You know, sometimes the scariest attacks aren’t the ones that blast through your front door. Instead, they’re more like a sneaky trap, set up where you least expect it. That’s pretty much the idea behind a watering hole attack strategy. Instead of going after you directly, attackers find a place you already trust, like a website you visit often, and plant their trap there. It’s a bit like leaving poisoned bait near a deer’s favorite water source. They’re counting on you to just go about your business, visit your usual spots, and then BAM! You’ve walked right into their plan. It’s a pretty clever, if devious, way to get people to compromise their own security.
Key Takeaways
- A watering hole attack strategy involves compromising websites frequented by a target group, rather than attacking targets directly.
- Attackers scout for websites with high traffic from specific demographics and exploit vulnerabilities to inject malicious code.
- Malicious code can lead to drive-by downloads, credential harvesting, or session hijacking, aiming to infect visitors or steal information.
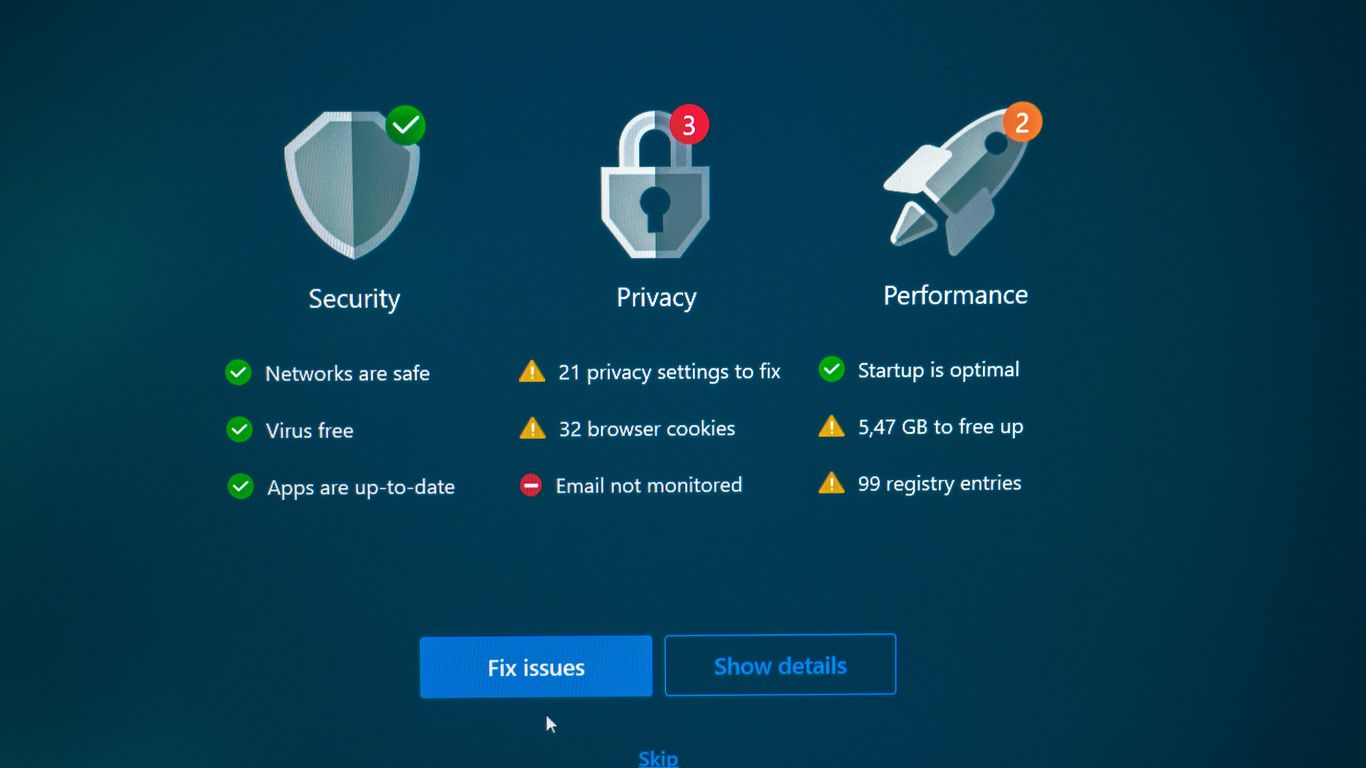
- Defending against these attacks requires a layered approach including web filtering, endpoint security, and user awareness training.
- Staying informed about evolving tactics, like AI-driven attacks and supply chain integration, is vital for effective defense.
Understanding Watering Hole Attacks
Watering hole attacks are a bit like setting a trap. Instead of going directly after a specific person or company, attackers figure out where their targets like to hang out online. Think of it like knowing which park bench your intended victim always sits on and then hiding a treat there. In the digital world, this means finding websites that a particular group of people visits regularly.
Defining The Watering Hole Attack Strategy
This strategy is all about patience and observation. Attackers identify websites that a specific group of users frequently visits. These could be industry news sites, forums, or even social media groups. Once they know where their targets go, they compromise one of these trusted sites. The goal isn’t to attack the website itself, but to use it as a stepping stone. They infect the site with malicious code, waiting for the target audience to visit. When a user from the targeted group browses the compromised site, their device can get infected without them even realizing it. It’s a way to bypass direct defenses by exploiting the trust users place in familiar online locations.
Targeting Specific User Groups
What makes watering hole attacks so effective is their focused approach. Attackers aren’t just randomly infecting websites; they’re doing it with a specific audience in mind. They might be after employees of a particular company, members of a professional organization, or even attendees of a specific conference. By understanding the interests and online habits of these groups, attackers can choose the most relevant websites to compromise. This precision means they’re more likely to hit their intended mark because the compromised site is one their targets are already likely to visit.
Exploiting Trusted Websites
The core of a watering hole attack relies on trust. Attackers don’t usually create their own fake websites for this purpose. Instead, they find legitimate, well-trafficked sites that their targets already trust. This could be a popular news portal, a professional association’s website, or a forum dedicated to a specific hobby. By compromising these established sites, attackers gain an advantage. Users are less likely to be suspicious of a site they visit regularly and consider safe. This trust is what allows the malicious code to be delivered without raising immediate alarms.
Here’s a look at common types of websites targeted:
- Industry-specific news sites
- Professional or trade association portals
- Online forums and communities
- Blogs frequented by the target demographic
- Event or conference websites
Reconnaissance And Target Selection
Before launching a watering hole attack, attackers spend a good amount of time figuring out who to target and where they hang out online. It’s like casing a joint, but for the digital world. They’re not just randomly picking websites; they’re doing their homework to find the best spots where their intended victims are likely to visit.
Identifying High-Traffic Websites
The first step is finding websites that a specific group of people actually uses. Think about it: if you want to catch fish, you go where the fish are, right? Attackers do the same. They look for sites that are popular with the people they want to hit. This could be anything from industry-specific forums and news sites to social media groups or even the official website of a professional organization. The goal is to find a place with consistent traffic from the target audience. They might use tools to see which sites are popular in general, but then they narrow it down to see which ones are frequented by, say, software developers in a particular region or employees of a specific company. It’s all about finding that sweet spot where the target audience congregates online.
Analyzing Visitor Demographics
Once they have a list of potential websites, attackers dig deeper. They want to know who is visiting these sites. Are they the right kind of people? This involves looking at visitor demographics. For example, if the target is a company’s executives, they’ll look for sites that executives are known to visit, perhaps financial news sites or specific business publications. They might analyze publicly available data, social media profiles, or even use specialized tools to get a picture of the audience. Understanding the visitor profile is key to making sure the chosen watering hole will actually reach the intended victims. It’s not enough for a site to be popular; it has to be popular with the right people. This analysis helps them avoid wasting resources on sites that won’t yield the desired results. It’s a bit like threat hunting, trying to find patterns and predict behavior.
Assessing Website Security Posture
Finally, attackers check how secure the website is. They’re looking for weaknesses they can exploit. This means checking for outdated software, known vulnerabilities in web applications, or weak security configurations. A site that’s well-maintained and up-to-date is harder to compromise. Attackers prefer sites that are easier targets, perhaps those that haven’t been updated in a while or have known security holes. They might scan the site for specific vulnerabilities or look for signs of neglect. The easier it is to get a foothold, the more likely they are to proceed with that particular watering hole. This part of the reconnaissance is about finding the path of least resistance to infect the site and, by extension, its visitors. It’s a critical step in the overall attack lifecycle.
Compromising The Watering Hole
Once attackers have identified a suitable watering hole, the next step is to actually compromise it. This isn’t usually about brute-forcing a login; it’s more about finding a way to inject malicious code or redirect users to a malicious site.
Exploiting Web Application Vulnerabilities
Many websites, especially older ones or those with custom code, have security holes. Attackers look for these weaknesses, like SQL injection or cross-site scripting (XSS) flaws. They might use automated tools to scan for known vulnerabilities or manually probe the site. Successfully exploiting a web application vulnerability can give them the ability to modify the site’s content or even run their own code on the server. This is a common way to get malicious scripts onto a page that visitors will see. It’s a bit like finding a loose window in a house to get inside.
Leveraging Drive-By Downloads
This is where things get really sneaky. A drive-by download happens when a user visits a compromised website, and malicious software is downloaded to their computer without them even knowing it. Attackers achieve this by embedding code on the watering hole site that exploits vulnerabilities in the visitor’s web browser or its plugins (like Flash or Java, though these are less common now). When the browser tries to load the page, it unknowingly downloads and runs the malware. It’s a silent infection, and it’s a big reason why keeping your browser and plugins updated is so important. This method is a core part of many man-in-the-browser attacks.
Injecting Malicious Scripts
This is a broad category, but it’s central to compromising the watering hole. Attackers might inject JavaScript code directly into the website’s HTML. This script could do a number of things: redirect users to a fake login page to harvest credentials, download further malware, or even try to exploit browser vulnerabilities. Sometimes, they might compromise the website’s content management system (CMS) or gain access through a compromised third-party plugin. The goal is to make the legitimate website serve malicious content to its unsuspecting visitors. This can be a very effective way to distribute malware, especially if the website is trusted by the target audience. Attackers often look for ways to make these scripts blend in, making them harder to spot.
Payload Delivery Mechanisms
Once attackers have successfully compromised a watering hole website, the next critical step is to get their malicious payload onto the visitors’ systems. This isn’t usually a direct download; it’s often more subtle, aiming to blend in or exploit existing trust. The goal is to make the user’s device the entry point for further malicious activity.
Malware Distribution
This is perhaps the most straightforward method. Attackers embed malicious code within seemingly harmless files or exploit vulnerabilities to push malware directly. A common technique here is the drive-by download. When a user visits the compromised site, their browser or a plugin might have a vulnerability that attackers can exploit. Without any user interaction beyond just visiting the page, malware can be downloaded and installed in the background. This is why keeping browsers and plugins updated is so important.
Credential Harvesting Pages
Instead of directly installing malware, attackers might redirect users to fake login pages. These pages look identical to legitimate ones – think of a bank’s login screen or a popular social media site. The user, trusting the compromised watering hole website, enters their username and password, thinking they’re logging into a legitimate service. This stolen information is then sent directly to the attacker. These credentials can be used for identity theft, financial fraud, or to gain access to other accounts, especially if the user reuses passwords.
Session Hijacking Techniques
Another method involves stealing session cookies or tokens. When you log into a website, it often gives your browser a temporary ‘session’ identifier. If an attacker can get hold of this identifier, they can impersonate you on that website without needing your password. They essentially ‘hijack’ your active session. This can be done by injecting scripts into the compromised website that capture these session details when a user visits. It’s a stealthy way to gain access to accounts and sensitive information.
Exploitation And Post-Exploitation
Once a watering hole attack has successfully compromised a website and infected visiting users, the next phase is all about making the most of that access. This is where the attackers move from setting the trap to actually catching their prey and reaping the rewards.
Executing Malicious Code
The primary goal here is to get the malicious code, often delivered via a drive-by download or a script injection, to run on the victim’s machine. This code might be a downloader for more sophisticated malware, or it could be designed to immediately start gathering information. The success of this step hinges on exploiting vulnerabilities in the user’s browser, plugins, or operating system that haven’t been patched. Attackers often use exploit kits that contain a variety of exploits, trying them in sequence until one works. The code itself is usually obfuscated to avoid detection by basic security software.
Lateral Movement Within Networks
If the initial compromise was on a user’s machine within a corporate network, the attacker won’t stop there. They’ll try to move from that initial foothold to other systems on the network. This is called lateral movement. They might use stolen credentials from the compromised machine, exploit network service vulnerabilities, or use techniques like pass-the-hash to gain access to other accounts and servers. The aim is to find more valuable targets, like domain controllers or servers holding sensitive data.
Data Exfiltration Strategies
After gaining access and potentially moving around the network, the attacker’s final objective is often to steal data. This could be sensitive customer information, intellectual property, financial records, or credentials. Attackers use various methods for exfiltration, trying to make the data transfer look like normal network traffic to avoid detection. This might involve:
- Using encrypted channels: Tunneling stolen data through protocols like HTTPS or DNS.
- Staging data: Collecting data in a temporary location on the network before exfiltrating it in larger chunks.
- Slow and low: Transferring data gradually over extended periods to stay under the radar of monitoring tools.
- Covert channels: Hiding data within seemingly innocuous network protocols or file transfers.
The sophistication of post-exploitation activities can vary greatly. Some attackers might be content with simply deploying ransomware and demanding payment, while others engage in long-term espionage, carefully extracting information over weeks or months without triggering alarms. The key is to remain undetected for as long as possible to maximize the value of the compromise.
Defense Against Watering Hole Attacks
So, how do you actually stop these watering hole attacks from messing with your systems? It’s not just one thing, you know. It’s more like building a bunch of different walls, so if one gets breached, there are others behind it. Think of it as a layered approach.
Web Filtering and Content Security
First off, you really need to pay attention to what your users are accessing online. Web filtering tools can be a lifesaver here. They can block access to known malicious sites or even sites that have suspicious characteristics. It’s like having a bouncer at the door of the internet for your company. Content security goes a bit further, looking at the actual data flowing through. This can help catch malicious code that might be hidden in legitimate-looking web pages. It’s about being proactive and not just waiting for something bad to happen.
Endpoint Protection and Patch Management
Your computers and devices, the endpoints, are often the final target. Good endpoint protection software, like advanced antivirus or endpoint detection and response (EDR) systems, can spot and stop malware before it does any real damage. But even the best software can’t always catch brand new threats. That’s where patch management comes in. Keeping all your software, especially web browsers and plugins, up-to-date with the latest security patches is super important. Attackers love to exploit old, known vulnerabilities, so closing those doors is key. Regularly updating your systems is one of the most effective ways to prevent many types of attacks.
Monitoring Outbound Connections
Sometimes, the first sign that something’s wrong isn’t an alert on your firewall, but rather unusual activity going out from your network. Monitoring outbound connections can help detect if a compromised machine is trying to communicate with a command-and-control server or exfiltrate data. It’s like watching for someone trying to sneak out of a building with stolen goods. Setting up alerts for suspicious traffic patterns can give you an early warning that a watering hole attack might be in progress or has already succeeded.
It’s easy to focus only on stopping bad stuff from getting in. But attackers often need to send data out or check in with their servers. Watching that outgoing traffic can reveal a lot about what’s happening on your network, even if the initial entry point was a seemingly harmless website visit.
User Awareness And Training

When we talk about watering hole attacks, it’s easy to get caught up in the technical details of how websites get compromised or what kind of malware is used. But honestly, a big part of the defense comes down to us, the users. Our actions, or inactions, can either be the weakest link or a strong line of defense.
Recognizing Suspicious Websites
Think about how often you click on links without really looking. Watering hole attacks count on that. They infect sites you already trust, making them look normal. So, what’s the trick to spotting trouble?
- Look for the unexpected: Did that familiar news site suddenly start asking for your login details in a weird way? Is a shopping site you frequent showing ads that seem off? Trust your gut.
- Check the URL: Even a small typo can mean you’re not on the real site. Attackers are good at making URLs look similar. Take an extra second to check.
- Browser warnings: Don’t just click past those warnings your browser throws up about a site being unsafe. They’re there for a reason.
Safe Browsing Habits
This is where we build good habits. It’s not about being paranoid, but about being smart online. It’s like looking both ways before crossing the street, but for the internet. A good starting point is understanding how to spot phishing attempts, which often go hand-in-hand with these kinds of attacks. Regular training can make a big difference here.
Here’s a quick rundown of what safe browsing looks like:
- Think before you click: Seriously, pause. Is that email attachment from someone you know? Is that link in a social media post too good to be true?
- Keep software updated: Those update notifications aren’t just annoying. They often patch up security holes that attackers love to exploit. This includes your browser, operating system, and any plugins.
- Use strong, unique passwords: If one site gets compromised, you don’t want that same password to open the door to all your other accounts. A password manager can help a lot with this.
- Be wary of public Wi-Fi: It’s convenient, but often not secure. Avoid doing sensitive things like online banking on open networks.
Reporting Potential Threats
If you see something suspicious, don’t just ignore it or assume someone else will report it. Reporting is how we help the whole community stay safer. It’s a team effort.
- Know who to tell: Does your company have a security team or IT help desk? Make sure you know how to reach them quickly.
- Provide details: When you report something, give as much information as you can. What did you see? What were you doing? What made it seem suspicious?
- Don’t be afraid to speak up: It’s better to report a false alarm than to let a real threat go unnoticed. No one will fault you for being cautious.
Advanced Watering Hole Tactics
Watering hole attacks aren’t static; attackers are constantly refining their methods to stay ahead. They’re moving beyond simply compromising a popular website and hoping for the best. Now, we’re seeing more sophisticated approaches that make these attacks harder to spot and more effective.
AI-Driven Attack Vectors
Artificial intelligence is changing the game. Attackers are using AI to automate the tedious parts of finding vulnerabilities and crafting convincing lures. This means they can scan for weaknesses across many sites much faster and create personalized messages that are much harder for people to ignore. This automation allows for quicker adaptation to defenses and a broader reach. Think of it like having a super-smart assistant that’s always looking for the easiest way in. This also ties into AI-driven social engineering, where AI can generate fake content to trick people.
Supply Chain Integration
Instead of directly attacking a company, attackers are now targeting the companies that other companies rely on. This is the supply chain approach. If an attacker can compromise a software update service or a popular third-party tool that many businesses use, they can potentially infect hundreds or thousands of organizations all at once. It’s a way to get a lot of bang for their buck, hitting multiple targets through a single point of compromise. This is a key aspect of supply chain attacks.
Mobile Device Targeting
We’re not just talking about computers anymore. Attackers are increasingly focusing on mobile devices. This can involve creating fake apps that look legitimate or exploiting vulnerabilities in mobile browsers. Since many people use their phones for work and personal tasks, compromising a mobile device can give attackers access to a wealth of sensitive information. This includes things like banking details, personal communications, and even access to corporate networks if the device is used for work.
Incident Response For Watering Hole Incidents
When a watering hole attack is suspected or confirmed, a structured incident response is key. It’s not just about cleaning up the mess; it’s about understanding how it happened and stopping it from happening again. This means having a plan ready before anything goes wrong.
Identifying Compromised Websites
The first step is figuring out which websites are actually compromised. This can be tricky because attackers try to hide their tracks. We look for unusual network traffic, strange redirects, or alerts from security tools. Sometimes, it’s as simple as noticing a website that used to load fine now behaving oddly or showing security warnings. We also rely on external threat intelligence feeds that might flag a site as malicious. It’s a bit like being a detective, piecing together clues to find the source of the problem.
Containing The Spread Of Malware
Once we know a site is compromised, we need to stop it from infecting more people. This usually involves taking the site offline temporarily or blocking access to it. For internal systems, if we suspect malware has spread, we isolate the affected machines. This means disconnecting them from the network to prevent further movement. Think of it like quarantining a sick patient to stop a contagious disease from spreading through a hospital. We also work with the website owner, if possible, to get the malicious code removed quickly. This might involve removing malicious scripts or patching the vulnerability that allowed the compromise in the first place.
Remediation And Recovery Processes
After containing the threat, we move to remediation. This is where we clean up the infected systems and restore them to a safe state. For websites, this means ensuring all malicious code is gone and the site is secure. For internal networks, it involves removing malware, patching systems, and resetting any compromised credentials. Recovery is the final stage, bringing systems back online and making sure everything is working as it should. We also conduct a post-incident review to learn from the event. What went wrong? How could we have detected it sooner? This helps us update our defenses and response plans for the future. It’s a cycle of response, recovery, and improvement.
The Evolving Threat Landscape
Attackers rarely use just one method anymore. Instead, they combine social tricks, technical flaws, and trusted relationships to break into organizations. Today, the speed at which attacks change can leave defenses behind almost instantly. Here are a few trends that stand out:
- Ransomware groups blend data theft and threats of publicity to push victims into paying up.
- Social engineering blends with automation, making phishing campaigns harder to spot.
- Multi-stage attacks now chain together weak links in identity, endpoints, and cloud infrastructure.
| Attack Vector | Notable Recent Trend |
|---|---|
| Phishing | Personalization using breached data |
| Ransomware | Double/triple extortion |
| Supply Chain | Widespread impact via popular software |
| Web Application Exploits | API attacks, insecure dependencies |
Security teams cannot rely on set-it-and-forget-it defenses; attackers innovate faster than patch cycles.
The Role Of Zero-Day Vulnerabilities
Zero-day attacks run rampant in the current threat environment. These are flaws in software or hardware that vendors don’t yet know about, giving attackers a head start. Rather than targeting big companies, attackers often use zero-days in watering hole attacks aimed at smaller, niche organizations.
Three things to know about zero-days:
- They’re often sold in underground markets before the public ever hears about them.
- Detection requires watching for odd behavior, since there are no signatures to catch.
- Fast patching and isolation can help limit the fallout when a zero-day is found in use.
When attackers combine zero-days with social engineering, it becomes much harder for typical protection tools to intervene.
Cross-Platform Attack Vectors
Watering hole attacks aren’t just a web issue anymore. As more people rely on mobile apps, cloud services, and connected devices, attackers go where the users are. Cross-platform threats now hit:
- Mobile phones, especially through malicious apps or fake updates
- IoT devices, which often lack strong update controls
- Cloud accounts, using compromised credentials for widespread access
Some attackers can use a single point of compromise to infect several types of devices or systems at once.
| Platform | Common Attack Methods |
|---|---|
| Windows Desktops | Malicious scripts, drive-by downloads |
| Mobile (Android/iOS) | Fake apps, SMS phishing |
| IoT Devices | Default credentials, unpatched firmware |
| Cloud Services | OAuth abuse, stolen tokens |
Organizations have to think bigger: a single vulnerability may be used to jump from a website to a mobile device to a cloud account all in one attack campaign. Staying current with defensive tactics isn’t optional anymore—it’s required just to keep up.
Staying Ahead of the Game
So, we’ve talked a lot about watering hole attacks. They’re pretty sneaky, right? Attackers don’t just barge in; they wait for you to visit a place you already trust, like a website you check every day. It’s like someone setting a trap in your favorite coffee shop. The key takeaway here is that staying safe isn’t just about having good antivirus software, though that’s important. It’s also about being smart online, keeping your systems updated, and just generally being aware of what’s going on. Think of it like locking your doors even when you’re home – it’s just a good habit to have. Because these attacks keep changing, we all need to keep learning and adapting, too. It’s a constant effort, but definitely worth it to keep your digital stuff safe.
Frequently Asked Questions
What exactly is a watering hole attack?
A watering hole attack is like a trap set by cybercriminals. They figure out which websites a specific group of people often visits, like a favorite hangout spot. Then, they secretly infect one of those trusted websites with harmful code. When people from that group visit the infected site, their computers or devices can get infected too, without them even realizing it.
How do attackers choose which websites to target?
Attackers do some homework. They try to find websites that are popular with the specific people or organizations they want to attack. This could be industry news sites, forums, or even social media pages that their targets frequently check. The goal is to find a place where their victims are likely to show up.
What happens when a user visits an infected website?
If a user visits a compromised website, harmful software, often called malware, can be downloaded onto their device automatically. This is sometimes called a ‘drive-by download.’ It can happen just by visiting the page, without the user clicking on anything suspicious. This malware can then steal information or cause other problems.
What kind of harm can malware from a watering hole attack cause?
The malware can do many bad things. It might steal personal information like passwords or credit card numbers, spy on what you’re doing, lock up your files and demand money (ransomware), or give the attacker control over your device to use it for other bad activities.
How can someone protect themselves from watering hole attacks?
Staying safe involves a few key things. Keep your software and web browser updated, as updates often fix security holes. Use good antivirus software and be careful about what you click on. Companies can use security tools to block suspicious websites and monitor network activity.
Is it possible to tell if a website has been compromised?
It’s often very difficult. Attackers try hard to make the infected websites look normal. Sometimes, a website might suddenly start acting strangely, like loading very slowly or showing weird pop-ups, but often there are no obvious signs until it’s too late. That’s why being cautious is important.
Are watering hole attacks common?
Yes, these attacks are used quite often, especially against specific groups like businesses, government agencies, or people in certain industries. They are a popular tactic because they can be very effective at reaching a targeted audience through a trusted source.
What’s the difference between a watering hole attack and a regular phishing attack?
A regular phishing attack usually involves sending fake emails or messages directly to people, trying to trick them into clicking a bad link or giving up info. A watering hole attack is different because it infects a website people *already* choose to visit, making it a more indirect but often more successful way to infect a target group.
