It’s easy to think that security breaches only happen because of some super-clever hacker. But honestly, a lot of the time, sensitive information just sort of… slips out. This isn’t usually because someone’s trying to be sneaky; it’s more about things being left open, mistakes being made, or systems just not being up to snuff. This article looks at all the ways information leakage can happen, often without anyone meaning for it to, and what we can do about it.
Key Takeaways
- Many information leaks happen due to simple mistakes in how systems are set up or managed, like using default passwords or not updating software. This is often called ‘unintentional information leakage’.
- Web applications, operating systems, and networks all have common weak spots that can accidentally expose data if not properly secured.
- Cloud environments and APIs, while powerful, introduce new ways information can leak if configurations are wrong or security isn’t kept up.
- Human error and insider actions, even when not malicious, are significant causes of information leakage, highlighting the need for training and good access controls.
- Keeping track of all your systems, from old ones to new cloud services, and managing risks from third-party suppliers is key to preventing accidental data exposure.
Understanding Information Leakage Vectors

Information leakage can happen in so many ways, it’s almost dizzying. It’s not always a direct hack; sometimes it’s just a slip-up. Think of it like leaving a window open – you didn’t invite anyone in, but the opportunity is there. These pathways, or vectors, are how sensitive data can get out when it shouldn’t. Understanding these vectors is the first step to actually stopping them.
Web Application Vulnerabilities and Information Leakage
Web apps are often the front door to a lot of data. Because they’re usually accessible from the internet, they’re prime targets. Things like SQL injection, where an attacker tricks the database into revealing information, or cross-site scripting (XSS), which can steal user session data, are common culprits. Even simple things like not properly validating user input can lead to unexpected data exposure. It’s a constant battle to keep these applications secure, especially with new features being added all the time.
Operating System Vulnerabilities Leading to Information Leakage
Your operating system is the foundation for everything. If the OS itself has weaknesses, it’s like building on shaky ground. Flaws in the OS kernel or system services can allow attackers to gain higher privileges, essentially giving them the keys to the kingdom. Outdated systems are a big problem here; if a known vulnerability isn’t patched, it’s an open invitation. This is why keeping systems updated is so important, even if it sometimes feels like a hassle.
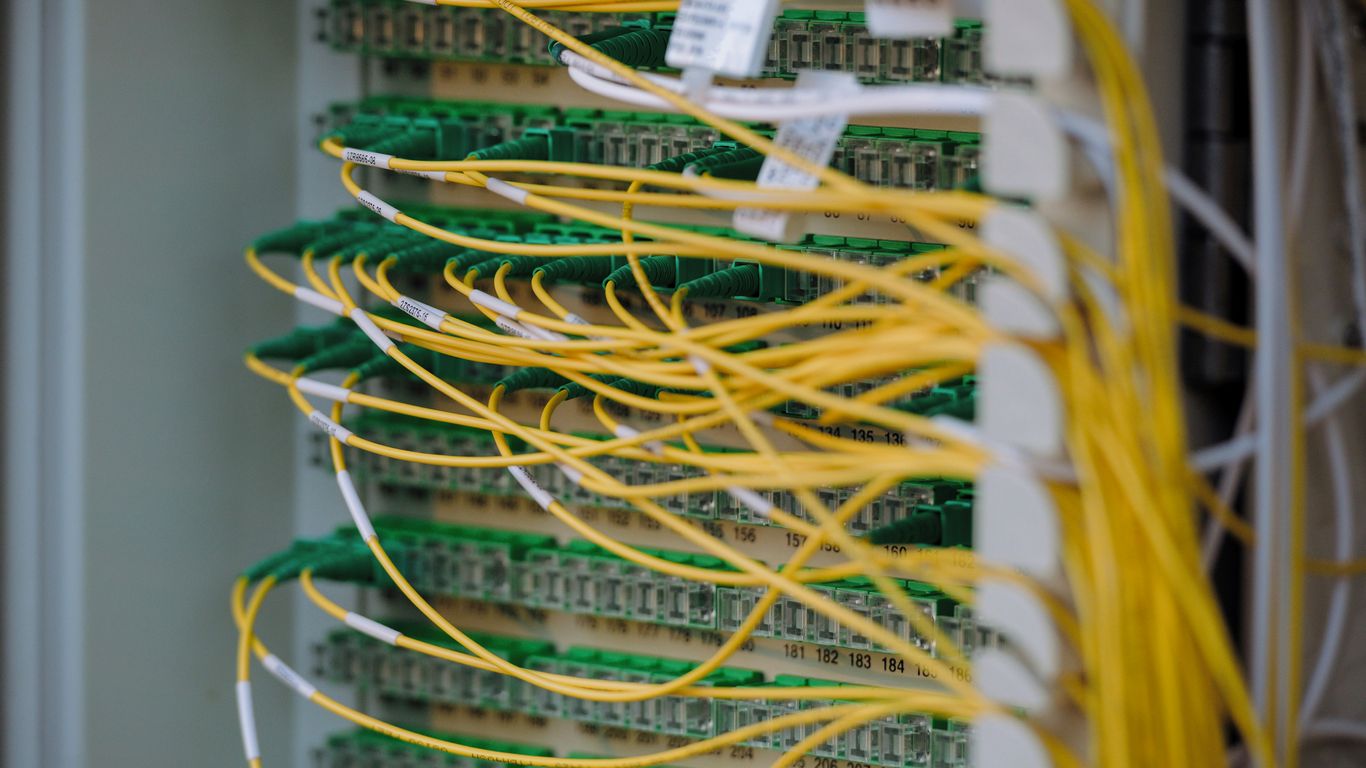
Network Vulnerabilities Exposing Sensitive Data
Networks are the highways for data. If those highways have weak security, data can be intercepted or accessed. Think about open ports that shouldn’t be, or using old, unencrypted protocols like Telnet. A poorly configured firewall can also let in more traffic than it should. If an attacker can get onto the network, even with limited access, they might be able to move around and find sensitive information. A flat network, where everything is connected without much segmentation, makes this lateral movement much easier. It’s all about controlling who can talk to what and how they do it. Understanding attack vectors is key to securing these pathways.
Configuration and Cloud-Related Information Leakage
Misconfigurations are a surprisingly common way sensitive information ends up in the wrong hands. It’s not always about sophisticated hacks; sometimes, it’s just a simple setting that’s been overlooked. This section looks at how mistakes in configuration and the way we use cloud services can open the door to data leaks.
Misconfigurations as a Source of Information Leakage
Think of a misconfiguration like leaving a door unlocked. It’s not an intentional breach, but it makes it incredibly easy for someone to walk in. This happens a lot with storage systems, databases, and even basic access controls. When default settings aren’t changed, or permissions are set too broadly, data that should be private can become accessible to anyone who knows where to look, or worse, to automated scanning tools.
- Default Credentials: Many systems come with default usernames and passwords. If these aren’t changed immediately, they become a prime target.
- Excessive Permissions: Giving users or applications more access than they actually need is a classic mistake. This can lead to accidental data exposure or malicious misuse.
- Disabled Logging: If logging is turned off or not configured correctly, you lose the ability to see who accessed what, making it impossible to detect or investigate a leak.
The sheer volume of data managed today means that even a small misconfiguration can have a large impact. Automated tools can scan for these errors, but manual oversight is still vital.
Cloud Environment Vulnerabilities and Data Exposure
Cloud environments offer incredible flexibility, but they also introduce new challenges. The shared responsibility model means that while the cloud provider secures the infrastructure, you are responsible for securing your data and applications within it. This is where many leaks happen.
- Exposed Storage Buckets: Cloud storage services like S3 buckets are notorious for being accidentally left public, exposing vast amounts of data.
- Identity and Access Management (IAM) Issues: Overly permissive IAM roles or poorly managed credentials can grant unauthorized access to cloud resources.
- Insecure APIs: Cloud services rely heavily on APIs. If these aren’t properly secured, they can become a gateway for attackers to access or manipulate data.
| Cloud Service | Common Misconfiguration | Potential Leakage |
|---|---|---|
| Object Storage | Publicly accessible buckets | Sensitive documents, PII, financial data |
| Databases | Default credentials, broad network access | Customer records, intellectual property |
| Serverless Functions | Insecure environment variables | API keys, database credentials |
Insecure APIs and Information Leakage Risks
APIs (Application Programming Interfaces) are the glue that holds modern applications together, especially in the cloud. They allow different software components to communicate. However, if an API isn’t designed or secured properly, it can become a significant source of information leakage.
- Lack of Authentication/Authorization: If an API doesn’t properly verify who is making a request and what they are allowed to do, sensitive data can be accessed by anyone.
- Excessive Data Exposure: APIs might return more data than the requesting application actually needs, potentially exposing sensitive fields.
- Rate Limiting Issues: Without proper limits on how many requests can be made, attackers can use APIs to systematically probe for vulnerabilities or extract large amounts of data.
It’s easy to focus on the big, complex attacks, but often, the simplest oversights in configuration or cloud setup are the ones that lead to unintentional information leaks. Paying attention to these details is key to keeping data safe.
Identity, Endpoint, and Mobile Information Leakage
When we talk about information leakage, it’s easy to get caught up in network firewalls and server configurations. But a huge chunk of the problem often lies much closer to home: with the identities we use, the devices we carry, and the endpoints we work from. These areas are frequently overlooked, yet they represent prime real estate for attackers looking to get in.
Identity and Access Vulnerabilities Causing Information Leakage
Think about how we log into things. Weak passwords, reusing the same password across multiple sites, or not using multi-factor authentication (MFA) are like leaving your front door wide open. Identity systems are prime targets because if an attacker gets hold of legitimate credentials, they can often move around without raising immediate alarms. It’s not just about passwords, though. Stale accounts – those belonging to former employees or contractors that were never properly disabled – are another common oversight. These lingering digital ghosts can be exploited long after the person has left the company.
- Excessive privileges: Giving users more access than they actually need for their job is a classic mistake.
- Insecure authentication flows: How systems verify who you are can have weak spots.
- Stale accounts: Old accounts that are still active but no longer needed.
Endpoint Vulnerabilities and Data Exposure
Your laptop, your desktop, even that server humming away in the corner – these are all endpoints. If they’re not properly secured, they become easy entry points. This usually means unpatched software, which is like having a known hole in your wall that anyone can crawl through. Insecure local settings, turning off security features like antivirus, or just not keeping devices updated all contribute to a larger attack surface. Attackers often aim for endpoints first because they’re the initial gateway into a network.
Mobile Device Vulnerabilities and Information Leakage
Smartphones and tablets are practically extensions of ourselves these days, and they often carry sensitive company data. The problem is, they operate outside the usual network defenses. Malicious apps that ask for way too many permissions, outdated operating systems that haven’t been patched, or storing data without encryption are all significant risks. If you lose your phone or it gets compromised, that sensitive data can easily fall into the wrong hands. Even connecting to unsecured public Wi-Fi can be a risky move, potentially exposing data in transit.
| Vulnerability Type | Common Issues |
|---|---|
| Mobile Apps | Excessive permissions, insecure data storage |
| Operating Systems | Outdated versions, unpatched vulnerabilities |
| Network Connections | Insecure Wi-Fi, lack of VPN usage |
| Data Storage | Unencrypted local storage, cloud sync issues |
Emerging and Specialized Information Leakage Threats
Beyond the usual suspects, a new wave of threats is constantly appearing, often targeting specific technologies or environments. These aren’t your everyday web app flaws; they require a different kind of attention.
IoT Vulnerabilities and Information Leakage
The Internet of Things (IoT) has exploded, connecting everything from smart thermostats to industrial sensors. The problem? Many of these devices were built with convenience, not security, in mind. They often lack basic security features like strong passwords, regular updates, or even encryption. This makes them easy targets for attackers looking to steal data or use them as entry points into a network.
- Default credentials: Many IoT devices ship with easily guessable or publicly known default usernames and passwords.
- Lack of patching: Manufacturers often don’t provide updates, leaving known vulnerabilities unaddressed.
- Insecure communication: Data transmitted between devices or to the cloud might not be encrypted, allowing eavesdropping.
Operational Technology and ICS Information Leakage
Operational Technology (OT) and Industrial Control Systems (ICS) manage critical infrastructure like power grids, water treatment plants, and manufacturing facilities. Historically, these systems were isolated, but increased connectivity for efficiency has opened them up to new risks. A breach here isn’t just about data theft; it can lead to physical disruption, environmental damage, or even loss of life. Information leakage from these systems could reveal operational details, control logic, or sensitive process parameters.
Hardware Vulnerabilities and Data Exposure
Sometimes, the threat isn’t in the software but in the hardware itself. Flaws in processors, memory chips, or other physical components can lead to data leakage that’s incredibly hard to detect and even harder to fix with software patches alone. Think of things like Rowhammer attacks, which can flip bits in memory, or side-channel attacks that analyze power consumption or electromagnetic emissions to infer sensitive data. These are highly specialized but can bypass many traditional security measures.
| Vulnerability Type | Potential Leakage |
|---|---|
| CPU-level flaws | Sensitive data from other processes or the OS |
| Memory bus exploits | Data in transit between components |
| Side-channel analysis | Encryption keys, passwords, or other secrets |
| Firmware weaknesses | System configuration, access credentials, network info |
These specialized threats highlight that security isn’t just about code. The physical components of our systems, and the very way they operate at a low level, can also be sources of unintended information disclosure. Addressing these requires a deeper dive into hardware security and advanced analysis techniques.
Supply Chain and Third-Party Information Leakage
When we talk about information leakage, it’s easy to focus only on what’s happening inside our own digital walls. But a huge chunk of risk comes from outside, specifically through our supply chain and the third-party vendors we rely on. Think about it: every software update, every service provider, every outsourced process is a potential entry point for attackers. They don’t always go for the strongest defenses directly; sometimes, they find a weaker link in the chain and use that to get to you. It’s like a domino effect, but with data.
Third-Party and Supply Chain Vulnerabilities
This is where things get tricky. Organizations often inherit risks from their suppliers. This can happen through software libraries that have hidden flaws, integrations with other services that aren’t properly secured, or even shared infrastructure. The problem is, we don’t always have a clear view into how secure our partners are. This lack of visibility means we might not know about a vulnerability until it’s already being exploited. It’s a big reason why supply chain attacks are becoming so common. Attackers are getting really good at finding these trusted channels to distribute malware or gain unauthorized access. It’s not just about software, either; compromised hardware components can also make their way into your systems.
Managing Third-Party Risk for Information Leakage Prevention
So, what can we do about it? First off, we need to be more diligent about vetting our partners. This means looking beyond just the price tag and really digging into their security practices. Are they following industry standards? Do they have a plan for handling security incidents? It’s also about having clear contracts that outline security responsibilities. Continuous monitoring is key here. We can’t just check once and forget about it. We need to keep an eye on our vendors’ security posture throughout the relationship. This is a core part of managing third-party risk. Building a robust vendor risk management program involves several steps:
- Initial Assessment: Thoroughly evaluate potential vendors’ security controls before signing any contracts.
- Contractual Agreements: Include specific security requirements, data protection clauses, and incident notification obligations.
- Continuous Monitoring: Regularly assess vendor compliance and security posture through audits, questionnaires, and threat intelligence.
- Incident Response Planning: Coordinate with vendors on how to respond to security incidents that may affect both parties.
Vendor Security and Information Leakage Concerns
Ultimately, the security of your data is only as strong as the weakest link in your entire ecosystem. If a vendor suffers a breach, your data could be exposed, even if your own internal security is top-notch. This is why it’s so important to treat vendor security not just as a compliance checkbox, but as a genuine business risk. We need to understand that our attack surface extends far beyond our own network perimeter. It includes all the services and software we use from external providers. Being proactive about understanding and mitigating these risks is essential for preventing unintentional information leakage.
Human Factors in Information Leakage
When we talk about security, it’s easy to get caught up in the tech – firewalls, encryption, all that jazz. But honestly, a lot of the time, the weakest link isn’t a piece of code or a network device. It’s us. People. Our actions, or sometimes our inactions, can open doors for attackers in ways that complex malware can only dream of. This section looks at how human behavior, whether intentional or not, plays a big role in information getting out when it shouldn’t.
Insider Threats and Unintentional Information Leakage
Insiders, meaning people within the organization like employees or contractors, can cause data leaks. This isn’t always malicious. Sometimes, it’s just a mistake. Someone might accidentally email sensitive documents to the wrong person, or leave a company laptop unlocked in a public place. These aren’t acts of sabotage, but they still result in confidential information being exposed. Think about a busy employee trying to meet a deadline; they might cut corners on security procedures without even realizing the risk they’re creating. It’s about the pressure and the daily grind sometimes leading to errors.
- Accidental Data Exposure: Sending sensitive files to the wrong recipient.
- Lost or Stolen Devices: Unsecured laptops or phones containing company data.
- Improper Data Disposal: Not securely deleting files or shredding documents.
- Overly Broad Access: Employees having access to more data than they need for their job.
Human Factors Influencing Information Leakage
Beyond direct insider actions, a whole host of human elements can contribute to security weaknesses. Think about how tired people get, especially when they’re overworked. When you’re exhausted, your attention wanders, and you’re more likely to make a mistake. It’s not that you want to leak information, but your brain just isn’t firing on all cylinders. This cognitive load can make security protocols seem like a hassle, leading people to bypass them. Also, the general culture within a company matters a lot. If security isn’t seen as everyone’s responsibility, it’s easy for bad habits to creep in.
Security awareness training is often seen as a checkbox exercise, but its real value lies in making people think twice before clicking a suspicious link or sharing a password. It’s about building a habit of caution.
Social Engineering and Information Leakage
This is where attackers actively try to trick people into revealing information or performing actions that compromise security. They play on our natural tendencies – our desire to be helpful, our respect for authority, or our fear of missing out. A common tactic is phishing, where an attacker pretends to be someone trustworthy, like IT support or a senior executive, and asks for credentials or sensitive data. It’s incredibly effective because it targets our psychology, not just technical flaws. Even the most secure systems can be bypassed if someone is convinced to hand over the keys.
Here’s a quick look at how social engineering works:
- Reconnaissance: The attacker gathers information about the target organization and individuals.
- Building Trust/Urgency: The attacker crafts a message or scenario designed to elicit a specific response.
- Exploitation: The target falls for the trick, providing information or access.
- Information Leakage: The sensitive data is compromised or systems are accessed.
Technical Vulnerabilities Enabling Information Leakage
When we talk about how sensitive information gets out when it shouldn’t, a lot of it comes down to technical weak spots. These aren’t usually the result of someone being careless, but rather flaws in the systems themselves. Think of them as tiny cracks in a dam that, over time, can let a lot of water through.
Zero-Day Vulnerabilities and Information Leakage
Zero-day vulnerabilities are the scariest kind because, by definition, nobody knows about them except the attackers. This means there are no patches, no defenses, and no warnings. When a zero-day is exploited, it’s like a secret door being opened that security systems aren’t even looking for. Attackers can use these unknown flaws to get into systems, steal data, or cause damage before anyone even realizes what’s happening. It’s a race against time, and usually, the defenders are behind from the start. Because these are so valuable, they’re often used in targeted attacks against high-value organizations or individuals.
SQL Injection Attacks and Data Exposure
SQL injection is a classic web application vulnerability. It happens when an attacker can trick a website’s database into doing things it shouldn’t. Basically, they insert malicious SQL code into input fields, like a search bar or a login form. If the website isn’t built carefully, that code gets run by the database. This can let attackers see all sorts of data they shouldn’t, like user lists, passwords, or even credit card numbers. It’s a pretty common way for sensitive information to leak out of web applications, and it’s been around for ages, yet it still catches many sites off guard. Proper input validation is key to preventing this, but it’s often overlooked.
Malware and Malicious Software Leading to Information Leakage
Malware is a broad category, but it’s a huge reason for unintentional information leakage. Think about viruses, trojans, spyware, and ransomware. These malicious programs are designed to infect systems and then do bad things. Spyware, for example, is specifically made to watch what you do and send that information back to the attacker. Ransomware might encrypt your data, but often it also steals it first. Even seemingly harmless adware can sometimes collect more data than it should. Malware can get onto systems in many ways, from clicking a bad link to downloading a compromised file. Once it’s in, it can quietly exfiltrate data without the user ever knowing. It’s a constant battle to keep these threats at bay, and new variants pop up all the time. Keeping your software updated and being careful about what you download are good first steps, but it’s a complex problem.
Here’s a quick look at how different types of malware can lead to data leaks:
| Malware Type | Primary Information Leakage Method |
|---|---|
| Spyware | Keylogging, screen capture, data harvesting |
| Trojan | Backdoor access, data exfiltration |
| Ransomware | Data theft before encryption |
| Infostealer | Steals credentials, financial data |
The technical vulnerabilities that allow information to leak are often subtle. They might be a single line of flawed code, a default setting that was never changed, or a system that’s just too old to keep up with modern security. Understanding these technical weak points is the first step in building stronger defenses and keeping sensitive data where it belongs.
Systemic Weaknesses Contributing to Information Leakage
Sometimes, the biggest security holes aren’t flashy zero-days or clever social engineering. They’re the slow, steady weaknesses that build up over time, often due to neglect or just the sheer complexity of managing modern IT environments. These systemic issues can create a broad attack surface, making it easier for attackers to find a way in and cause trouble.
Patch Management Gaps and Information Leakage
Think about software updates. We all get those notifications, right? Sometimes we click ‘remind me later’ a few too many times. In a business setting, this can be a major problem. When patches for known vulnerabilities aren’t applied promptly, those weaknesses remain open doors. Attackers actively scan for systems running outdated software, and if they find one, they can often use readily available tools to exploit the flaw. This isn’t about discovering a brand-new exploit; it’s about taking advantage of something everyone else already knows about but hasn’t fixed.
- Delayed patching leaves known vulnerabilities exploitable.
- Challenges include compatibility issues and the downtime required for updates.
- Decentralized ownership can lead to inconsistent application of security fixes.
Legacy System Vulnerabilities and Data Exposure
Many organizations still rely on older systems. These might be critical for specific operations, but they often lack support for modern security features. Vendors might stop releasing security updates, leaving them permanently vulnerable. Trying to secure these systems can be like trying to fit a square peg in a round hole. They might not support strong encryption, multi-factor authentication, or even basic logging that newer systems take for granted. This makes them prime targets for attackers looking for an easy way into the network. Securing these systems often requires creative workarounds or significant investment in modernization.
Legacy systems accumulate vulnerabilities over time and are difficult to secure or replace, presenting a persistent risk.
Encryption Weaknesses and Information Leakage Risks
Encryption is supposed to be a safeguard, but it’s not foolproof. Weaknesses can creep in through several avenues. This could be using outdated or weak encryption algorithms that are easily broken. It could also be poor key management – losing the keys, using default keys, or not rotating them regularly. Expired certificates can also cause issues, sometimes leading systems to fall back to less secure communication methods or simply breaking functionality. When encryption fails, sensitive data, whether it’s stored on a disk or moving across the network, becomes exposed.
| Weakness Type | Example |
|---|---|
| Algorithm | Using DES instead of AES |
| Key Management | Reusing default keys, no key rotation |
| Implementation | Incorrectly applying encryption protocols |
| Certificate Issues | Expired or untrusted SSL/TLS certificates |
Detection and Mitigation of Information Leakage
Spotting when sensitive information might be slipping out is one thing, but actually stopping it is another. It’s like trying to catch water with a sieve – you need the right tools and a good plan. We’re talking about putting up defenses and having a way to clean up the mess if something does get out.
Logging and Monitoring Gaps in Information Leakage Detection
Think of logs as the security camera footage of your systems. If the cameras aren’t on, or they’re only recording in a few spots, you’re going to miss a lot. Many organizations struggle because their logging isn’t set up right. They might log too much generic stuff, making it hard to find the important bits, or they don’t log critical events at all. This leaves blind spots where attackers can operate without anyone noticing.
- Inadequate Event Logging: Not capturing enough detail about user actions, system changes, or network traffic.
- Poor Log Management: Logs are stored improperly, overwritten too quickly, or not centralized, making analysis difficult.
- Lack of Alerting: Even if logs exist, there are no systems in place to flag suspicious activity in real-time.
Without proper visibility, detecting subtle information leakage becomes nearly impossible. It’s like trying to find a needle in a haystack when the haystack is also on fire and you can’t see.
Security Monitoring and Detection of Information Leakage
This is where you actively look for trouble. It’s not just about having logs; it’s about using them and other tools to find suspicious patterns. This involves a mix of automated systems and sometimes, good old-fashioned human analysis. We need to watch for things like unusual data transfers, access to sensitive files by people who shouldn’t be looking, or strange network activity.
Here are some common areas to focus on:
- Data Loss Prevention (DLP) Tools: These systems are designed to identify and block sensitive data from leaving the network. They can monitor emails, file transfers, and cloud storage.
- User and Entity Behavior Analytics (UEBA): UEBA tools look for deviations from normal user behavior. If an employee suddenly starts downloading large amounts of customer data late at night, that’s a red flag.
- Network Traffic Analysis (NTA): Monitoring network flows can reveal unusual communication patterns, like large outbound transfers to unknown destinations.
- Endpoint Detection and Response (EDR): EDR solutions monitor activity on individual computers and servers, looking for signs of compromise or data exfiltration.
Incident Response and Recovery from Information Leakage
Okay, so something did leak. Now what? This is where your incident response plan kicks in. It’s not just about fixing the technical problem; it’s about managing the fallout. This means figuring out what was lost, who was affected, and how to prevent it from happening again. It also involves communicating with customers or regulators if necessary.
Key steps usually include:
- Containment: Stop the leak from spreading further. This might mean isolating affected systems or revoking access.
- Eradication: Remove the cause of the leak, whether it’s malware, a misconfiguration, or a compromised account.
- Recovery: Restore systems to normal operation and ensure data integrity.
- Post-Incident Analysis: Understand exactly how the leak happened, what lessons were learned, and update security measures accordingly.
| Phase | Key Activities |
|---|---|
| Preparation | Develop Incident Response Plan, train teams, establish communication channels. |
| Identification | Detect and confirm an incident is occurring. |
| Containment | Limit the scope and impact of the incident. |
| Eradication | Remove the root cause of the incident. |
| Recovery | Restore affected systems and data to normal operation. |
| Post-Incident Activity | Conduct lessons learned, update plans, and improve defenses. |
Strategic Approaches to Prevent Information Leakage
Preventing unintentional information leakage isn’t just about having the right tools; it’s about building a security-conscious culture and implementing smart, layered defenses. It requires a proactive stance, looking at your entire digital footprint and how information flows in and out of your organization. Think of it like securing your home – you need strong locks, but you also need to make sure everyone in the house knows not to leave the door open.
Attack Surface Management and Information Leakage Reduction
Your attack surface is basically all the points where an attacker could try to get into your systems. This includes network connections, applications, user accounts, and even devices your employees use. The bigger this surface, the more chances there are for something to go wrong. Reducing it means getting rid of unnecessary access points and making sure the ones you keep are well-protected. It’s about being deliberate with what you expose.
- Identify all potential entry points: This means mapping out your networks, applications, cloud services, and any third-party connections.
- Minimize exposure: Turn off unused services, close unnecessary ports, and restrict access to only what’s needed.
- Regularly review and audit: Things change, so you need to keep checking your attack surface to make sure it hasn’t grown or become less secure.
Security Frameworks and Information Leakage Prevention
Using established security frameworks provides a structured way to think about and manage your security risks. Frameworks like NIST or ISO 27001 offer guidance on what controls to put in place and how to organize your security efforts. They help ensure you’re not just reacting to problems but building a robust, ongoing security program. It’s about having a plan that covers all the bases.
Frameworks help align security activities with overall business goals, making sure that security investments are purposeful and contribute to the organization’s resilience rather than just being a technical checklist.
Identity, Authentication, and Authorization for Information Leakage Control
How you manage who and what can access your systems is incredibly important. Identity management is about knowing who is who, authentication is proving they are who they say they are, and authorization is deciding what they are allowed to do. Weaknesses here, like reused passwords or overly broad permissions, are a common way sensitive data gets out. Strong identity controls are a cornerstone of preventing unauthorized access and subsequent leakage.
- Implement Multi-Factor Authentication (MFA): This adds an extra layer of security beyond just a password.
- Enforce the Principle of Least Privilege: Users and systems should only have the minimum access necessary to perform their tasks.
- Conduct Regular Access Reviews: Periodically check who has access to what and remove any unnecessary permissions. This is especially important for sensitive data, and tools exist to help manage data security.
By focusing on these strategic areas, organizations can significantly reduce the risk of unintentional information leakage, moving from a reactive posture to a more proactive and resilient security stance.
Wrapping Up: Staying Vigilant in a Connected World
So, we’ve talked a lot about how information can slip out, often without anyone meaning for it to. It happens everywhere, from the apps we use daily to the big systems companies run. Whether it’s a simple mistake like leaving a door unlocked or a more complex issue with how software is built, the result is the same: sensitive stuff can get out. The key takeaway here is that staying safe isn’t just about having the latest tech. It’s about being aware, checking things twice, and making sure everyone, from the top boss to the newest hire, understands the risks. It’s an ongoing effort, not a one-and-done fix, and requires constant attention to keep our digital lives secure.
Frequently Asked Questions
What is unintentional information leakage?
It’s when sensitive information accidentally gets out, like leaving a door unlocked. This can happen because of mistakes in how computers are set up, weak passwords, or even just human error, leading to data falling into the wrong hands without anyone meaning for it to.
How can web applications leak information?
Web apps can leak info through flaws like ‘injection attacks’ where bad code is slipped in, or ‘cross-site scripting’ where sneaky scripts run. If these apps aren’t built carefully, they might show more data than they should or let attackers get in.
What’s the danger with cloud settings leaking data?
In the cloud, mistakes in setting up who can access what are super common. Think of leaving a storage box wide open for anyone to see. Bad configurations or not understanding how cloud security works can easily expose important company or customer data.
Can my phone or computer be a source of leaks?
Yes! If your phone or computer isn’t updated, has weak security, or runs old software, it’s like having a weak lock on your house. Hackers can get in through these ‘endpoint vulnerabilities’ and steal the information stored on your device.
What are ‘zero-day’ vulnerabilities?
A ‘zero-day’ is a brand new security hole that nobody knows about yet, not even the company that made the software. Because it’s unknown, there’s no fix, making it a prime target for hackers to exploit before it can be patched.
How do insider threats cause information leaks?
Insiders are people who already have access, like employees. They might accidentally share too much, use their access wrongly, or even intentionally steal data. Because they have permission, their actions can be harder to spot than an outsider’s.
What’s the problem with old computer systems?
Old systems, or ‘legacy systems,’ often don’t get security updates anymore. They might have known weaknesses that haven’t been fixed, making them easy targets for attackers. It’s like using an old, rusty key that anyone could copy.
How can we stop information from leaking?
Stopping leaks involves many things: keeping software updated, setting up strong passwords and access rules, training people about security risks, and constantly checking for weak spots. It’s about building many layers of defense and being careful with information.
