You know, we all go through things, right? Sometimes stuff happens at work, especially in security, and you learn a thing or two. The trick is actually *using* that knowledge. It’s not just about writing down what went wrong after a security incident. It’s about making sure that information actually changes how we do things. This whole process of lessons learned integration security is pretty important if we want to get better and not keep making the same mistakes. Let’s talk about how to make that happen.
Key Takeaways
- Building a strong foundation for lessons learned integration security means getting your governance, risk management, and policies in order first. It’s like making sure your house has a solid base before you start adding furniture.
- When a security incident happens, don’t just fix it and forget it. Really dig into what went wrong, figure out the root cause, and use that to improve your response plans and security controls. This feedback loop is key.
- Use what you learn from security events to make your defenses better. If an incident showed a weakness, update your controls, fix vulnerabilities, and improve how you handle patches. It’s about making your security tighter.
- Keep an eye on what threats are out there and share that information. Knowing what’s happening in the wider world helps you get ahead of potential problems before they hit you directly.
- Remember that people are a big part of security. Make systems easier to use, train people well, and be mindful of things like security fatigue. Happy, aware employees are better defenders.
Establishing A Foundation For Lessons Learned Integration
Getting security right from the start means building a solid base for how we learn and improve. It’s not just about reacting when something goes wrong; it’s about setting up systems that help us get better all the time. This involves looking at our overall approach to security and making sure it fits with what the business is trying to do.
Cybersecurity Governance Frameworks
Think of governance as the rulebook and the referees for our security efforts. It’s about making sure everyone knows who’s responsible for what and that our security actions actually help the company achieve its goals. Without clear governance, it’s easy for security to become an afterthought or a set of disconnected tasks. A good framework helps us manage security effectively, aligning it with business objectives and defining clear accountability. This is key for making sure our incident response efforts are well-coordinated and that we can actually learn from what happens. It’s about having the right structure in place to oversee security, which is a core part of risk management foundations.
Risk Management Foundations
Before we can learn from incidents, we need to understand what we’re trying to protect and what the potential dangers are. Risk management is all about identifying these dangers, figuring out how likely they are to happen, and what the impact would be if they did. This helps us focus our efforts on the most important areas. We need to know where our weak spots are and what threats are out there. This process helps us prioritize where to spend our time and resources, making sure we’re not just guessing. It’s about making informed decisions based on potential threats and vulnerabilities.
Policy Frameworks
Policies are the written rules that guide our behavior and set expectations for security. They need to be clear, practical, and easy for everyone to understand. A good policy framework doesn’t just list rules; it explains why they’re important and how they fit into the bigger picture of protecting the organization. When policies are well-defined and communicated, they become a strong tool for managing security. They provide a baseline for what’s acceptable and what’s not, helping to prevent many issues before they even start. Having these frameworks in place is a big step towards a more secure environment, and they are often a requirement for compliance and regulatory requirements.
Integrating Security Incident Feedback Loops
When a security incident happens, it’s not just about putting out the fire. It’s a chance to learn and get better. We need to make sure that what we learn from these events actually changes how we do things. This means creating a solid loop where information from incidents goes back into improving our defenses and processes.
Post-Incident Review and Learning
After an incident, the most important thing is to figure out exactly what went wrong and why. This isn’t about pointing fingers; it’s about understanding the root cause. A good review looks at the timeline, the actions taken, and the outcome. The goal is to identify specific, actionable steps to prevent the same thing from happening again. This process helps refine our incident response plans and strengthens our overall security posture. It’s about continuous refinement to reduce recurrence.
Here’s a basic breakdown of what a post-incident review might cover:
- Incident Timeline: When did it start, when was it detected, when was it resolved?
- Root Cause Analysis: What technical or procedural failures allowed it to happen?
- Response Effectiveness: What worked well, and what could have been done better?
- Lessons Learned: What specific changes are needed in policies, controls, or training?
- Action Items: Who is responsible for implementing the changes, and by when?
The real value of an incident isn’t the event itself, but the knowledge gained and applied afterward. Without a structured way to capture and act on these lessons, incidents become costly repetitions rather than opportunities for growth.
Incident Response Governance
Having a clear structure for how incidents are handled is key. This means defining roles, who has the authority to make decisions, and how communication flows, both internally and externally. Good governance makes sure that during a crisis, everyone knows their part and can act quickly and effectively. This preparedness shortens recovery time significantly. It’s about having defined roles, escalation paths, and communication protocols ready to go.
Key elements of incident response governance include:
- Defined Roles and Responsibilities: Who leads the response, who handles technical aspects, who manages communications?
- Escalation Paths: When and how should an incident be escalated to higher levels of management or specialized teams?
- Communication Protocols: How will internal teams communicate, and how will external stakeholders (like customers or regulators) be informed?
- Decision Authority: Who has the final say on critical decisions, such as taking systems offline?
Root Cause and Remediation
Once an incident is contained, the focus shifts to fixing the underlying problem. Root cause analysis is more than just finding the immediate trigger; it’s about digging deeper to understand the systemic issues that allowed the incident to occur. Remediation then involves implementing specific changes to address these root causes. This could mean updating software, changing configurations, or revising policies. Fixing symptoms without addressing the root cause often leads to repeat incidents. This is where we can really improve our defenses by continuously monitoring security controls and making targeted improvements.
Here’s a look at the remediation process:
- Identify Root Cause: Use forensic data and analysis to pinpoint the fundamental reason for the incident.
- Develop Remediation Plan: Outline specific actions, resources, and timelines needed to fix the identified issues.
- Implement Changes: Execute the remediation plan, which might involve patching, reconfiguring systems, or updating procedures.
- Validate Fixes: Test to confirm that the implemented changes effectively address the root cause and prevent recurrence.
- Update Documentation: Record the incident, the root cause, the remediation steps, and any updated policies or procedures.
This structured approach ensures that lessons learned from incidents are translated into concrete improvements, making the organization more resilient against future attacks. It’s also vital to integrate this with threat hunting to proactively find similar weaknesses.
Enhancing Security Controls Through Incident Analysis
When a security incident happens, it’s not just about putting out the fire. It’s a chance to really look at what went wrong and how we can make things tougher for attackers next time. Think of it like a mechanic fixing a car after a breakdown; they don’t just fix the broken part, they figure out why it broke and make sure it doesn’t happen again. This is where incident analysis really shines.
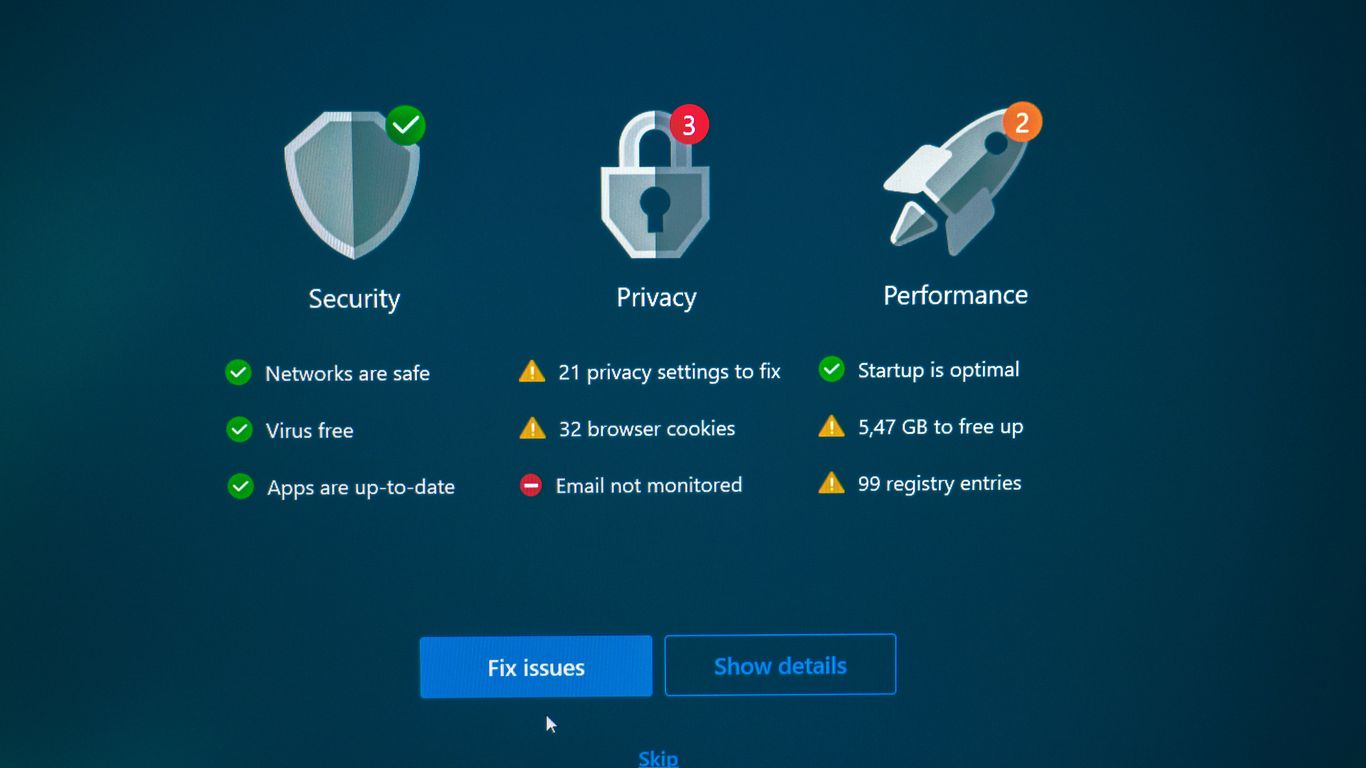
Incidents Inform Control Enhancements
Every incident, big or small, gives us clues. A successful phishing attempt, for example, might show that our current email filters aren’t catching everything, or that users aren’t quite sure what to look for. This isn’t about blame; it’s about learning. We can then use this information to update our filters, tweak our policies, or even adjust how we train people. It’s a cycle: incident happens, we learn, we improve our defenses. This continuous loop helps us stay ahead. We need to make sure our detection systems are actually working, and that means looking at the alerts they generate. Sometimes, too many alerts can be as bad as too few, leading to what’s called security fatigue. We need to find that balance.
- Reviewing alert data to identify false positives and tune detection rules.
- Analyzing successful attack vectors to understand common entry points.
- Updating firewall rules or access controls based on observed malicious traffic patterns.
The goal here is to transform reactive responses into proactive improvements. Each event is a data point that can strengthen our overall security posture, making the organization more resilient against future threats.
Vulnerability Management and Testing
Incidents often highlight existing weaknesses. If an attacker managed to exploit a specific software flaw, it’s a clear signal that our vulnerability management needs a closer look. This means not just finding vulnerabilities, but also making sure we’re fixing them quickly and effectively. Regular testing, like penetration tests, can simulate attacks to see if our current controls would hold up. It’s like stress-testing our defenses before a real attack happens. We need to keep a close eye on what’s being found and how quickly it’s being addressed. A table showing common vulnerabilities and their remediation timelines can be really helpful here:
| Vulnerability Type | Common Exploitation Vector | Average Time to Remediate (Days) |
|---|---|---|
| Unpatched Software | Known CVE exploitation | 7 |
| Misconfiguration | Exposed service | 3 |
| Weak Credentials | Credential stuffing | 1 |
This kind of data helps us see where we’re doing well and where we need to speed things up. It’s all about reducing our attack surface before someone else finds it.
Patch Management Strategies
Patching is one of those things that’s easy to put off, but incidents show why it’s so important. If a system gets compromised because it was missing a simple security update, that’s a preventable failure. Our strategy needs to be clear: identify what needs patching, prioritize based on risk, and then actually apply the patches. This isn’t just about software; it includes operating systems, firmware, and even applications. We need to make sure that our systems are up-to-date and that we’re not leaving doors open for attackers. A good patch management plan means less chance of a simple exploit leading to a major incident. It’s a core part of keeping our systems secure and reducing the risk of privilege escalation.
Leveraging Threat Intelligence for Proactive Security
Threat intelligence is more than just a buzzword; it’s about using information to get ahead of potential problems. Instead of just reacting when something bad happens, we can use what we know about attackers and their methods to build better defenses. This means looking at what’s happening out there in the wider cyber world and figuring out how it might affect us.
Threat Intelligence and Information Sharing
Gathering threat intelligence involves collecting data on indicators of compromise, understanding attacker infrastructure, and recognizing common behavioral patterns. It’s not enough to just collect this data; it needs to be analyzed and made useful. Sharing this information across different organizations and sectors can significantly strengthen collective defense. Think of it like a neighborhood watch, but for the digital world. When one house sees something suspicious, they tell everyone else, making the whole block safer. This collaborative approach helps everyone stay one step ahead of evolving threats. Effective programs often involve structured ways to share this insight, making it actionable for all participants. This shared knowledge strengthens defense across the board [756d].
AI-Driven Attacks and Defense Adaptation
Artificial intelligence is changing the game for attackers. They’re using AI to make phishing emails more convincing, create realistic deepfakes for social engineering, and automate reconnaissance. This means attacks can be scaled up and become much harder to spot. Because of this, our own defenses need to adapt. We’re seeing more AI and machine learning being used on the defensive side too, to analyze vast amounts of data and identify unusual activity that might signal an attack. It’s a constant race, with both sides using advanced tech.
Cyber Threat Landscape Evolution
The landscape of cyber threats is always shifting. Attackers are becoming more organized, financially motivated, and are using more sophisticated techniques. They’re not just using one method; attacks often combine social engineering, credential abuse, and even using legitimate system tools to hide their tracks. Ransomware, for example, has evolved significantly, with tactics like double and triple extortion becoming more common. Understanding these evolving threat actor models and their motivations is key to building defenses that can actually keep up. It’s a dynamic environment, and staying informed is half the battle.
- Phishing and Social Engineering: Attackers use AI to personalize these attacks, making them more convincing.
- Ransomware: Evolved tactics include data theft alongside encryption.
- Supply Chain Attacks: Compromising trusted vendors to reach multiple targets.
The effectiveness of our security posture hinges on our ability to anticipate and adapt to the ever-changing tactics of threat actors. Proactive measures, informed by robust threat intelligence, are no longer optional but a necessity for survival in the digital age.
Strengthening Security Awareness and Human Factors
When we talk about cybersecurity, it’s easy to get caught up in firewalls, encryption, and the latest threat detection tools. But let’s be honest, a lot of security incidents start with people. That’s where focusing on security awareness and the human element comes in. It’s not just about ticking a box; it’s about building a culture where everyone understands their role in keeping things safe.
Human-Centered Security Design
Think about how we interact with technology every day. If a security control is clunky or makes a task unnecessarily difficult, people will find ways around it. That’s why designing security with the user in mind is so important. When security tools and processes are intuitive and easy to use, people are more likely to adopt them. This isn’t about lowering standards; it’s about making the right thing to do the easiest thing to do. We need to consider how people actually work and build security into those workflows, rather than just layering it on top. This approach helps reduce the chances of accidental mistakes, which are a major source of security problems.
Security Fatigue Mitigation
We’ve all been there – bombarded with alerts, endless policy updates, and constant reminders. This can lead to something called security fatigue, where people start to tune out important warnings. It’s like the boy who cried wolf. To combat this, we need to streamline security processes and reduce unnecessary noise. This means prioritizing alerts, automating routine tasks, and making sure the security messages we send are clear and actionable. Instead of overwhelming people, we should aim for focused, relevant communication. It’s about making sure that when a real alert comes through, it gets the attention it deserves.
The effectiveness of security measures is directly tied to how well they integrate with human behavior. Overly complex or intrusive controls often lead to workarounds, diminishing the intended security benefit. A more effective strategy involves designing systems that are both secure and user-friendly, thereby encouraging compliance and reducing the likelihood of errors.
Onboarding and Offboarding Security Training
Security shouldn’t be an afterthought when someone joins or leaves the company. For new hires, onboarding is the perfect time to set clear expectations about security policies and safe practices. This early education can prevent risky behaviors from developing in the first place. On the flip side, offboarding needs to be just as thorough. When an employee leaves, their access must be removed promptly and completely. Delays here can create significant risks, especially if the departing employee has lingering access. Having a structured process for both ensures a smoother transition and reduces potential vulnerabilities.
Here’s a quick look at what effective onboarding and offboarding training should cover:
- Onboarding:
- Introduction to company security policies.
- Recognizing common threats like phishing and social engineering.
- Proper handling of sensitive data.
- Reporting security incidents.
- Offboarding:
- Confirmation of access revocation.
- Return of company assets.
- Reminders about data confidentiality agreements.
- Secure data handling during transition.
By paying attention to these human factors, we can build a much stronger defense. It’s about making security a shared responsibility, not just a technical problem. For more on how to assess your current security posture, including human elements, check out understanding security posture. And to design programs that really stick, consider building a security awareness program.
Measuring And Improving Security Program Effectiveness
It’s easy to get caught up in the day-to-day of security operations, putting out fires and reacting to new threats. But how do you actually know if what you’re doing is working? That’s where measuring and improving your security program comes in. It’s not just about having controls in place; it’s about understanding their impact and making them better over time. This means looking at both the technical side of things and, importantly, the human element.
Training Effectiveness Measurement
We spend a lot of time and resources on security awareness training. But does it actually change behavior? Measuring the effectiveness of this training is key. We can look at things like how often employees fall for simulated phishing emails. If that number goes down after training, that’s a good sign. We also track how many security incidents are reported by employees – a higher number might mean they’re more aware and know what to look for. It’s about seeing if the training translates into real-world actions that reduce risk.
Metrics and Response Performance
When an incident does happen, how quickly and effectively do we respond? Metrics like Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) give us a clear picture. MTTD tells us how long it takes to even notice something is wrong, while MTTR measures how long it takes to get things back to normal. Lower numbers here generally mean a stronger defense. We also look at containment time – how fast we can stop the spread of an attack – and recovery time, which is about getting systems back online. These numbers help us pinpoint where our response processes might be slow or inefficient.
| Metric | Current Average | Target | Improvement Area |
|---|---|---|---|
| Mean Time to Detect (MTTD) | 48 hours | 24 hours | Alert correlation and monitoring |
| Mean Time to Respond (MTTR) | 72 hours | 36 hours | Playbook refinement and automation |
| Containment Time | 12 hours | 6 hours | Incident response team training |
Measuring Security Performance
Beyond specific incidents, we need to look at the overall health of our security program. This involves a mix of quantitative and qualitative measures. Are we seeing a reduction in the number of critical vulnerabilities? Is our compliance with security policies improving? We can also assess user behavior, looking for signs of security fatigue, which can happen when people are overwhelmed with alerts or complex procedures. Addressing this fatigue is important because tired users are more likely to make mistakes. Ultimately, we want to see a trend of improvement, showing that our security efforts are making a real difference in protecting the organization. This continuous evaluation is vital for adapting to the ever-changing threat landscape and integrating information sharing into our defense strategy.
Effective security measurement isn’t just about collecting data; it’s about using that data to drive meaningful change. It requires a commitment to understanding what works, what doesn’t, and why, then acting on those insights to build a more robust and resilient security posture. This data-driven approach is key to developing effective security metrics and demonstrating the value of security investments to the wider organization.
Building Resilience Through Continuous Improvement
Resilience and Adaptation
Cyber resilience is about more than just bouncing back from an incident; it’s about getting stronger. It means designing systems and processes that can handle disruptions and then learning from those events to improve future responses. Think of it like a boxer training: they don’t just train to win a fight, they train to withstand punches and come back even tougher. This involves understanding how attacks happen and then making sure your defenses can adapt. It’s a constant cycle of preparing, responding, and refining. Building this kind of adaptability is key to staying ahead in the long run. We need to look at how we can make our systems more robust, so they don’t just survive an attack but actually learn from it. This is where we start to see real progress in our security posture.
Business Continuity and Disaster Recovery
When things go wrong, and they sometimes do, having a solid plan for business continuity and disaster recovery is non-negotiable. This isn’t just about getting servers back online; it’s about making sure the business can keep running, even with limited resources or damaged infrastructure. It involves identifying what absolutely needs to keep working and having backup plans ready. We need to test these plans regularly, not just assume they’ll work when we need them. A well-rehearsed plan can make the difference between a minor hiccup and a major crisis. It’s about having those pre-defined procedures, or playbooks, ready to go so that when an incident strikes, the team knows exactly what steps to take. This preparedness is a huge part of overall resilience.
| Critical Function | Recovery Time Objective (RTO) | Recovery Point Objective (RPO) |
|---|---|---|
| Customer Support | 4 hours | 1 hour |
| Core Operations | 2 hours | 15 minutes |
| Financial Reporting | 24 hours | 4 hours |
Cybersecurity as Continuous Governance
Cybersecurity isn’t a project with an end date; it’s an ongoing process, a form of continuous governance. This means that oversight, accountability, and strategic alignment of security efforts need to be constantly reviewed and updated. As new threats emerge and technologies change, our governance structures must evolve too. It’s about embedding security into the fabric of how the organization operates, not treating it as an add-on. This requires regular assessments, policy updates, and a commitment from leadership to adapt. Without this continuous oversight, even the best initial security setup can become outdated and ineffective. We need to make sure our security practices are always aligned with current risks and business goals. This approach helps us maintain a strong security posture over time and respond effectively to new challenges. Cybersecurity governance is the backbone of this continuous effort.
Integrating Security Into The Development Lifecycle
Bringing security into the software development process from the get-go isn’t just a good idea; it’s pretty much a necessity these days. We’re talking about making sure security isn’t an afterthought, something bolted on at the end when it’s way harder and more expensive to fix. It’s about building it in from the ground up, right from the initial design stages.
Secure Development and Application Architecture
This means thinking about security when you’re first sketching out how an application will work. It involves things like threat modeling, which is basically trying to guess how someone might try to break your app before you even write the code. Then there’s adopting secure coding standards – basically, a set of rules for writing code that avoids common mistakes that lead to vulnerabilities. It’s also about managing your dependencies, which are all the third-party libraries and components your app relies on. You need to know what’s in them and if they have any known security issues. Building security in early significantly reduces risks down the line.
- Threat Modeling: Identifying potential threats and vulnerabilities during the design phase.
- Secure Coding Practices: Following guidelines to write code that is resistant to common attacks.
- Dependency Management: Keeping track of and securing all third-party components used in the application.
When security is woven into the fabric of development, it becomes a natural part of the process, not an obstacle. This proactive approach saves time, money, and a whole lot of headaches later on.
Vulnerability Management in Development
Once you’re building, you can’t just forget about security. You need to be actively looking for weaknesses. This is where vulnerability management comes in. It’s not a one-time check; it’s an ongoing process. You’re identifying, assessing, and then prioritizing any security flaws you find. Think of it like constantly checking your house for weak spots. Tools can help scan your code and systems for known issues. This is a key part of proactive security, making sure you’re fixing things before they become a problem.
Security Embedded Early
Ultimately, the goal is to shift security ‘left,’ meaning as early as possible in the development lifecycle. This involves integrating security checks and balances directly into your development pipelines. Tools that perform static analysis (SAST) and dynamic analysis (DAST) can automatically scan code for flaws. This approach aligns with modern security frameworks and is becoming a standard expectation. It’s about making security a shared responsibility, not just the security team’s job. This also ties into managing your supply chain risk, as many vulnerabilities come from third-party components.
- Static Application Security Testing (SAST): Analyzing source code for vulnerabilities.
- Dynamic Application Security Testing (DAST): Testing running applications for weaknesses.
- Software Composition Analysis (SCA): Identifying risks in open-source libraries and dependencies.
This integrated approach helps create more robust and secure applications from the start, reducing the likelihood of costly breaches and compliance issues.
Addressing Evolving Attack Methodologies
Attackers are always finding new ways to get into systems. It’s not just about finding a hole and going through it anymore. They’re getting smarter, using more complex methods that can be hard to spot. We need to keep up with these changes to stay ahead.
AI-Powered Attacks
Artificial intelligence is changing the game for attackers. They’re using AI to make phishing emails sound more convincing, create fake but realistic-looking videos or audio for scams, and even automate the process of finding weaknesses in systems. This means attacks can be more personalized and scaled up much faster than before. It’s a big shift from the old days of generic spam.
- AI for Phishing: Generating highly personalized and context-aware phishing messages.
- Deepfakes: Creating convincing fake audio or video for social engineering.
- Automated Reconnaissance: Using AI to scan for and identify system vulnerabilities.
The rise of AI in attacks means we can’t rely solely on traditional signature-based detection. We need systems that can spot unusual behavior and adapt quickly.
Data Exfiltration and Destruction Tactics
Beyond just stealing data, attackers are now more focused on making sure organizations can’t recover. This includes tactics like "double extortion," where they not only encrypt your data but also threaten to release it publicly if you don’t pay. Some might even just aim to destroy data to cause maximum disruption. This means our defenses need to be ready for both data theft and outright destruction, and our recovery plans need to be robust.
| Tactic | Description |
|---|---|
| Double Extortion Ransomware | Encrypts data and threatens public release if ransom isn’t paid. |
| Data Destruction | Malware designed to permanently delete or corrupt data. |
| Covert Exfiltration | Stealing data through less obvious channels like DNS or HTTPS traffic. |
Credential and Session Exploitation
Getting hold of someone’s login details is still a big win for attackers. They’re using methods like credential stuffing, where they try lists of stolen usernames and passwords from other breaches, hoping people reuse their passwords. They also go after session tokens, which can let them impersonate a logged-in user without needing the password at all. This highlights why strong authentication, like multi-factor authentication (MFA), and careful management of user sessions are so important. It’s about making sure that even if credentials are compromised, the attacker can’t easily get in or stay in. We need to be on the lookout for suspicious login activity and monitor authentication logs closely.
- Credential Stuffing: Using leaked credentials from one breach to access other accounts.
- Session Hijacking: Stealing active session tokens to impersonate users.
- Password Spraying: Trying common passwords across many accounts to find weak ones.
Staying updated on these evolving attack methods is key to building effective defenses. It’s a constant race, and understanding how attackers operate is the first step to stopping them. Organizations must adapt their security strategies to these changing threats.
The Role Of Leadership In Security Integration
When we talk about making security a real part of how a company works, not just an add-on, leadership has a massive part to play. It’s not just about the security team doing their thing; it’s about everyone, from the top down, understanding and supporting security efforts. Without that backing, even the best security plans can fall apart.
Leadership Influence on Security Culture
Leaders set the tone for the entire organization. If leaders treat security as an afterthought, employees will too. But if they visibly commit to security, talk about it, and make it a priority in meetings and decisions, it signals that it’s important. This kind of commitment helps build a stronger security culture where people are more likely to follow rules and report issues. It’s about making security a shared value, not just a set of rules.
- Visible commitment: Leaders actively participating in security discussions and initiatives.
- Resource allocation: Dedicating budget and personnel to security programs.
- Accountability: Holding individuals and teams responsible for security practices.
A strong security culture doesn’t happen by accident. It’s built over time through consistent messaging and actions from leadership that show security is a core business function, not just an IT problem.
Governance and Program Management
Leadership is responsible for setting up the right governance structures. This means making sure there are clear policies in place and that they are actually followed. It also involves overseeing the security program to make sure it’s working effectively and adapting to new threats. Think of it like managing any other major business program; it needs oversight, clear goals, and regular check-ins. Effective security policy implementation often starts with clear roles and risk management defining roles.
Enterprise Risk Management Integration
Security shouldn’t live in a silo. Leaders need to make sure that cybersecurity risks are treated the same way as other business risks. This means integrating security considerations into the overall enterprise risk management framework. When security is part of the bigger picture, it gets the attention and resources it needs to protect the business effectively. This operational framework acts as the ‘operating system’ for the security team, focusing on practical, business-aligned security measures security operations governance.
| Risk Area | Leadership Action |
|---|---|
| Data Breach | Approve investment in data loss prevention tools. |
| Ransomware Attack | Support regular incident response drills. |
| Insider Threat | Champion strict access control policies. |
| Supply Chain Risk | Mandate third-party security assessments. |
Moving Forward: Making Lessons Stick
So, we’ve talked a lot about what happens when things go wrong and how to get better. It’s not just about fixing the immediate problem, but really digging into why it happened in the first place. That means writing things down, sharing what we learned, and actually changing how we do things. Think of it like learning from that time you tripped over your own feet – you don’t just get up and do it again, right? You figure out what went wrong and try not to do it again. Applying that same idea to our work, whether it’s a security incident or a project hiccup, helps us build stronger systems and processes. It’s an ongoing thing, not a one-and-done deal, and keeping that cycle of learning and improving going is key to staying ahead.
Frequently Asked Questions
What does it mean to ‘integrate lessons learned’ in cybersecurity?
It means using what we learned from security mistakes or near-misses to make our systems and defenses better. Think of it like learning from a test you didn’t do so well on, so you can ace the next one. We change our rules, fix our security tools, and train our people based on what went wrong or almost went wrong.
How does fixing security problems after an incident help prevent future ones?
When a security problem happens, like a hacker getting in, we figure out exactly how they did it. Then, we fix that specific weak spot. We also look to see if other parts of our system might be weak in a similar way. This helps us stop the same problem from happening again.
Why is it important to learn from security mistakes?
Learning from mistakes is super important because the bad guys are always trying new tricks. If we don’t learn and adapt, we’ll keep falling for the same old tricks. It’s like practicing to get better at a sport; the more you practice and learn from your mistakes, the better you become at winning.
How can we make our security controls better based on what happens in the real world?
We watch what kinds of attacks are happening and how they succeed. If we see a lot of attacks trying to trick people into clicking bad links, we might add more training about phishing. If hackers are finding ways to break into certain types of software, we’ll work harder to update and secure that software.
What is ‘security fatigue’ and how does it affect us?
Security fatigue happens when people get tired of too many security warnings or rules. It’s like hearing a fire alarm so often that you start to ignore it, even if there’s a real fire. To fix this, we try to make security alerts and rules clearer and less annoying, so people pay attention when it really matters.
How does leadership play a role in making security better?
Leaders set the example for everyone. If leaders show that security is important by following the rules and supporting security efforts, then everyone else is more likely to take it seriously too. They help create a culture where security is everyone’s job.
What’s the difference between ‘business continuity’ and ‘disaster recovery’?
Business continuity is about making sure the business can keep running, even if something bad happens, maybe by using backup plans. Disaster recovery is more about getting everything back to normal after a big problem, like fixing computers and systems that were damaged.
Why is it important to think about security right from the start when building new software or systems?
It’s much easier and cheaper to build security in from the beginning, like putting strong locks on a house when you’re building it, rather than trying to add them later. If we wait until the end, we might miss important security holes that hackers could use to get in.
