about identifying where more training is needed. The results can be eye-opening.
Here’s a quick look at what we might track:
| Metric | Description |
|---|---|
| Click-Through Rate | Percentage of users who clicked a malicious link. |
| Credential Submission | Percentage who entered login details. |
| Attachment Opened | Percentage who opened a suspicious attachment. |
| Reporting Rate | Percentage who reported the suspicious email. |
Policy Acknowledgment and Training
Having security policies is one thing, but making sure everyone actually reads, understands, and agrees to them is another. We test this by checking if employees have formally acknowledged security policies, like those covering password management or data handling. Regular training sessions are also key. We look at how effective these training programs are, not just by seeing if people pass a quiz, but by observing if their behavior changes. For instance, do they start using stronger passwords after training? Do they report suspicious activity more often? It’s about making security a habit, not just a rule they signed off on once. A good security awareness training program should be ongoing and relevant to daily tasks effective security awareness training.
Reporting Incident Procedures
When something looks fishy, people need to know what to do. This means having clear, simple procedures for reporting security incidents. We test this by seeing if employees can easily find out who to contact and how to report a potential issue. Sometimes, we might even run scenarios where we ask employees to report something that isn’t actually a problem, just to see if they follow the correct channels. Prompt reporting is super important because it can stop a small issue from becoming a major disaster. If people are afraid to report, or don’t know how, that’s a big risk.
The human element in security is often the most unpredictable, but also the most critical. Focusing on awareness, clear procedures, and practical training can significantly reduce the likelihood of successful attacks that rely on human error or manipulation.
Incident Response and Recovery Testing
When a security incident happens, having a plan is one thing, but actually testing that plan is another. Incident response and recovery testing is all about making sure your team knows what to do when the worst occurs. It’s not just about having a document; it’s about muscle memory and coordinated action. We’re talking about simulating real-world scenarios to see how well your defenses hold up and, more importantly, how quickly and effectively your team can get things back to normal.
Tabletop Exercises and Playbooks
Tabletop exercises are a fantastic way to start. Think of it as a walk-through. Your team gathers, and a scenario is presented – maybe a ransomware attack or a data breach. You then go through the steps outlined in your incident response playbooks, discussing who does what, when, and how. This helps identify gaps in your procedures and communication before a real event forces you to figure it out on the fly. It’s a low-pressure environment to iron out the kinks. These exercises are key to developing comprehensive incident response capabilities.
Here’s a basic breakdown of what a tabletop exercise might cover:
- Scenario Introduction: Presenting the simulated incident (e.g., "We’ve detected unusual outbound traffic from our finance servers.")
- Initial Triage and Assessment: Discussing how the team would verify the alert, determine its scope, and classify its severity.
- Containment Actions: Deciding on immediate steps to limit the spread, like isolating affected systems or disabling accounts.
- Eradication and Recovery: Planning how to remove the threat and restore systems to a secure, operational state.
- Communication Strategy: Outlining who needs to be informed, both internally and externally.
Digital Forensics Readiness
If an incident occurs, you’ll likely need to understand exactly what happened. Digital forensics readiness means having the tools, processes, and trained personnel in place to collect and analyze digital evidence properly. This isn’t just about finding out who did it; it’s about understanding the attack vector, the extent of the compromise, and gathering evidence that might be needed for legal action or regulatory reporting. Chain of custody for evidence is absolutely critical to maintain its integrity. Without proper readiness, valuable information can be lost or corrupted, making it impossible to learn from the incident or hold responsible parties accountable.
Backup and Restoration Verification
This is the part that often gets overlooked until it’s too late. You can have the best incident response plan in the world, but if your backups are corrupted, incomplete, or simply don’t work, recovery becomes a nightmare. Regularly testing your backup and restoration procedures is non-negotiable. This means not just checking if a backup file exists, but actually performing a restore operation to a test environment. You need to verify that the data is intact and that you can bring systems back online within your defined recovery time objectives. This is a core part of ensuring business continuity and minimizing downtime. It’s about confirming that your safety net actually catches you when you fall.
Compliance-Driven Security Assurance Activities
Mapping Controls to Standards
When we talk about compliance, it’s not just about ticking boxes; it’s about making sure our security setup actually lines up with what the rules say we should be doing. This means we need to take a good, hard look at all the security measures we have in place – things like our firewalls, how we manage user access, and even how we train our staff – and then figure out exactly which ones meet the requirements of specific regulations or industry standards. It’s like making a checklist to see if our security practices are on the same page as, say, GDPR or PCI DSS. This process helps us spot where we might be falling short and where we’re doing a good job. It’s a critical step in proving we’re serious about protecting data and systems.
Audit Readiness Assessments
Getting ready for an audit can feel like preparing for a big exam. We need to make sure all our documentation is in order, that our security controls are actually working as intended, and that we can easily show evidence of this to the auditors. This involves things like reviewing our policies, checking our logs, and sometimes even running internal tests to simulate what an auditor might look for. The goal here is to be confident that when the auditors arrive, we can demonstrate our compliance without a lot of last-minute scrambling. It’s about having a clear picture of our security posture and being able to back it up with facts. This proactive approach helps us identify and fix issues before they become major problems during an actual audit, which can save a lot of headaches and potential fines. It’s also a good way to ensure our security team is aligned with the broader organizational goals and risk tolerance. For more on how audits verify compliance, check out this context on audits.
Maintaining Regulatory Documentation
Keeping track of all the paperwork related to compliance is a big job. This includes everything from security policies and procedures to records of training, incident reports, and evidence of control implementation. We need a system to organize and store this information so it’s readily available when needed, especially during audits or investigations. Think of it as building a reliable history of our security efforts. This documentation isn’t just for auditors; it also helps us understand our own processes better and identify areas for improvement. It’s about creating a clear, auditable trail that shows we’re actively managing our security responsibilities. Without good documentation, even the best security practices can be hard to prove.
Continuous Monitoring and Security Telemetry
Keeping an eye on things is super important in security. It’s not enough to just set up defenses and hope for the best. You need to constantly watch what’s happening across your systems, networks, and applications. This is where continuous monitoring and security telemetry come into play. Think of it like having a really good security camera system for your entire digital environment, but instead of just video, you’re collecting all sorts of data.
Log Collection and Analysis
Logs are basically records of what’s happening. Every system, application, and device generates logs – think login attempts, file access, network connections, and error messages. Collecting all these logs in one place and then digging through them is key. It helps you spot unusual activity that might signal a problem. Without good log management, you’re flying blind. It’s like trying to find a needle in a haystack without a magnet.
- Centralized Log Aggregation: Gather logs from all sources (servers, firewalls, applications, endpoints) into a single repository.
- Log Normalization: Standardize log formats so they can be easily compared and analyzed.
- Log Retention and Integrity: Ensure logs are stored securely for a defined period and can’t be tampered with.
Anomaly Detection Strategies
Just collecting logs isn’t enough; you need to figure out what’s normal and what’s not. Anomaly detection uses various techniques to identify deviations from typical behavior. This could be a user logging in from an unusual location, a server suddenly using a lot of network bandwidth, or a program making unexpected system calls. Spotting these anomalies early can help you catch threats before they cause major damage. It’s about finding the digital equivalent of a strange noise in the house when you’re supposed to be alone.
Effective detection relies on having a good baseline of normal activity. Without this context, it’s hard to tell if something is truly suspicious or just a one-off event. This baseline needs to be regularly updated as your environment changes.
Key Security Metric Tracking
Metrics give you a way to measure the effectiveness of your security program. Instead of just guessing, you can look at data to see what’s working and what’s not. This could include things like the number of security incidents detected per month, the average time it takes to respond to an alert, or the percentage of systems that are up-to-date with patches. Tracking these metrics helps you make informed decisions about where to focus your security efforts and resources. It’s about making security measurable and driving continuous improvement. You can check out security metrics to get a better idea of what to track.
Wrapping Up Security Assurance Testing
So, we’ve looked at a bunch of ways to test security, from checking code as it’s written to making sure systems are set up right and that people know what they should and shouldn’t be doing. It’s not just about finding bugs; it’s about building trust in our digital stuff. Keeping systems patched, managing configurations, and testing applications regularly all play a part. And let’s not forget the human side – training and awareness are just as important as any technical control. Ultimately, security testing isn’t a one-and-done deal. It’s an ongoing process that needs to keep up with new threats and changes in technology. By using a mix of these methods, organizations can build stronger defenses and be better prepared for whatever comes their way.
Frequently Asked Questions
What is security assurance testing?
Security assurance testing is like checking if a castle’s walls are strong and if only the right people can get inside. It’s a way to make sure computer systems and apps are safe from bad guys trying to break in or steal things. We test different parts to find weak spots before they can be used against us.
Why is it important to test for vulnerabilities?
Imagine leaving a window unlocked at home. Vulnerabilities are like those unlocked windows for computers. Testing helps us find these unlocked windows so we can lock them up. If we don’t, hackers might sneak in and cause trouble, like stealing information or messing up our systems.
What’s the difference between vulnerability scanning and penetration testing?
Vulnerability scanning is like quickly walking around the castle and looking for obvious weak spots, like a loose brick. Penetration testing is like actually sending a spy to try and break into the castle, testing the walls, doors, and guards to see how well they hold up. It’s a more hands-on and realistic test.
How does testing help protect applications?
Applications are the tools we use every day, like social media or online banking apps. Testing applications is like making sure these tools are built with strong materials and have good locks. It helps find flaws in the app’s design or code that could let bad actors get in and access our information.
What does ‘least privilege’ mean in security?
Least privilege is like giving someone only the keys they absolutely need to do their job, and no more. If a worker only needs to access the kitchen, they shouldn’t get a key to the vault. This way, if their keys get stolen, the thief can’t get into places they shouldn’t be.
Why is testing important for cloud security?
When we use cloud services, it’s like renting space in a big, shared building. We still need to make sure our own space is secure and that we’re following the building’s rules. Cloud security testing checks that our settings are correct and that we’re not accidentally leaving doors open for others to access our stuff.
What are ‘red team exercises’?
Red team exercises are like having a pretend enemy team (the red team) try to attack our systems. They act like real hackers. This helps our own security team (the blue team) practice spotting and stopping attacks. It’s a great way to see how well our defenses really work when put to the test.
How does user training fit into security testing?
Sometimes, the weakest link isn’t the technology, but people. Training users on how to spot fake emails (phishing) or create strong passwords is a form of testing their awareness. We might even send fake phishing emails to see who clicks them, so we know where to focus more training.
