You know, sometimes employees bring their own tools to work. It’s not always a bad thing, but it can create some headaches for IT. This stuff, often called shadow IT, can pop up anywhere. It’s like finding a new app on your work computer that nobody in IT approved. It might seem harmless, but these unmanaged systems can really mess with security. We’re going to look at why this happens and what we can do about it.
Key Takeaways
- Shadow IT happens when people use apps or systems without IT knowing. This creates blind spots in security.
- Unauthorized systems can easily bypass security checks, leading to weaknesses that attackers might find.
- To fix this, we need better tools to see what’s being used, clear rules about what’s okay, and good alternatives for people to use.
- When IT doesn’t know about certain systems, it’s harder to spot attacks and protect company data.
- Making sure everyone follows security rules, from IT to regular users, is a big part of keeping things safe from shadow IT.
Understanding Shadow IT Risks
Shadow IT, basically when employees use tech tools or services without the IT department’s knowledge or approval, is a pretty common thing these days. It happens because people want to get their jobs done faster or easier, and sometimes the official tools just don’t cut it. But this convenience comes with a heap of risks that can really mess with an organization’s security.
The Pervasive Nature of Shadow IT
It’s easy for shadow IT to creep in. Think about all the cloud-based apps and services available. A team might start using a new project management tool or a file-sharing service because it seems more efficient for their specific tasks. Before you know it, multiple departments are using different, unapproved tools, creating a fragmented and hard-to-manage technology landscape. This widespread use means that security policies and controls that are in place for approved systems simply don’t apply to these rogue applications. It’s like having doors unlocked all over the building without anyone realizing it.
Unmanaged Systems and Applications
When systems and applications aren’t managed by IT, they often miss out on critical security updates and patches. This leaves them open to known vulnerabilities that attackers are actively looking for. Imagine using an old version of software that has a well-documented security flaw; attackers can find guides on how to exploit it. These unmanaged assets also might not have proper access controls, meaning sensitive data could be exposed to more people than intended. It’s a recipe for trouble, especially when you consider how many cloud computing security challenges stem from unpatched systems.
Blind Spots in Security Oversight
Perhaps the biggest issue with shadow IT is the blind spot it creates for the security team. If you don’t know a system exists, you can’t protect it. This lack of visibility means that security monitoring tools won’t be tracking activity on these unauthorized systems. Potential threats or breaches might go completely unnoticed until they cause significant damage. It’s hard to defend your perimeter when you don’t even know where all the walls are. This makes it incredibly difficult to maintain a strong security posture and respond effectively to incidents.
Identifying Unauthorized Systems
Spotting systems and applications that aren’t officially sanctioned can feel like a treasure hunt, but one where the treasure is actually a security risk. These unauthorized systems pop up because users or departments find them useful for their work, often without realizing the potential problems they create. They bypass the usual checks and balances, leaving security teams in the dark.
Bypassing Security Controls
When software or hardware is brought into the network without going through the proper IT channels, it automatically sidesteps all the security measures that are supposed to be in place. Think of it like building a new room onto your house without telling the building inspector – you might get away with it for a while, but it probably won’t meet safety codes. These systems might not have the right firewalls, they could be missing critical security updates, or they might not be configured to log activity properly. This means that even if your main systems are locked down tight, these rogue elements can become easy entry points for attackers.
Lack of Proper Asset Discovery
It’s tough to protect what you don’t know exists. Many organizations struggle with keeping an accurate inventory of all the hardware and software running on their network. This is where shadow IT really thrives. If a system isn’t on the official asset list, it won’t be included in regular security checks, vulnerability scans, or patching schedules. This creates a significant blind spot. Without knowing what’s out there, you can’t possibly secure it.
Vulnerabilities from Unmanaged Assets
Unmanaged assets are essentially ticking time bombs. Because they aren’t overseen by IT, they often run outdated software with known security flaws. These vulnerabilities can be exploited by attackers looking for an easy way in. Imagine a company that relies heavily on its main server security but has a forgotten, unpatched workstation connected to the network. An attacker could compromise that workstation and then use it as a stepping stone to access more sensitive parts of the network. It’s a classic case of the weakest link breaking the chain.
The challenge isn’t just about finding these systems; it’s about understanding the risks they introduce and then bringing them under control or removing them entirely. Ignoring them is not an option if you want to maintain a solid security posture.
Mitigating Shadow IT Challenges
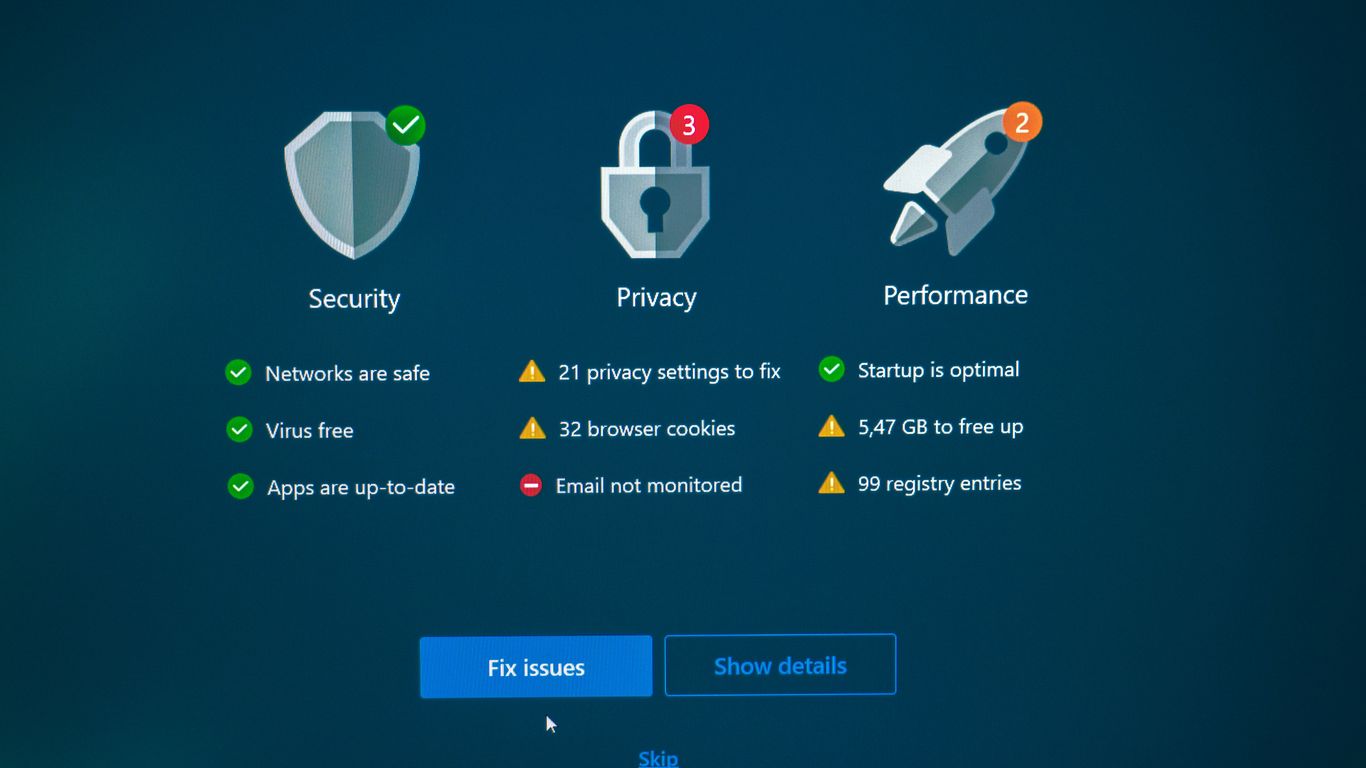
Shadow IT, those unsanctioned systems and applications employees use without official approval, can really mess with your security. It’s like having a bunch of unlocked doors in your house that you didn’t even know existed. The biggest hurdle is just knowing what’s out there. Without that visibility, you can’t protect it. So, how do we get a handle on this? It really comes down to a few key areas.
Enhancing Visibility Tools
First off, you need to see what you’re dealing with. This means investing in tools that can scan your network and cloud environments to find all the software and services being used. Think of it as a digital inventory. You’re looking for anything that isn’t on your approved list. This isn’t a one-time thing, either; it needs to be an ongoing process. Keeping an accurate list of all assets is a big part of effective patch management, as you can’t patch what you don’t know you have.
Establishing Clear Organizational Policies
Once you know what’s out there, you need rules. Clear policies are super important. These should outline what kind of software and services are allowed, what the process is for requesting new tools, and what the consequences are for using unapproved ones. It’s not just about saying ‘no’; it’s about explaining why certain tools are risky and what the potential impact could be. This helps employees understand the security implications and make better choices.
Providing Secure and Approved Alternatives
Sometimes, employees turn to shadow IT because the official tools are clunky, slow, or just don’t do what they need. If you can offer good, secure alternatives that meet their needs, they’re much less likely to go rogue. This might mean evaluating and approving popular third-party apps or developing internal solutions. Making it easy for people to do their jobs securely is a win-win. It reduces risk and keeps productivity up. It’s about making the secure path the easiest path.
The Impact of Shadow IT on Security Posture
When systems and applications pop up without the IT department’s knowledge, it really messes with how secure the whole organization is. Think of it like adding extra doors to your house without telling anyone – you don’t know who has keys or if they’re even locked properly. This creates a much bigger attack surface, giving bad actors more places to try and get in.
Increased Attack Surface Exposure
Shadow IT means there are systems, cloud services, or apps running that the security team doesn’t know about. Because they’re unknown, they don’t get the usual security checks, updates, or monitoring. This leaves them wide open for exploitation. It’s not just about more entry points; it’s about entry points that are likely unpatched and misconfigured, making them easy targets. This can include anything from a team using a free online project management tool to a department spinning up its own cloud server without IT approval.
Challenges in Threat Detection
Detecting threats becomes a lot harder when you don’t know what you’re supposed to be protecting. Security tools are usually set up to monitor known systems and traffic patterns. Unauthorized systems operate outside these established parameters. This means malicious activity happening on or through these shadow systems might go completely unnoticed. It’s like trying to spot a burglar when you don’t even know which windows are supposed to be there.
Compromised Data Integrity and Availability
When data is stored or processed on unmanaged systems, its integrity and availability are at risk. There might not be proper backup procedures in place, meaning data could be lost permanently if something goes wrong. Furthermore, without security controls, data could be altered without anyone knowing, or it could be held hostage by ransomware. This directly impacts business operations and can lead to significant financial and reputational damage.
- Data Loss: Lack of backups on unmanaged systems.
- Data Corruption: Unauthorized modifications to sensitive information.
- Service Unavailability: Systems going offline without a recovery plan.
The biggest problem with shadow IT is that it creates blind spots. Security teams can’t protect what they can’t see, and these unauthorized systems are literally invisible to their standard defenses. This makes the entire organization more vulnerable to breaches and data loss.
Addressing Insufficient Security Testing
When systems and applications aren’t checked regularly for weaknesses, it’s like leaving the back door unlocked. This is what we mean by insufficient security testing. It means that vulnerabilities can hang around for ages, completely unnoticed, just waiting for someone to find them. This isn’t just a minor oversight; it’s a direct invitation for trouble.
Persistent Undetected Weaknesses
Think about it: if you don’t look for problems, you won’t find them. This is especially true with software and systems that get updated or changed over time. New code can introduce new flaws, or old configurations might become insecure as the environment around them shifts. Without a dedicated effort to find these issues, they just sit there. This creates a growing list of potential entry points for attackers that the security team might not even know exist. It’s a ticking time bomb, really.
Integrating Secure Development Lifecycles
So, what’s the fix? One big part is making sure security is part of the development process from the very start. This is often called a ‘secure development lifecycle’ or SDLC. Instead of just building something and then trying to test the security later, you build security in. This means things like:
- Threat modeling: Thinking about what could go wrong during the design phase.
- Secure coding practices: Training developers to write code that avoids common mistakes.
- Code reviews: Having other developers or security experts look over the code for potential issues.
- Using security tools: Employing automated checkers that scan code for known vulnerabilities.
This approach helps catch problems early, when they are much cheaper and easier to fix. It’s a proactive way to build more robust systems.
The Role of Regular Vulnerability Scans
Beyond building securely, you’ve got to keep checking. Regular vulnerability scans are like routine check-ups for your systems. These scans use automated tools to look for known weaknesses, like outdated software versions or misconfigurations. They can cover a lot of ground quickly and identify a wide range of potential problems. It’s important to remember that these scans aren’t a silver bullet; they find known issues. But they are a really important piece of the puzzle for keeping unauthorized systems from becoming major headaches.
The absence of regular, thorough security testing creates a false sense of security. It allows vulnerabilities to fester, increasing the likelihood and impact of a successful cyberattack. Proactive identification and remediation are key to maintaining a strong security posture.
Combating Improper Access Controls
When systems and data aren’t protected by the right access rules, it’s like leaving the front door unlocked. This is where improper access controls come into play, and honestly, it’s a pretty big deal for security. It means people might be able to see or do things they really shouldn’t, which can lead to all sorts of problems, from accidental data leaks to deliberate misuse.
Overly Broad Permission Risks
Think about giving everyone the keys to the entire building, just in case they might need to access one specific room someday. That’s essentially what happens with overly broad permissions. Users get access to way more data and functions than their actual job requires. This isn’t just inefficient; it’s a security nightmare waiting to happen. If an account with too many permissions gets compromised, an attacker can instantly access a huge amount of sensitive information or critical systems. It makes it much harder to track who did what, too, because so many people have the same wide-ranging access.
Implementing Role-Based Access
So, how do we fix this? A really solid approach is Role-Based Access Control, or RBAC. Instead of assigning permissions individually, you group users into roles based on their job functions. Then, you assign permissions to those roles. For example, everyone in the ‘Sales’ role might get access to customer relationship management tools, but only the ‘Sales Manager’ role gets permission to export customer lists. This way, people only have the access they need to do their jobs, and nothing more. It simplifies management and significantly cuts down on the risk of unauthorized access.
The Necessity of Regular Access Reviews
Even with RBAC in place, things can get messy over time. People change roles, leave the company, or their job duties evolve. If access isn’t updated accordingly, you end up with ‘permission creep,’ where people retain access they no longer need. That’s why regular access reviews are so important. You need to periodically check who has access to what and confirm that it still aligns with their current responsibilities. This usually involves managers or system owners verifying their team members’ access rights. It’s a bit of a chore, but it’s a vital step in keeping your access controls tight and effective.
Keeping access controls in check isn’t just about setting them up once; it’s an ongoing process. Regular checks and updates are key to preventing unauthorized access and misuse, especially as your organization and its people change.
Securing Unmanaged Endpoints
When we talk about Shadow IT, we often focus on the software and cloud services people bring in without permission. But we can’t forget about the devices themselves. Unmanaged endpoints, like personal laptops, tablets, or even IoT gadgets that connect to the company network, are a big deal. They’re often the first place attackers try to get in because they might not have the same security protections as company-issued gear. Think about it: if a personal laptop isn’t patched regularly or has outdated antivirus, it’s an open door.
Common Entry Points for Attackers
These devices can be a weak link in a few ways. For starters, they might not have the latest security updates installed. Attackers love systems that are easy to exploit because they’re running old software. Also, if these devices connect to public Wi-Fi networks, they could be vulnerable to snooping or man-in-the-middle attacks. And let’s not forget about removable media, like USB drives, which can carry malware from one place to another. It’s a real concern when you consider how many people work remotely now.
Essential Endpoint Protection Measures
So, what can we do? First, we need to have some form of endpoint protection on these devices, even if they’re not company-owned. This could involve installing security software that monitors for malicious activity. We also need to think about how these devices connect to our network. Implementing network segmentation can help limit the damage if an unmanaged endpoint does get compromised. It’s like putting up firewalls between different parts of your house so a small fire in one room doesn’t burn down the whole place. Having a clear policy on what’s allowed is also key.
The Importance of Device Management and Patching
Ultimately, the goal is to reduce the attack surface. This means making sure all devices, managed or not, are as secure as possible. Regular patching is one of the most effective ways to close known security holes. It’s a bit like fixing a leaky roof before the next rainstorm. We need to know what devices are connecting to our network and ensure they meet a minimum security standard. This might involve using tools that can scan devices for vulnerabilities or enforce certain security settings before allowing them access. It’s a continuous effort, not a one-time fix, to keep our digital environment safe. You can find more information on how to manage these risks by looking into endpoint security solutions.
Keeping track of every single device that connects to your network can feel overwhelming, especially with remote work and BYOD policies. However, ignoring these unmanaged endpoints is a risk you can’t afford to take. A proactive approach, combining clear policies with the right technical controls, is the best way to defend against potential threats.
The Human Element in Shadow IT
It’s easy to get caught up in the technical side of cybersecurity, focusing on firewalls and encryption. But honestly, a lot of security issues boil down to people. Think about it: how often do problems start because someone clicked a bad link or used a weak password? That’s where the human element in shadow IT really comes into play. When employees bypass official channels to use tools they find easier or more convenient, they’re often creating blind spots that security teams can’t see. This isn’t usually malicious; it’s just people trying to get their jobs done more efficiently.
User Behavior Analytics for Anomalies
One way to get a handle on this is by looking at user behavior. Tools that track user activity can flag unusual patterns. For example, if someone suddenly starts accessing a lot of files they don’t normally touch, or if they’re logging in at odd hours from strange locations, that’s a signal something might be off. These systems help detect potential insider threats, whether they’re accidental or intentional. It’s like having a digital detective watching for anything out of the ordinary, helping to spot issues before they become major problems. This kind of monitoring can be really helpful in understanding what’s actually happening on your network, beyond just the approved applications.
Risks Associated with Remote Work
Remote work has definitely changed the game. Suddenly, people are working from home, using their own internet connections and sometimes their own devices. This expands the attack surface significantly. A home network might not have the same security protections as an office network, and personal devices might not be as well-maintained or protected. This creates more opportunities for attackers to get in. It’s a big shift, and it means we have to think differently about how we secure our systems when people aren’t physically in the office. We need to make sure that even when people are working from anywhere, the data remains safe. This is a big challenge for many organizations today, and it requires a new approach to security controls.
Navigating Bring Your Own Device Policies
Speaking of personal devices, the whole ‘Bring Your Own Device’ (BYOD) thing is another area where the human element is key. Allowing employees to use their personal phones or laptops for work can boost productivity and employee satisfaction, but it also introduces risks. These devices might not have the same security software or updates as company-issued equipment. They could be more vulnerable to malware or theft. So, having clear policies is super important. What kind of security measures are required on personal devices used for work? How do we handle data if a device is lost or stolen? These aren’t just technical questions; they’re about setting expectations for employees and making sure everyone understands their role in keeping company data safe, even on their own tech.
Preventing Privilege Misuse and Credential Issues
When we talk about systems getting compromised, it’s often not about some super-advanced hack. More often than not, it boils down to people having too much access or not protecting their login details properly. This section looks at how to stop those kinds of problems before they start.
The Dangers of Excessive Permissions
Giving people more access than they actually need to do their job is a big risk. Think about it: if an account with admin rights gets stolen, the attacker can do a lot more damage than if that account only had access to a few specific files. This is where the idea of least privilege comes in. It means everyone, and every system, should only have the bare minimum permissions required for their tasks. It’s like giving a temporary worker a key to just one office, not the whole building. This limits what an attacker can do if they manage to get hold of those credentials.
- Over-privileged accounts are a prime target for attackers.
- They allow for easier lateral movement across networks.
- They significantly increase the impact of any account compromise.
We need to be really careful about who gets what level of access. It’s not just about initial setup; it’s an ongoing thing.
Establishing Strong Password Hygiene
This one might sound obvious, but you’d be surprised how many places still struggle with it. Weak passwords, reused passwords, or passwords written down on sticky notes are just invitations for trouble. Strong password policies are a start, but they need to be combined with tools and training. Using password managers can really help users create and store complex passwords without having to remember dozens of them. It’s about making it easy for people to do the right thing.
Good password practices are a foundational element of security. They prevent many common types of unauthorized access and reduce the likelihood of account takeover. Without them, even the most sophisticated security systems can be bypassed.
Discouraging Credential Sharing
Sharing login details is a bad habit that kills accountability. If multiple people use the same account, how do you know who did what? This makes it hard to track down issues and assign responsibility. It also means that if one person leaves the company, their shared credentials might still be in use. We need clear policies against sharing, and technical controls that make it difficult or impossible to do so. For example, systems should ideally require individual logins for access. This is especially important for privileged accounts, where the impact of misuse is so much higher. You can find more information on managing these high-level accounts through Privileged Access Management (PAM) solutions.
- Implement multi-factor authentication (MFA) wherever possible.
- Regularly audit who has access to what, and why.
- Educate users on the risks and consequences of sharing credentials.
Strengthening the Security Culture
Building a strong security culture is about more than just having the right tools; it’s about making sure everyone in the organization understands their role in keeping things safe. It’s like a neighborhood watch, but for our digital assets. When people feel like security is everyone’s job, not just the IT department’s, things tend to run a lot smoother and safer. This means encouraging good habits and making sure people know what to do when something seems off.
Fostering Responsible Security Behaviors
This involves making security practices second nature. It’s about creating an environment where employees naturally think about security in their daily tasks. Think about it: if you’re used to locking your car every time you park, you’re less likely to have it broken into. The same applies to digital security. We need to make sure people are aware of the risks and know how to avoid them.
- Regular Security Awareness Training: Keep training fresh and relevant. Instead of just annual check-the-box exercises, use real-world examples and interactive scenarios. This helps people remember what they learn.
- Clear Communication Channels: Make it easy for employees to ask questions about security or report concerns without fear of reprisal. A simple, accessible reporting system is key.
- Lead by Example: When leaders prioritize and visibly participate in security initiatives, it sends a powerful message throughout the company.
A strong security culture means that security considerations are integrated into everyday decision-making, not treated as an afterthought. It’s about building a shared sense of responsibility.
The Critical Role of Leadership Support
Leadership support is absolutely vital. If the people at the top don’t seem to care about security, why should anyone else? When executives champion security initiatives, allocate resources, and hold teams accountable, it signals that security is a genuine priority. This backing helps drive the adoption of new policies and technologies. It’s not just about signing off on a budget; it’s about actively participating and demonstrating commitment. Without this, even the best security plans can falter. For instance, if leadership doesn’t support implementing a least privilege access model, it becomes much harder to enforce across the organization.
Encouraging Security Reporting
We need to make it as easy as possible for employees to report suspicious activity. This could be anything from a weird email that looks like phishing to noticing unusual system behavior. The faster we know about a potential issue, the quicker we can address it and prevent it from becoming a bigger problem. This means having clear, simple reporting procedures and making sure everyone knows them. It also means responding to reports in a way that encourages more reporting in the future, not less. Acknowledging reports and explaining the outcome, even if it was a false alarm, builds trust and reinforces the value of reporting.
Wrapping Up: Staying Ahead of the Curve
So, we’ve talked a lot about how systems and apps can pop up without anyone really knowing, and how that can cause problems. It’s like leaving doors unlocked when you’re not home. Keeping track of everything, making sure things are tested properly, and controlling who sees what are big parts of keeping things safe. And honestly, it’s not just about the tech; it’s about people too. Making sure everyone understands the risks and does their part makes a huge difference. It’s an ongoing thing, not a one-and-done deal. Staying aware and making smart choices helps keep the digital doors locked tight.
Frequently Asked Questions
What exactly is ‘Shadow IT’?
Shadow IT is like when people in a company use apps or devices for work that the IT department doesn’t know about or hasn’t approved. Think of it as secret tech tools that can cause problems because no one is watching them.
Why is using unapproved systems a big deal?
When systems aren’t approved, they might not be safe. They could have weak spots that hackers can use to get into the company’s network or steal important information. It’s like leaving a window open in your house – you don’t know who might come in.
How can a company find these hidden systems?
Companies can use special tools to look for all the devices and software connected to their network. They also need clear rules about what tech people can and can’t use, and they should offer safe, approved options so employees don’t feel the need to go rogue.
What happens if security checks aren’t done often enough?
If systems aren’t checked for problems regularly, small weaknesses can grow into big security holes. Hackers love finding these overlooked issues. Regular checks, like scanning for viruses and testing defenses, are super important.
What’s the problem with giving people too much access?
When someone has access to more information or systems than they need for their job, it’s risky. If their account gets stolen or they make a mistake, a lot more damage can be done. It’s better to give people only the keys they absolutely need.
How can companies protect devices that aren’t managed?
Devices like personal laptops or phones used for work can be easy targets. Companies need ways to manage these devices, make sure they have security software, and keep them updated with the latest fixes to prevent attackers from using them as an entrance.
Does how people act affect company security?
Yes, definitely! People can accidentally click on bad links, share passwords, or use risky devices. Training them to be careful and aware, especially when working from home or using their own devices, is a huge part of staying safe.
What’s the best way to make sure everyone cares about security?
Building a strong security mindset means everyone understands why it’s important and does their part. Leaders need to show they support security, and employees should feel comfortable reporting anything that seems suspicious without fear.
