When it comes to keeping sensitive information safe, key rotation enforcement systems are a big deal. Companies rely on these systems to make sure cryptographic keys don’t stick around longer than they should. Letting keys get old or forgotten is risky business—attackers love stale keys. Regularly swapping out keys, tracking their use, and making the process as smooth as possible helps keep data secure and headaches to a minimum. Here’s what you need to know about building a strong approach to key rotation enforcement systems.
Key Takeaways
- Key rotation enforcement systems help prevent attackers from using old or compromised cryptographic keys.
- Automating key rotation reduces the chances of human error and keeps the process consistent.
- Regular audits and monitoring of key usage can catch strange activity before it turns into a bigger problem.
- Integrating key rotation into daily security routines makes it easier to stay compliant and secure.
- Clear policies and easy-to-follow steps encourage everyone in the company to stick to good key management practices.
Establishing Robust Key Management Practices
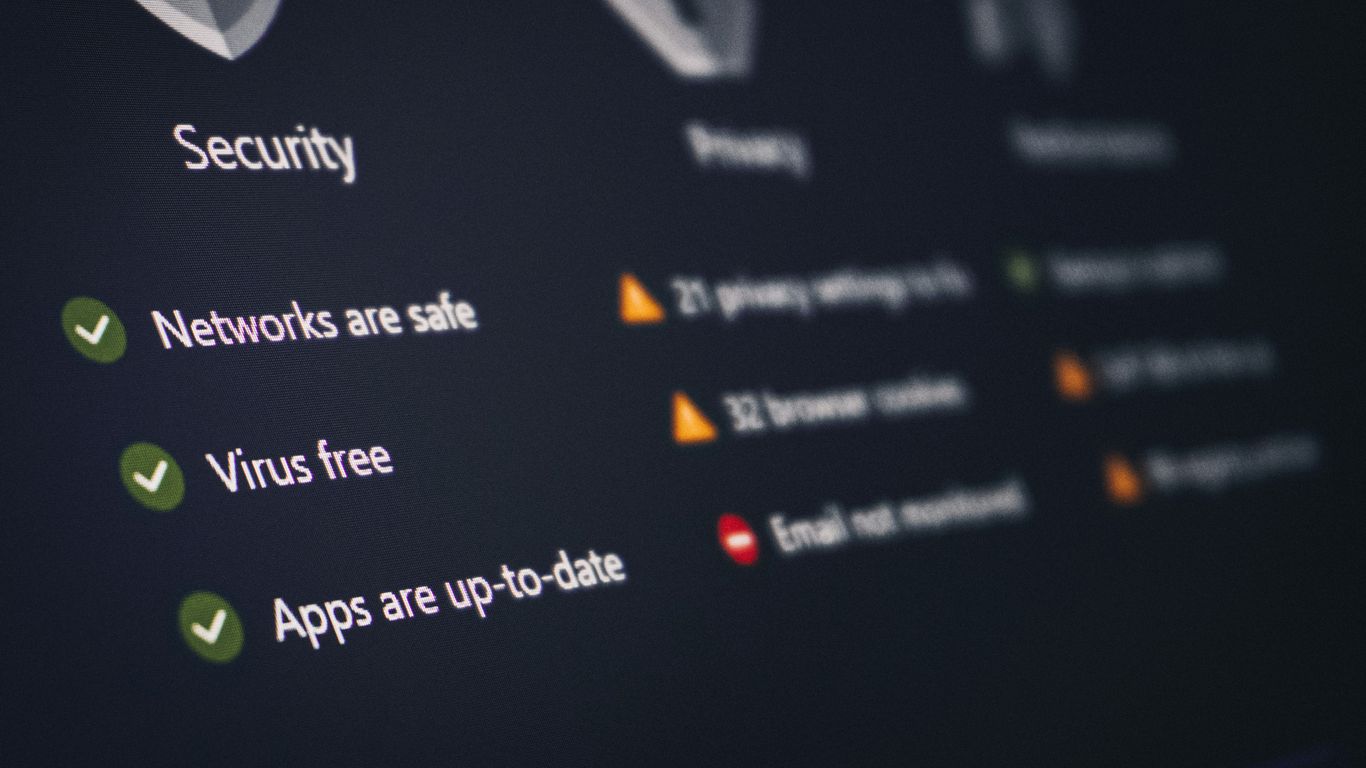
When we talk about keeping our digital stuff safe, we often focus on firewalls and antivirus, right? But there’s a whole other layer that’s super important, and that’s how we handle our cryptographic keys. Think of these keys like the master keys to your most valuable digital vaults. If they fall into the wrong hands, or if they’re not managed properly, all the other security measures can become pretty useless.
The Role of Key Management Systems
So, what exactly is a Key Management System (KMS)? Basically, it’s a system designed to handle the entire life cycle of your cryptographic keys. This means generating them securely, storing them safely, knowing when to rotate them out, and how to get rid of them when they’re no longer needed. Without a solid KMS, you’re basically leaving your digital doors unlocked. It’s not just about having keys; it’s about controlling them. A good KMS helps make sure your encryption actually works the way it’s supposed to, which is pretty vital for keeping data private. You can find more about how these systems work in relation to encryption effectiveness.
Secure Generation and Storage of Cryptographic Keys
It all starts with how you make these keys. They need to be generated using strong, random processes. You can’t just make up a key; it needs to be unpredictable. Then comes storage. Storing keys securely is a big deal. They shouldn’t be sitting in plain text files on a server or, worse, on someone’s laptop. Specialized hardware, like Hardware Security Modules (HSMs), or secure software vaults are typically used. This keeps them protected from unauthorized access, even if other parts of your system get compromised. It’s about making sure that even if someone gets into your network, they can’t just grab the keys to everything.
The Necessity of Regular Key Rotation
Keys, like anything else, can become a risk over time. Maybe a key has been in use for a very long time, increasing the chances it could be discovered or brute-forced. Or perhaps there’s a suspicion that a key might have been exposed, even if you can’t prove it. This is where key rotation comes in. It’s the practice of regularly replacing old keys with new ones. This limits the window of opportunity for attackers. If an old key is compromised, the damage is contained to the period that key was active. It’s a proactive step that significantly reduces risk. Think of it like changing the locks on your house every few years – it’s just good practice.
Here’s a quick look at why rotation matters:
- Limits Exposure Window: If a key is compromised, the period of potential data exposure is reduced.
- Mitigates Brute-Force Attacks: Longer-lived keys are more susceptible to brute-force or cryptanalytic attacks.
- Supports Compliance: Many regulations require regular key rotation as a security control.
- Reduces Impact of Insider Threats: Limits the duration an insider could misuse a compromised key.
Managing keys isn’t a set-it-and-forget-it task. It requires ongoing attention and a structured approach to keep your data protected. Ignoring this aspect can leave even the most sophisticated security systems vulnerable.
Proper credential management, which includes key rotation, is a cornerstone of good security hygiene. It’s not just about passwords; it’s about all the secret pieces of information that grant access. You can learn more about effective credential management to see how it ties into the broader picture.
Understanding the Evolution of Security Threats
It feels like every week there’s a new headline about a massive data breach or a crippling cyberattack. The landscape of digital threats isn’t just changing; it’s accelerating. Attackers are getting smarter, more organized, and frankly, more brazen. We’re not just talking about random hackers anymore; we’re seeing sophisticated groups, sometimes backed by states, with serious resources.
Ransomware and Double Extortion Tactics
Ransomware used to be about locking up your files and demanding a payout. Simple, if terrifying. But that’s old news. Now, attackers often steal your data before they encrypt it. Then, they threaten to leak it publicly if you don’t pay. This "double extortion" tactic adds a whole new layer of pressure, making organizations think twice about just restoring from backups. Some even go for "triple extortion," adding DDoS attacks or contacting customers directly to pile on the misery. It’s a nasty business, and it means defenses need to be way more robust than just having good backups. The rise of Ransomware-as-a-Service (RaaS) also means that even less skilled individuals can launch these attacks, making the threat more widespread than ever. We’ve seen how this can impact businesses, and it’s a serious concern for any organization.
The Rise of Supply Chain Attacks
Another trend that’s really taken off is the supply chain attack. Instead of trying to break directly into a company’s network, attackers go after a trusted vendor or software provider. Think about it: if a hacker can compromise the update mechanism for a widely used software, they can potentially infect thousands of organizations all at once. It’s like poisoning the well. These attacks exploit the trust we place in our partners and the software we rely on. It means we can’t just focus on our own defenses; we have to think about the security posture of everyone in our digital supply chain. This is a complex problem that requires a lot of visibility into third-party relationships.
Evolving Threat Actor Motivations and Capabilities
What’s driving all this? For many, it’s pure financial gain. Cybercrime is a massive industry. But it’s not just about money. Nation-states are increasingly involved, using cyberattacks for espionage, disruption, or political leverage. Hacktivists are also out there, motivated by ideology. And we can’t forget insider threats – people within an organization who misuse their access, intentionally or not. The capabilities of these actors are also growing. They’re using automation, AI for more convincing social engineering, and advanced techniques to stay hidden. It means our defenses need to keep pace, constantly adapting to new methods and motivations.
Implementing Identity-Centric Security Models
Identity as the New Security Perimeter
Forget the old idea of a castle with a moat. In today’s world, the network perimeter isn’t really the main defense anymore. Think about it: people work from home, use cloud apps, and access systems from all sorts of devices. This means the identity of the user and the device is what really matters for security. It’s like the digital ID card that grants access. We need to make sure that only the right people, using the right devices, can get to the right information. This shift means we have to rethink how we control access entirely. It’s not just about blocking bad guys from getting in; it’s about constantly checking who’s already inside and what they’re allowed to do. This is why identity security has become so important, moving beyond just passwords to more advanced ways of verifying who someone is. Identity is the new frontier.
Strengthening Authentication and Authorization
So, if identity is the new perimeter, how do we actually make it strong? It comes down to two main things: authentication and authorization. Authentication is proving you are who you say you are. Passwords alone just don’t cut it anymore. We’re talking about multi-factor authentication (MFA), which requires more than just a password – maybe a code from your phone or a fingerprint scan. It’s a basic step that makes a huge difference. Authorization, on the other hand, is about what you’re allowed to do once you’re in. This is where the principle of least privilege comes in. You should only have access to exactly what you need to do your job, and nothing more. If your job doesn’t involve looking at HR records, you shouldn’t have access to them, plain and simple. This limits the damage if an account gets compromised.
Here’s a quick look at how these work together:
- Authentication: Verifying identity (e.g., password + MFA).
- Authorization: Determining access rights based on verified identity and role.
- Least Privilege: Granting only necessary permissions.
The Growing Adoption of Passwordless Technologies
Because passwords are such a pain and a security risk, a lot of places are moving towards passwordless options. This isn’t just a futuristic idea; it’s happening now. Think about using your fingerprint to log into your phone or a special security key to access sensitive systems. These methods are often more secure than passwords because they’re harder to steal or guess. Plus, they can be more convenient for users. While it might seem like a big change, the benefits in terms of security and user experience are pretty significant. It’s all part of building a more robust system where we don’t rely on something as fragile as a password. Strong IAM is foundational.
Moving to an identity-centric model means we’re constantly verifying, not just assuming trust. Every access request, from any user or device, needs to be checked against policies. This continuous verification is key to stopping threats before they can spread.
Addressing Human Factors in Security
Look, we build all these fancy firewalls and intrusion detection systems, but sometimes, the biggest hole in our security isn’t a piece of code; it’s us. People. We get tired, we get distracted, we make mistakes. It’s just how it is. Ignoring this is like building a fortress but leaving the main gate wide open because you assume everyone inside is a saint.
Mitigating Security Fatigue Through Usable Controls
Ever feel like you’re drowning in alerts? That’s security fatigue, and it’s a real problem. When people are constantly bombarded with warnings, they start to tune them out. It’s like the boy who cried wolf, but with more pop-up windows. The trick here is to make security controls actually usable. If logging in requires a ten-step process every single time, people will find ways around it, and not in a good way. We need systems that are protective without being overly burdensome. Think about it: if a security measure is too complicated, people will just try to get their work done faster, often by skipping steps. This is why user-friendly design in security tools isn’t just a nice-to-have; it’s a necessity. We’re seeing a shift towards more intuitive interfaces and fewer, more meaningful alerts. It’s about making the right thing to do the easy thing to do.
Encouraging Reporting of Suspicious Activity
When something looks off, people should feel comfortable speaking up. But often, they don’t. Why? Fear of getting in trouble, not wanting to bother anyone, or simply not knowing how to report it. We need to create an environment where reporting is seen as a positive contribution, not a complaint. This means having clear, simple ways to report suspicious emails or activities, and importantly, providing feedback. Let people know their reports were received and, if appropriate, what happened. This reinforces the behavior and shows that their vigilance matters. A good way to start is by establishing clear reporting channels and making sure everyone knows about them. It’s a simple step, but it can make a big difference in catching threats early, before they become major problems. Remember, your employees are often the first line of defense, so let’s make sure they feel equipped and encouraged to act.
Overcoming Resistance to Security Change
Change is hard, and security changes can feel particularly disruptive. People get used to their routines, and introducing new policies or tools can feel like an annoyance. It’s not always about malice; it’s often just inertia. To get past this, communication is key. Explain why the change is happening, what the risks are if we don’t change, and how the new process will ultimately benefit everyone. Leadership needs to visibly support these changes, too. If the boss isn’t on board, why should anyone else be? We also need to consider the timing and rollout. Big, sudden changes can be overwhelming. Breaking them down into smaller, manageable steps, and providing adequate training and support, can make a world of difference. Think about how you’d introduce a new piece of software at work – you wouldn’t just drop it on everyone’s desk without instructions, right? Security changes should be treated with the same care. It’s about guiding people through the transition, not just dictating it. For instance, when implementing new access controls, clearly outlining the benefits and providing hands-on training can significantly reduce pushback and improve adoption. This approach helps build trust and makes people feel more invested in the security of the organization. Managing service account risk is one area where clear communication about new procedures is vital.
Securing the Evolving Remote Workforce
Working from home has become the norm for many, and it’s changed how we think about security. It’s not just about locking down the office anymore. We’ve got people working from all sorts of places, using different networks and devices, which opens up new challenges.
Adapting Security Strategies for Remote Work
The shift to remote work means our old security plans might not cut it. We need to rethink how we protect our data and systems when employees aren’t behind the company firewall. This involves looking at everything from how people connect to the network to the devices they use. It’s about building security into the way people work, not just layering it on top. We need to make sure that access controls are strong, even when someone is connecting from their home Wi-Fi. This often means adopting new technologies and updating policies to match the reality of a distributed workforce. It’s a big change, and it requires a flexible approach.
The Criticality of Endpoint Security
When everyone is working remotely, their laptops and phones become the new front lines. If an endpoint gets compromised, it’s like an attacker walking right into the office. That’s why endpoint security is so important now. We’re talking about making sure devices are up-to-date with security patches, have strong antivirus software, and are configured securely. Tools like Mobile Device Management (MDM) and Mobile Threat Defense (MTD) can help manage and protect these devices, whether they’re company-issued or personal devices used for work. It’s a constant effort to keep these endpoints safe from threats like malware and unauthorized access. We need to make sure that even if a device is lost or stolen, the data on it is protected.
Managing Risks Associated with Home Networks and Devices
Home networks and personal devices present a unique set of risks. Unlike a controlled office environment, home networks can be less secure, and personal devices might not have the same security measures in place. Think about shared Wi-Fi networks or family members using the same computer for personal browsing and work tasks. This is where clear guidelines and training become really important. We need to educate employees on best practices for securing their home networks, like using strong Wi-Fi passwords and keeping router firmware updated. For personal devices used for work, implementing policies around data segregation and ensuring devices meet certain security standards is key. It’s about reducing the chances of a compromise on a personal device spilling over into the company network. Proper account deprovisioning is also vital when employees leave, to prevent orphaned accounts from becoming a security risk [3fb4].
Here’s a quick look at common remote work security concerns:
| Concern | Potential Impact |
|---|---|
| Unsecured Home Wi-Fi | Unauthorized network access, data interception |
| Personal Device Malware | Compromise of work data, spread to company network |
| Lack of Updates | Exploitable vulnerabilities on endpoints |
| Shared Devices | Data leakage, unauthorized access to work accounts |
| Weak Authentication | Account takeover, lateral movement |
Leveraging Automation in Security Operations
Security teams are often swamped with repetitive tasks. Think about sifting through endless logs, triaging alerts, or even basic incident containment steps. This is where automation really shines. It’s not about replacing people, but about giving them better tools to do their jobs more effectively. By automating these routine processes, security professionals can spend less time on busywork and more time on the complex threats that actually need human insight.
Reducing Manual Workloads with Automated Workflows
Manual security tasks are a huge drain on resources. Automation can take over many of these, freeing up your team. Imagine workflows that automatically scan for vulnerabilities, patch systems, or even isolate a compromised endpoint the moment it’s detected. This isn’t science fiction; it’s becoming standard practice. Tools that integrate with your existing security stack can orchestrate these actions, making your defenses more responsive.
- Automated alert triage to filter out noise.
- Automated patching and configuration management to address known weaknesses.
- Automated response actions for common incident types.
Automating security governance enhances efficiency, reliability, and scalability in security operations. By automating routine tasks like alert triage, incident containment, and control testing, security teams can focus on complex threats and strategic initiatives. This leads to faster detection and response times, reduced human error, and the ability to manage growing digital footprints without proportional increases in staff. Automation also streamlines control definition, implementation, testing, and ensures accountability, creating a more robust and adaptable security posture. Automating security governance
Improving Incident Response Times Through Automation
When an incident happens, every second counts. Automation can drastically cut down the time it takes to respond. Instead of manually gathering information, checking logs, and executing containment steps, automated playbooks can do it in minutes, or even seconds. This speed is critical for limiting the damage an attacker can do. Think about how much faster you could recover from a ransomware attack if your systems could automatically isolate infected machines and initiate recovery processes.
Scalability Benefits of Automated Security Processes
As organizations grow and their digital footprints expand, security teams often struggle to keep up without a proportional increase in staff. Automation provides a way to scale security operations effectively. Automated workflows can handle a much larger volume of alerts and incidents than manual processes ever could. This means your security posture can grow with the business, rather than becoming a bottleneck. It also helps maintain consistency in your security practices, regardless of the scale.
| Task Category | Manual Time (Est.) | Automated Time (Est.) |
|---|---|---|
| Alert Triage | 15-30 mins/alert | < 1 min/alert |
| Endpoint Containment | 30-60 mins/incident | < 5 mins/incident |
| Vulnerability Scanning | Hours/Week | Continuous/Scheduled |
Implementing robust technical controls is also key. This includes effective patch management strategies to keep software updated, addressing vulnerabilities before they can be exploited. Automation is key for efficient patching. Additionally, configuration management is crucial to ensure systems are set up securely according to defined baselines, preventing unauthorized changes and reducing attack surfaces. Continuous monitoring and enforcement are vital for maintaining a secure environment. patch management strategies
Enhancing Detection and Response Capabilities
When preventive measures don’t quite stop an intrusion, having solid detection and response plans in place is your next line of defense. It’s all about spotting trouble early and acting fast to minimize damage. Think of it like having a good alarm system and a quick-response team ready to go.
The Importance of Security Information and Event Management (SIEM)
Security Information and Event Management (SIEM) systems are pretty central to this. They pull in logs and event data from all over your network – servers, firewalls, applications, you name it. By collecting all this information in one place, SIEM tools can correlate events, spot suspicious patterns, and generate alerts. This gives you a much clearer picture of what’s happening across your entire IT environment. Without good log collection and analysis, you’re basically flying blind when it comes to detecting threats that slip past your initial defenses. It’s a big job, but having a well-tuned SIEM makes a huge difference in spotting those subtle signs of compromise. You can check out how SIEM works to get a better grasp.
Streamlining Incident Response with Orchestration and Automation
Once a potential incident is flagged, speed is key. This is where security orchestration and automation come into play. These tools can automate repetitive tasks, like isolating an infected machine or blocking a malicious IP address. This frees up your security team to focus on more complex investigations and decision-making. Imagine a playbook that automatically kicks off when a certain type of alert fires – that’s the power of automation. It helps make sure that responses are consistent and timely, no matter who is on duty. Coordinating these efforts, especially with things like purple team exercises, can really sharpen your team’s ability to react effectively. It’s about making sure your playbooks are up-to-date and that your tools work together smoothly to eliminate blind spots.
Continuous Monitoring for Anomaly Detection
Detection isn’t a one-time thing; it needs to be ongoing. Continuous monitoring means constantly watching for deviations from normal behavior. This is where anomaly detection shines. Instead of just looking for known bad stuff (like viruses with specific signatures), anomaly detection looks for anything that’s out of the ordinary. This could be a user logging in from an unusual location, a server suddenly using a lot more network bandwidth, or a process behaving strangely. While it can sometimes generate false alarms, when tuned correctly, it’s incredibly effective at catching novel threats that signature-based systems might miss. Keeping an eye on things 24/7 is the goal here.
Here’s a quick look at what makes detection and response effective:
- Visibility: Having access to logs and telemetry from all your systems.
- Correlation: The ability to link related events together to see the bigger picture.
- Timeliness: Acting quickly once a threat is identified.
- Automation: Using tools to speed up routine response actions.
Effective detection and response isn’t just about having the right tools; it’s about having well-defined processes and skilled people who know how to use those tools. It requires constant tuning and adaptation as threats evolve and your own environment changes. Without this, even the best technology can fall short when it matters most.
Proactive Vulnerability and Risk Management
Keeping your digital assets safe means constantly looking for weak spots before the bad guys do. It’s like doing regular check-ups on your home’s security system, making sure all the locks are good and there are no easy ways in. This isn’t a one-time thing; it’s an ongoing process.
Identifying and Prioritizing Security Weaknesses
First off, you need to know what you’re even looking for. This involves scanning your systems, applications, and networks for known flaws. Think of it as a detailed inventory of every potential entry point. Once you find these weaknesses, you can’t just fix them all at once, right? Resources are limited. So, you have to figure out which ones are the most dangerous. This means looking at how likely a vulnerability is to be exploited and what kind of damage it could cause if it is. A small, hard-to-reach flaw might be less of a worry than a widely known issue on a critical server.
- Regular System Scanning: Use automated tools to find vulnerabilities.
- Threat Intelligence: Keep up with what attackers are currently targeting.
- Risk Assessment: Score vulnerabilities based on exploitability and impact.
Prioritizing risks helps focus your efforts where they matter most, preventing a scattershot approach to security.
Reducing the Attack Surface Through Remediation
Once you’ve figured out what needs fixing, you actually have to fix it. This is the remediation part. It could mean patching software, changing configurations, or even removing unnecessary services that just sit there, waiting to be exploited. Every bit of cleanup you do shrinks the area an attacker can target. It’s about making your systems less appealing and harder to break into. For instance, closing unused network ports or disabling old, unneeded software makes a big difference. You can find more on managing these kinds of issues by looking at account provisioning practices.
Integrating Vulnerability Management into Security Posture
This whole process of finding and fixing weaknesses shouldn’t be a side project. It needs to be a core part of how you do security every day. That means making sure it’s part of your regular operations, not just something you do when there’s a major incident. Tracking your progress, from finding a vulnerability to confirming it’s fixed, is key. This continuous loop of scanning and fixing helps you stay ahead of the curve and keeps your overall security strong. It’s about building a resilient environment that can withstand the constant pressure from attackers.
The Imperative of Data Encryption and Integrity
Protecting your digital assets means more than just keeping attackers out. It’s also about making sure the data you have is accurate and hasn’t been messed with, and that sensitive information stays private. This is where data encryption and integrity checks come into play.
Protecting Information with Cryptographic Algorithms
At its core, data encryption is like putting your information into a secret code. You use special mathematical processes, called cryptographic algorithms, to scramble your data so it looks like gibberish to anyone who doesn’t have the right key. This is super important for keeping things confidential. Think about customer records or financial details; if those fall into the wrong hands, it’s a big problem. Encryption stops that from happening, even if someone manages to steal the data itself. It’s a key part of keeping sensitive information safe from prying eyes.
Ensuring Confidentiality of Data at Rest and in Transit
Data isn’t always on the move; sometimes it’s just sitting there, and sometimes it’s being sent across networks. Encryption needs to cover both scenarios. When data is at rest, meaning it’s stored on hard drives, servers, or in the cloud, encryption keeps it protected. If a server gets stolen or a database is breached, the data remains unreadable. When data is in transit, like when you’re sending an email or accessing a website, encryption protocols like TLS scramble it as it travels. This prevents anyone from intercepting and reading it along the way. It’s a two-pronged approach to keeping your information private.
The Role of Key Management in Encryption Effectiveness
Encryption is only as good as the keys used to scramble and unscramble the data. If those keys are weak, lost, or stolen, your encryption is useless. This is where key management comes in. It’s the whole process of creating, storing, using, rotating, and destroying those encryption keys securely. Without a solid key management system, your encryption efforts can fall apart. It’s not just about using strong algorithms; it’s about managing the keys that make those algorithms work. Proper key management is absolutely vital for encryption to actually do its job effectively. You can find more on data classification which helps determine what needs this level of protection.
Here’s a quick look at why key management matters:
| Aspect | Description |
|---|---|
| Key Generation | Creating strong, unpredictable keys. |
| Secure Storage | Protecting keys from unauthorized access. |
| Key Rotation | Regularly changing keys to limit exposure if one is compromised. |
| Access Control | Limiting who can use specific keys. |
| Auditing | Tracking key usage to detect suspicious activity. |
Ultimately, encryption and integrity checks are not optional extras; they are fundamental requirements for any organization serious about protecting its data in today’s threat landscape. Ignoring them is like leaving your front door wide open.
Strategies for Preventing Privilege Misuse

When we talk about security, it’s easy to get caught up in the technical stuff, like firewalls and encryption. But sometimes, the biggest risks come from within. Privilege misuse is a big one. It’s not always about malicious intent; often, it’s just about having more access than you really need.
Enforcing Least Privilege Principles
This is probably the most talked-about strategy, and for good reason. The idea is simple: give people and systems only the permissions they absolutely need to do their job, and nothing more. Think of it like giving a contractor a key to your house – you wouldn’t give them a key to your safe, right? It’s the same principle. This means carefully defining roles and making sure those roles have the minimum necessary access. It really cuts down on the potential damage if an account gets compromised or if someone makes a mistake.
- Define roles clearly: What does each job function actually require?
- Assign permissions based on roles: Don’t give out admin rights like candy.
- Regularly review permissions: People change roles, projects end, and access needs to be adjusted.
Managing Excessive Permissions and Access Exposure
Even with a least privilege approach, things can get out of hand. Over time, accounts might accumulate permissions they no longer need. This is where active management comes in. We need to look for these situations and clean them up. It’s about reducing the overall attack surface by making sure no single account has too much power. This is especially important for accounts that have high-level access, like administrators or service accounts. If one of these gets compromised, the fallout can be massive. Tools that help manage privileged access can be a lifesaver here, keeping track of who has what and flagging anything unusual. You can find more on managing privileged access to help with this.
The Role of Privileged Access Management Systems
These systems are designed specifically to tackle the challenges of privileged accounts. They don’t just grant access; they control, monitor, and audit it. Think of them as a security guard for your most sensitive digital doors. They can enforce things like just-in-time access (you only get the permission when you need it, for a limited time) and session recording, so you can see exactly what someone did while they had elevated privileges. This level of oversight is pretty critical for preventing misuse and for investigating incidents if they do occur. It’s a proactive way to handle a high-risk area, and it’s becoming a standard part of a strong security setup for many organizations.
Managing privileged access is not a one-time task. It requires ongoing attention, regular audits, and a commitment to refining policies as threats and business needs evolve. Ignoring this area leaves a significant gap in your defenses.
Here’s a quick look at how excessive permissions can increase risk:
| Permission Level | Potential Impact of Misuse |
|---|---|
| Administrator | Full system compromise, data exfiltration, disabling security controls |
| Standard User | Limited data access, potential for malware execution |
| Service Account | Access to applications and databases, potential for lateral movement |
By limiting these permissions, we significantly reduce the potential damage from privilege escalation or accidental misuse.
Building a Strong Security Culture
Think of security like a team sport. You can have the best equipment and the most skilled players, but if everyone isn’t on the same page, working together, you’re not going to win. That’s pretty much how it is with cybersecurity. It’s not just about firewalls and antivirus software; it’s about the people using those tools and systems every day. A strong security culture means everyone, from the intern to the CEO, understands their role in protecting the organization. It’s about making security a shared responsibility, not just an IT department problem.
Fostering Shared Values and Responsible Behaviors
So, how do you get everyone to care? It starts with making security relevant to their daily work. Instead of just handing out a thick policy document, break down what it means for different roles. For example, someone in marketing needs to know about protecting customer data and avoiding social engineering, while a developer needs to focus on secure coding practices. It’s about connecting the dots between their actions and the bigger picture of organizational security. We need to move beyond just telling people what not to do and start showing them why it matters and how they can contribute positively. This involves clear communication about threats and the impact of security incidents, making the abstract concept of cybersecurity feel more concrete and personal.
The Critical Influence of Leadership Commitment
If the leaders aren’t visibly committed to security, why should anyone else be? When executives talk about security, allocate resources to it, and follow the rules themselves, it sends a powerful message. It shows that security isn’t just a checkbox item; it’s a core business priority. This commitment needs to be more than just words; it needs to be demonstrated through actions. Think about it: if leadership consistently bypasses security protocols for convenience, it undermines the entire effort. Leaders need to champion security initiatives, support training programs, and hold themselves and others accountable. This visible support is key to building a strong foundation for any security transformation.
Integrating Security Awareness into Daily Operations
Security awareness shouldn’t be a one-off training session during onboarding. It needs to be woven into the fabric of daily operations. This means regular, bite-sized updates on new threats, reminders about best practices, and making it easy for people to report suspicious activity without fear of reprisal. For instance, having a simple, clear process for reporting phishing attempts can make a huge difference. When people feel comfortable speaking up, it helps with early detection of threats, which is often the most critical step in mitigating damage. It’s about creating an environment where asking questions about security is encouraged, not seen as a sign of weakness.
Here are a few ways to integrate security awareness:
- **Regular
Implementing Effective Key Rotation Enforcement Systems
Okay, so we’ve talked a lot about why key rotation is important, but how do we actually make sure it happens? It’s not enough to just say ‘rotate your keys’; you need systems in place to enforce it. This is where automation and solid processes come into play.
Automating Key Rotation Schedules
Manually tracking when each cryptographic key needs to be rotated is a recipe for disaster. It’s tedious, prone to human error, and frankly, nobody wants to do it. That’s why automating these schedules is so important. Think of it like setting up recurring appointments for your keys. A good Key Management System (KMS) can handle this automatically. You define the rotation period – maybe every 90 days for your SSL certificates or every year for your encryption keys – and the system takes care of the rest. It can even trigger alerts when a rotation is due or has been completed. This takes the guesswork out of the equation and makes sure keys don’t get stale. It’s a big step towards better secrets management.
Monitoring and Auditing Key Usage
Just rotating keys isn’t the whole story. You also need to know how they’re being used and who is using them. This is where monitoring and auditing come in. You want to be able to see when a key is accessed, by what system or user, and if that access is legitimate. This helps catch potential misuse or compromised keys early. For instance, if a key that’s supposed to be dormant suddenly starts getting heavy use, that’s a red flag. Auditing also helps with compliance, providing a trail of activity that regulators might ask for. It’s about having visibility into your entire key lifecycle, from creation to destruction.
Integrating Key Rotation into Security Workflows
Finally, key rotation shouldn’t be a standalone task. It needs to be woven into your broader security operations. This means integrating your key management system with other tools you use, like your Security Information and Event Management (SIEM) system or your incident response platform. When a key is rotated, that event should be logged and potentially trigger other actions. For example, if a key is compromised and needs immediate rotation, that event could automatically kick off an incident response playbook. This makes key rotation part of a larger, coordinated security effort, rather than just another item on a checklist. It’s about making sure your security tools talk to each other effectively, especially when dealing with things like token issuance.
Automating key rotation and integrating it into security workflows reduces the risk of using outdated or compromised keys, which are common entry points for attackers. This proactive approach is far more effective than reacting to a breach after it has already occurred.
Wrapping Up Key Rotation
So, we’ve talked a lot about why rotating your keys is a good idea. It’s not just some technical chore; it’s a real part of keeping your stuff safe. Think of it like changing the locks on your house every so often. You might not have had a break-in, but it’s still smart to do. Making this a regular thing, maybe even automating parts of it, means you’re not leaving doors open for attackers. It’s about staying ahead, even when the bad guys are always trying new tricks. Keep at it, and your systems will be that much tougher.
Frequently Asked Questions
What is key rotation and why is it important?
Key rotation means changing your secret codes, like passwords or encryption keys, regularly. It’s important because if someone steals an old code, they can’t use it forever to get into your stuff. It’s like changing the locks on your house every year to keep burglars out.
How often should I rotate my keys?
The best time to rotate keys depends on how sensitive your information is and how often it’s used. For very important stuff, you might change keys every 30, 60, or 90 days. For less sensitive things, maybe every year is okay. The main idea is to do it often enough to stay safe.
What happens if I don’t rotate my keys?
If you don’t change your keys, and someone manages to get a hold of one, they can keep using it to access your systems or data for a long time. This makes it easier for hackers to steal information or cause damage, and it makes it harder to figure out when a breach actually happened.
Can key rotation be automated?
Yes, absolutely! Many systems can automatically rotate keys for you. This is much better than trying to remember to do it yourself. Automation helps make sure it happens on time and correctly, which is a big help for keeping things secure.
What is a Key Management System (KMS)?
A Key Management System, or KMS, is like a special safe for your secret codes. It helps you create them, keep them safe, change them when needed (rotate them), and get rid of them when they’re no longer used. It makes managing all your keys much easier and more secure.
How does key rotation help against ransomware?
Ransomware locks up your files and demands money. If ransomware steals your encryption keys, rotating those keys makes the stolen key useless for future encryption. It also helps ensure that your backups, which might use encryption, are protected by current keys, making recovery easier.
What’s the difference between key rotation and key revocation?
Key rotation is like changing your locks to new ones. Key revocation is like taking away someone’s key entirely because they shouldn’t have access anymore. Rotation is about keeping things fresh and secure over time, while revocation is about immediately stopping access.
Does key rotation apply to passwords too?
Yes, the idea of rotating secrets applies to passwords as well! While we often talk about ‘keys’ in encryption, changing your passwords regularly is a form of key rotation. It helps protect your accounts from being taken over if a password gets exposed.
