You know, we talk a lot about keeping our computers safe, right? We worry about viruses and hackers getting into our systems. But what if the threat isn’t just in the software we see every day? What if it’s deeper, in the very basic instructions that tell our hardware how to work? That’s where firmware persistence attack vectors come in. It’s a pretty scary thought, but understanding these hidden pathways is the first step to defending against them. Let’s break down how attackers can use firmware to stick around, even when you think you’ve cleaned things up.
Key Takeaways
- Firmware attacks are tough to deal with because they live on the hardware itself, surviving even when you reinstall your operating system.
- Rootkits and other firmware-level tools let attackers hide their actions and keep control of a system for a long time.
- Weaknesses in hardware, like flaws in the boot process or compromised parts from the start, create openings for attackers.
- Attackers use advanced tricks, sometimes even using normal system tools, to stay hidden and get around security measures.
- Problems in the supply chain, where components or software are made or delivered, can introduce firmware persistence attack vectors before a system is even used.
Understanding Firmware Persistence Attack Vectors
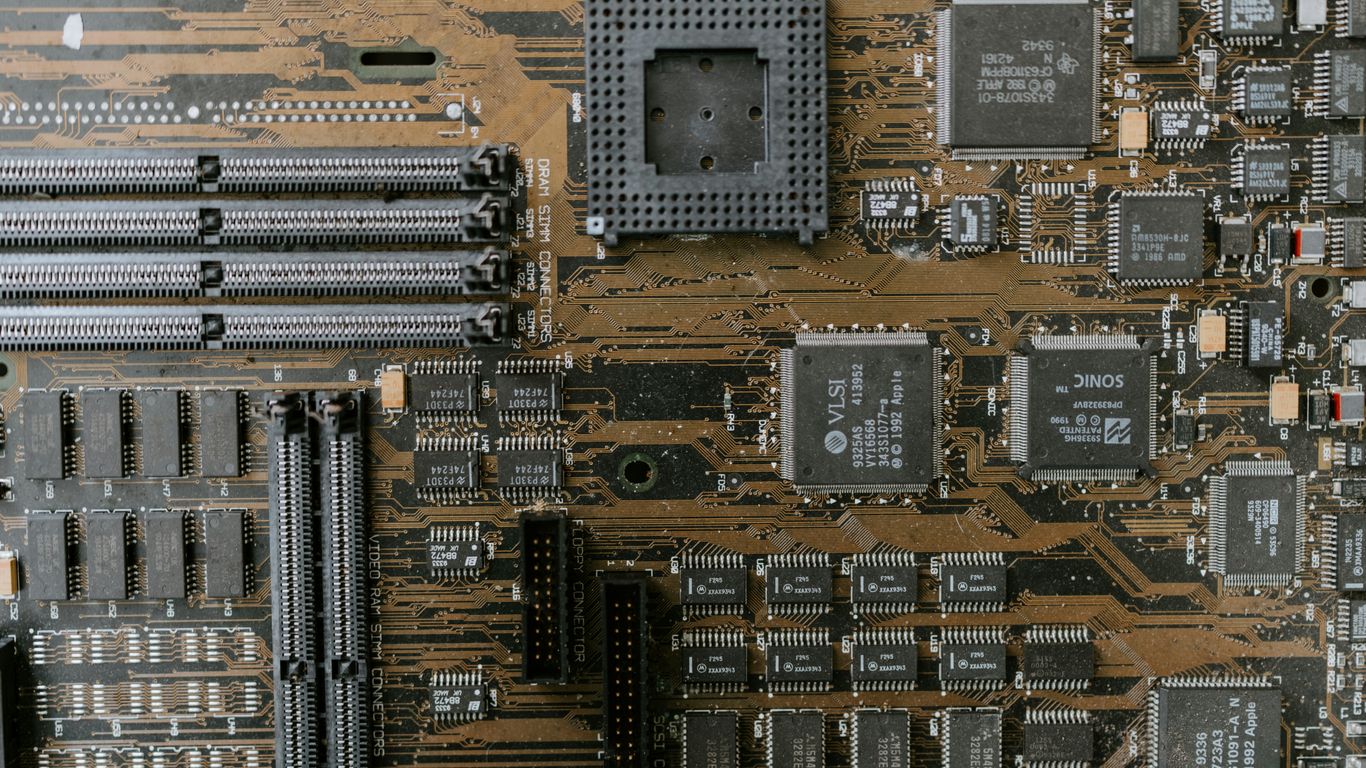
When we talk about computer security, we often focus on the software running on top, like the operating system or applications. But there’s a deeper layer, the firmware, that can also be a target for attackers. This is the low-level software that controls hardware components, like your BIOS or UEFI on a motherboard, or the firmware on network cards and storage devices.
Attacks targeting firmware are particularly concerning because they can survive even a complete operating system reinstallation. This means that even if you wipe your hard drive and install a fresh copy of Windows or macOS, the malicious firmware could still be lurking, waiting to re-infect your system. It’s like having a hidden problem in the foundation of a house that keeps causing issues no matter how many times you repaint the walls.
Here’s a look at some of the ways attackers can exploit firmware:
- BIOS/UEFI Compromise: The BIOS (Basic Input/Output System) or its modern successor, UEFI (Unified Extensible Firmware Interface), is the first software that runs when you turn on your computer. It initializes hardware and loads the operating system. If an attacker can compromise this, they can potentially control the boot process, load malicious code before the OS even starts, or disable security features. This is a serious threat because it happens at the earliest stage of system startup.
- Device Firmware Exploitation: Many hardware components have their own embedded firmware. Think about your network interface card (NIC), graphics card, or even your SSD. If this firmware can be modified, an attacker could potentially intercept network traffic, disable security controls on the device, or even cause the hardware to malfunction. This is a less common but still significant attack vector, especially with the increasing complexity of hardware.
- Supply Chain Compromise: Sometimes, the firmware can be compromised before the hardware even reaches you. This is a supply chain attack where malicious code is inserted during manufacturing or distribution. By the time you get the device, it’s already infected, making detection incredibly difficult. This is why supply chain attacks are so worrying; they exploit trust in legitimate vendors.
These types of attacks are difficult to detect with traditional security tools because they operate at a level below the operating system. Standard antivirus software often doesn’t have the visibility or capability to scan or monitor firmware effectively. This makes firmware persistence a challenging problem to solve, requiring specialized tools and a deep understanding of hardware security. It’s a reminder that security needs to be considered at every level of a system, not just the software we interact with daily. Understanding these attack vectors is the first step in building defenses against them, and it highlights the importance of secure boot processes and regular firmware updates when available. For more on advanced evasion techniques, you can look into stealthy operations.
Rootkits and Firmware Level Control
Rootkits are a particularly nasty class of malware. Their main goal is to hide malicious activity and keep attackers in control of a system, often for a long time. They’re designed to be stealthy, making them really hard to find. Think of them as the ultimate digital hide-and-seek champions.
Stealthy Malicious Activity Concealment
One of the primary functions of a rootkit is to mask the presence of other malicious software or processes. They achieve this by intercepting system calls and modifying the output that operating system utilities would normally provide. For instance, if you were to list running processes, a rootkit could filter out its own processes, making them invisible to standard tools like Task Manager or ps on Linux. This concealment extends to files, network connections, and even registry keys. This ability to hide makes initial detection incredibly challenging. It means that even if you suspect something is wrong, your usual methods of investigation might be completely blind to the actual threat.
Maintaining Privileged Access
Rootkits don’t just hide; they also ensure that the attacker maintains a high level of access. This often means operating at a privileged level, such as the kernel or, more insidiously, the firmware. By embedding themselves deep within the system’s core operations, they can resist attempts to remove them. Even if you try to clean up the operating system, the rootkit, residing in firmware, can reinfect or simply continue its operations undetected. This level of persistence is what makes firmware-level control so concerning. It’s like having a hidden landlord who controls the building’s foundation, regardless of who owns the apartments.
Kernel and Firmware Level Operations
When we talk about kernel-level operations, we’re referring to the core of the operating system. Malware that operates here has significant power. Firmware-level operations go even deeper, affecting the basic software that controls hardware components like the BIOS or UEFI. Compromising these layers means the malware can load before the operating system even starts, giving it ultimate control. This is a significant departure from traditional malware that might infect user applications or system files. It’s a way to achieve persistent access that survives OS reinstallation and even some hardware-level diagnostics. The implications for system integrity and security are profound, as the very foundation of trust in the system is undermined. For more on how attackers maintain access, understanding stealth persistence is key.
Hardware Vulnerabilities and Compromised Components
When we talk about security, we often focus on software, but the physical stuff matters too. Hardware vulnerabilities are a big deal because they can be really hard to fix, sometimes even impossible without replacing the component. Think about the basic instructions your computer or device runs on before the operating system even loads – that’s firmware.
Firmware Flaws and Insecure Boot Processes
Firmware is like the low-level software that controls hardware. If this firmware has bugs or backdoors, attackers can exploit it. A common problem is an insecure boot process. This is the sequence of events that happens when you turn on your device, loading the operating system. If this process isn’t protected, an attacker could potentially inject malicious code right at the start, before any security software even has a chance to run. This is a serious issue because it can bypass many standard security measures. This type of compromise can survive even a full operating system reinstallation.
- UEFI/BIOS Vulnerabilities: Flaws in the Unified Extensible Firmware Interface (UEFI) or Basic Input/Output System (BIOS) can allow attackers to gain control early in the boot sequence.
- Secure Boot Bypass: Attackers may find ways to circumvent secure boot mechanisms, which are designed to ensure only trusted software loads.
- Firmware Updates: Insecure firmware update processes can be exploited to install malicious firmware.
Hardware Backdoors and Side-Channel Attacks
Sometimes, hardware itself might have hidden ways in, known as backdoors. These could be intentionally placed by a manufacturer or introduced through a vulnerability. Then there are side-channel attacks. These don’t exploit a direct flaw in the code but rather observe physical characteristics of the hardware, like power consumption or electromagnetic emissions, to infer sensitive information. It’s a bit like listening to the clicks of a lock to figure out how to open it. These methods are quite advanced and often require physical access or very close proximity to the target system. Exploiting these can lead to privilege escalation chains that are difficult to detect.
Compromised Components in the Supply Chain
Another major concern is the supply chain. What if a component is compromised before it even reaches you? This could happen during manufacturing or shipping. A malicious actor might tamper with hardware, embedding malicious firmware or even hardware-level backdoors. When you install this compromised hardware, you’re unknowingly bringing the threat into your own environment. This makes it incredibly difficult to defend against, as the compromise is at the most fundamental level. It highlights the need for careful vetting of hardware sources and supply chain security practices.
The integrity of hardware components is paramount. A seemingly innocuous piece of hardware could harbor hidden vulnerabilities, making it a persistent threat vector that bypasses traditional software defenses.
Advanced Malware Techniques and Evasion
Modern malware authors are constantly developing new ways to sneak past security defenses. It’s not just about having a virus anymore; these threats are getting really sophisticated. One big area is fileless malware. Instead of dropping a file onto your system, it lives entirely in memory. This makes it super hard for traditional antivirus software to even see it, because there’s no file to scan. Think of it like a ghost – it’s there, but you can’t quite grab it.
Then there’s the whole ‘Living Off the Land’ (LotL) approach. This is where malware doesn’t bring its own tools. Instead, it uses legitimate programs already on your computer – like PowerShell or command prompt – to do its dirty work. It’s like a burglar using your own tools to break in. This makes it look like normal system activity, which is a big headache for detection systems. This tactic is particularly effective because it blends in with everyday operations.
Here’s a quick look at some common evasion methods:
- Fileless Execution: Malware resides only in RAM, avoiding disk-based scanning.
- Memory Injection: Malicious code is injected into the memory space of legitimate processes.
- Polymorphism/Metamorphism: Malware code changes its signature with each infection, making signature-based detection difficult.
- Living Off the Land (LotL): Abuses built-in system utilities for malicious purposes.
- Code Obfuscation: Deliberately making code harder to understand and analyze.
Attackers are always looking for ways to stay hidden. By using techniques that mimic normal system behavior or operate in ways that bypass standard file scanning, they can significantly increase their chances of success and prolong their presence on a compromised system. This makes detection a much more complex challenge than it used to be.
Another trick is polymorphic and metamorphic malware. These types of malware change their own code every time they infect a new system. It’s like a chameleon changing its colors. This means that even if security software recognizes one version, the next one it sees will look completely different, making signature-based detection almost useless. You can find more on these evolving threats by looking into advanced malware techniques.
These advanced methods mean that security solutions need to be smarter. They can’t just rely on knowing what a threat looks like; they need to understand what it’s doing. Behavioral analysis and anomaly detection are becoming more important than ever to catch these elusive threats. The constant evolution of malware means that staying ahead requires continuous adaptation and a multi-layered defense strategy, including looking at things like firmware security as a potential attack surface.
Supply Chain and Infrastructure Compromise
Compromising Software Dependencies
Think about it, software isn’t built in a vacuum these days. We rely on tons of libraries, frameworks, and pre-built components to get things done faster. That’s where the supply chain comes in. If an attacker can sneak something malicious into one of those common pieces of code, it can end up in countless applications without anyone realizing it. It’s like a virus spreading through shared resources. This is a huge problem because it means you could be running compromised code without even knowing it, just because you used a popular library.
- Malicious code injected into open-source libraries.
- Compromised build tools or development environments.
- Tampered software updates from trusted vendors.
These attacks exploit the trust we place in our development tools and partners. It’s a quiet way to get a foothold deep inside systems. We need to be really careful about what we pull into our projects. Checking the integrity of dependencies is becoming super important, and there are tools that can help with that, like software composition analysis.
Attacks on Vendor Integrations
Beyond just code libraries, many businesses integrate with third-party services and vendors. Think about cloud services, SaaS platforms, or even managed service providers. If one of these vendors gets compromised, it can directly impact your organization. Attackers might gain access to your data or systems through the established connection. It’s a bit like leaving a back door open because you trusted the delivery person. This is why vetting vendors and understanding their security posture is so important. You’re essentially inheriting their risks.
Firmware as a Supply Chain Attack Vector
This is where things get really tricky. Firmware, the low-level software that controls hardware, is another prime target. If an attacker can compromise the firmware of a component – say, a network card or a hard drive – before it even gets to you, that’s a supply chain attack. This kind of compromise is incredibly hard to detect because it happens before the operating system even loads. It can survive OS reinstallation and operate completely under the radar. Firmware-level compromises are some of the most persistent and difficult threats to deal with. It means that even a clean OS install might not be enough if the underlying hardware is already compromised. This is why secure boot processes and hardware integrity checks are so vital for protecting systems, especially critical ones like domain controllers.
Exploitation and Execution Pathways
Attackers don’t just find a way in; they need a solid plan to actually do something once they’re inside. This involves figuring out how to run their code and make it stick. It’s not always about finding some super-complex zero-day vulnerability. Often, the easiest routes are the ones that are overlooked.
Remote Code Execution Flaws
Remote Code Execution (RCE) vulnerabilities are like finding a master key. They let an attacker run commands on a target system from afar, without needing any prior access or special privileges. Think of a web server with a flaw that lets someone upload and execute a script. This is a direct pathway to getting malicious code running. These flaws pop up in all sorts of software, from web applications to network services.
- Buffer overflows: A classic. If a program doesn’t check how much data it’s receiving, an attacker can send too much, overwriting memory and potentially injecting their own code.
- Deserialization flaws: When applications aren’t careful about how they handle serialized data (data that’s been converted into a format for storage or transmission), attackers can send specially crafted objects that execute code when deserialized.
- Unpatched services: Many network services have known RCE vulnerabilities. If these aren’t patched, they’re just sitting there, waiting for someone to exploit them.
Exploiting Misconfigurations
Sometimes, the system itself is the weak link, not necessarily a specific software bug. Misconfigurations are everywhere, and they can open doors wide open. It’s like leaving your house unlocked because you forgot to close the back door after taking out the trash. Attackers love finding these. They might find an open network port that shouldn’t be, a service running with excessive permissions, or default credentials that were never changed. These aren’t always flashy exploits, but they are incredibly effective for gaining initial access or escalating privileges. For instance, leaving cloud storage buckets publicly accessible is a huge misconfiguration that can lead to massive data breaches.
Attackers often find that exploiting simple misconfigurations is far easier and less risky than developing complex exploits. These errors can stem from human oversight, rushed deployments, or a lack of proper security training.
Chaining Exploits for Increased Effectiveness
What’s better than one exploit? Several, used one after another. This is called exploit chaining. An attacker might use a less severe vulnerability to gain a foothold, then use that access to exploit another vulnerability that gives them higher privileges. Or they might chain an RCE flaw with a persistence mechanism. This makes the attack much harder to stop because you might detect one part, but the attacker has already moved on to the next stage. It’s a step-by-step process that builds on itself, allowing attackers to achieve goals that a single exploit wouldn’t allow. For example, an attacker might first exploit a web application vulnerability to gain access to a server, then use that access to exploit a local privilege escalation vulnerability to become an administrator. This layered approach is a hallmark of sophisticated attacks and is a key reason why defense in depth is so important.
Persistence Mechanisms Beyond Traditional Methods
When we talk about attackers sticking around on a system, we usually think about things like creating new user accounts or dropping files that start up when the computer boots. But the really persistent ones go much deeper. They know that just messing with the operating system is often not enough, especially if security teams are good at spotting those kinds of changes. So, they look for ways to embed themselves so deeply that even a full OS reinstall might not get rid of them.
Scheduled Tasks and Registry Modifications
Attackers often tweak existing, legitimate scheduled tasks. Instead of making a new one that might look suspicious, they’ll modify a task that already runs regularly. This is a clever way to get their code to run automatically, even after a reboot. It’s all about blending in with normal system operations. They’ll look for tasks that have high privileges or run frequently, then carefully change what they do. It’s a bit like hiding in plain sight. This is a common technique because it’s relatively easy to implement and can provide long-term access without raising too many alarms. The key is to modify existing, trusted entries rather than creating new ones.
Firmware-Level Control for Long-Term Access
This is where things get really serious. Firmware, like the BIOS or UEFI on a motherboard, or the firmware on network cards and hard drives, is the low-level software that makes hardware work. If an attacker can compromise this layer, they can achieve a level of persistence that’s incredibly hard to remove. Think about it: the operating system loads after the firmware. So, if the firmware itself is compromised, it can potentially reinfect the OS every time it starts up, or even hide the malware from the OS entirely. This is a major concern because firmware updates are not as common as OS patches, and detecting firmware-level compromise is much more difficult. It’s a way to maintain access even after the operating system has been wiped and reinstalled. This is why securing the boot process and verifying firmware integrity are so important.
Maintaining Access After Detection
Even if an attacker is detected, they might have fallback plans. This could involve having multiple persistence mechanisms in place, so if one is found and removed, others can take over. They might also use techniques that are hard to trace, like living off the land by using legitimate system tools for malicious purposes. The goal is to make it as difficult and time-consuming as possible for defenders to fully clean the system. Sometimes, the best defense is to have a solid plan for what to do when something is detected, and that includes knowing how to thoroughly eradicate any persistence the attacker might have established. It’s a constant cat-and-mouse game, and attackers are always looking for new ways to stay hidden and keep their foothold.
IoT and OT Vulnerabilities
When we talk about firmware persistence, it’s easy to get caught up in the world of traditional computers and servers. But the landscape of connected devices is vast, and that’s where Internet of Things (IoT) and Operational Technology (OT) systems come into play. These devices, often found in homes, smart cities, and industrial settings, present a unique set of challenges when it comes to security and, by extension, firmware persistence.
Insecure Communication Protocols
Many IoT and OT devices were designed with functionality and cost as primary drivers, not necessarily robust security. This often means they rely on older, less secure communication protocols. Think about it: if a device is sending data over a network without proper encryption or authentication, it’s like shouting your secrets across a crowded room. Attackers can easily intercept this traffic, potentially gaining insights or even injecting malicious commands. This lack of secure communication can be a direct pathway for attackers to gain initial access and then look for ways to establish persistence, perhaps by altering device firmware.
Lack of Vendor Support and Lifecycle Management
This is a big one. A lot of these devices, especially cheaper IoT gadgets, get deployed and then are largely forgotten. Vendors might stop providing security updates after a year or two, or sometimes, they never provided them in the first place. This leaves devices running on outdated firmware with known vulnerabilities. It’s like leaving your front door wide open and never planning to fix the lock. Attackers actively scan for these unpatched systems, and if they find a way in, they can exploit the firmware to maintain a persistent presence. This is especially problematic for OT systems where replacing hardware can be incredibly disruptive and expensive, leading to systems that are effectively unsupported for years. You can find more information on how attackers exploit remote services by scanning for open ports and default credentials.
Prioritizing Availability Over Security
In many OT environments, the primary goal is keeping the lights on, literally. Industrial control systems, for example, are designed for maximum uptime. A system going offline, even for a security patch, can have significant consequences, from production halts to safety risks. This focus on availability often means security measures, including firmware updates and robust security configurations, take a backseat. Attackers understand this. They know that in these environments, the tolerance for downtime is low, which can make them less likely to be detected if they can establish a persistent foothold without causing immediate disruption. This trade-off between availability and security creates a fertile ground for persistent threats.
Here’s a quick look at some common issues:
- Outdated Firmware: Devices running old versions with known exploits.
- Weak Authentication: Default or easily guessable passwords, or no authentication at all.
- Unencrypted Data: Sensitive information transmitted without protection.
- Limited Patching: Infrequent or non-existent security updates from vendors.
It’s a challenging situation, and the persistence mechanisms used in these environments can be quite sophisticated, often leveraging the very firmware that controls the device’s core functions. This makes them incredibly difficult to remove without a full system rebuild, if that’s even possible.
Third-Party and Supply Chain Risks
It’s easy to think about security as just what’s happening inside your own network, but a lot of risk actually comes from outside. We’re talking about the companies you work with, the software you buy, and even the hardware components that make up your systems. When you bring in a third-party service or use a piece of software developed by someone else, you’re essentially inheriting their security posture. If they have weak security, that weakness can become your weakness.
Think about it like this: you might have a super secure house, but if you hire a contractor to do some work and they leave a back door unlocked, your house isn’t secure anymore. It’s the same idea with supply chains. Attackers know this, so they often target the weaker links in the chain – the vendors or suppliers – to get to their bigger targets. This is a big reason why supply chain attacks have become so common. They can compromise software updates, libraries, or even hardware firmware, affecting many organizations at once.
Here are some common ways these risks show up:
- Compromised Software Dependencies: Using open-source libraries or third-party code means you’re trusting that code. If that code has a vulnerability or is intentionally backdoored, your system is at risk.
- Attacks on Vendor Integrations: When you connect your systems to a vendor’s platform or use their APIs, you’re creating a pathway. If the vendor’s security is weak, an attacker could use that connection to get into your network.
- Firmware as a Supply Chain Attack Vector: This is a really sneaky one. If the firmware on hardware components (like network cards or even motherboards) is compromised before it even gets to you, it can be incredibly hard to detect and can survive operating system reinstallation.
The challenge here is visibility. It’s tough to know exactly how secure every single vendor or piece of software is. You have to rely on trust, audits, and certifications, but even those aren’t foolproof. Attackers are getting really good at exploiting these trusted relationships.
Managing these risks means doing your homework. It involves looking closely at the security practices of your vendors, verifying the integrity of software and updates, and having clear contractual agreements about security responsibilities. It’s an ongoing effort, not a one-time check. Keeping up with vendor security assessments is key.
Legacy Systems and Patch Management Gaps
Older systems, bless their hearts, are often a real headache when it comes to security. Think about that old server humming away in the corner, running software that hasn’t seen an update since, well, who knows when. These systems are like open doors for attackers because they usually don’t get the latest security fixes. It’s not always the company’s fault, though. Sometimes, updating that old software could break everything else, and testing takes ages. Plus, finding people who even know how to manage these ancient beasts can be tough.
Lack of Vendor Support and Modern Security Controls
When vendors stop supporting a product, they stop releasing patches. That means any new vulnerabilities discovered after that point are basically left wide open. Modern security tools and techniques often just don’t work with these older systems, leaving them exposed. It’s like trying to put a brand-new lock on a door that’s already falling off its hinges.
Delayed or Inconsistent Patching
Patch management is a big deal, right? It’s about getting those security updates out there. But with legacy systems, patching can be a real mess. Updates might come late, or not at all, or maybe only some systems get patched. This inconsistency creates a patchwork quilt of security, with some parts strong and others full of holes. Attackers love this kind of environment because they can just look for the weakest link. A robust patch management process is key, but it’s often harder to implement on older infrastructure.
Accumulated Vulnerabilities Over Time
Over the years, these systems just keep collecting vulnerabilities. Each new flaw discovered is another potential entry point. Without regular updates, these issues don’t get fixed. It’s a bit like never cleaning your house – eventually, it just becomes a mess. This accumulation makes them prime targets, and the longer they’re left unpatched, the more attractive they become to anyone looking to cause trouble. It really highlights the need for a solid vulnerability management strategy across the board.
Wrapping Up: Firmware’s Role in Security
So, we’ve talked a lot about how attackers can get into systems, sometimes in ways that are really hard to find, like messing with the firmware. It’s not just about patching your software anymore. These low-level attacks can stick around even if you wipe everything and start fresh. It really shows that keeping systems safe means looking at all the layers, from the operating system all the way down to the hardware’s basic instructions. Paying attention to firmware security, keeping it updated, and using things like secure boot can make a big difference in stopping some of the nastier, more persistent threats out there. It’s a complex area, for sure, but ignoring it leaves a pretty big hole in your defenses.
Frequently Asked Questions
What exactly is firmware, and why is it a target for hackers?
Firmware is like the basic software that tells hardware, such as your computer’s motherboard or graphics card, how to work. Hackers target it because if they can change the firmware, they can control the hardware in ways that are very hard to detect, even if you reinstall your operating system. It’s like changing the instructions for a machine at its core.
How can hackers make their malicious programs hide using firmware?
When hackers mess with firmware, they can create secret ‘backdoors’ or hide their malicious programs. These hidden programs can run without being seen by normal security software. It’s like having a secret room in your house that no one knows about, where you can do things without anyone noticing.
What are firmware attack vectors?
Firmware attack vectors are the different ways hackers try to get into and control the firmware. This could be by finding mistakes in the firmware’s code, tricking the system during startup, or even by tampering with computer parts before they even reach you, like during manufacturing.
Can a hacker’s firmware attack survive if I completely wipe my computer and reinstall everything?
Yes, that’s the scary part about firmware attacks. Since the firmware is separate from the main operating system (like Windows or macOS), changing the firmware can mean the malicious code stays even after you reinstall everything. It’s like the foundation of a house being rotten, even if you repaint the walls.
What is a rootkit, and how does it relate to firmware?
A rootkit is a type of software designed to hide itself and other malicious programs. Some advanced rootkits can actually infect the firmware. This makes them incredibly difficult to find and remove because they operate at a very low level of the computer’s system.
How do hardware flaws make firmware attacks possible?
Sometimes, the physical parts of a computer or device have weaknesses, or ‘flaws,’ in their design or the software (firmware) that controls them. Hackers can use these flaws, like mistakes in how the system starts up (the boot process), to gain control and install their own hidden programs.
What does it mean if a component is ‘compromised in the supply chain’?
This means that a computer part or piece of software was tampered with *before* it even got to you. For example, a hacker might secretly add malicious firmware to a chip while it’s being made or shipped. When you install it, the hidden bad code is already there.
Why are devices like smart home gadgets (IoT) often vulnerable to firmware attacks?
Many smart devices are made quickly and cheaply. They might not get regular security updates, have weak passwords, or use insecure ways to talk to each other. This makes their firmware easier for hackers to attack and control, especially since companies might stop supporting older devices.
