You know, we talk a lot about cybersecurity, but sometimes the really deep stuff, like the root of trust, gets overlooked. It’s like the foundation of a house; if that’s shaky, the whole thing is in trouble. This article is going to break down what root of trust exploitation really means, why it’s such a big deal, and how attackers try to mess with it. We’ll also look at what happens when it goes wrong and, importantly, how we can all do a better job of protecting it. It’s not just for the tech wizards; understanding this stuff helps everyone stay safer online.
Key Takeaways
- Root of trust exploitation involves attackers targeting the most basic, foundational security elements of a system, often in hardware or firmware.
- Attackers use various methods, from exploiting hardware flaws and weak firmware to stealing cryptographic keys, to compromise the root of trust.
- A successful root of trust exploit can lead to widespread system compromise, data breaches, and a complete loss of trust in the affected systems.
- Defending against root of trust exploitation requires secure hardware and firmware design, strong cryptographic practices, and continuous security testing.
- Maintaining the integrity of the root of trust is an ongoing process that involves secure development, vigilant monitoring, and adapting to new threats.
Understanding Root Of Trust Exploitation
Defining Root Of Trust Exploitation
So, what exactly is root of trust exploitation? Basically, it’s when someone messes with the most fundamental, built-in security foundation of a device or system. Think of it like trying to tamper with the bedrock of a building – if that’s compromised, everything built on top is at risk. This ‘root of trust’ is usually a piece of hardware or firmware that’s designed to be tamper-proof and is responsible for verifying the integrity of everything else that loads or runs. When an attacker figures out how to mess with this core component, they can essentially trick the system into believing that malicious code or unauthorized actions are legitimate. This opens the door to all sorts of nasty things, from stealing sensitive data to taking complete control of a device. It’s a pretty serious problem because this root of trust is supposed to be the ultimate safeguard.
The Criticality of a Secure Root of Trust
Having a solid, uncompromised root of trust is super important for a few reasons. It’s the first thing that boots up, so it sets the stage for all subsequent security checks. If that initial check is faulty, then any security measures that come after it are basically useless. It’s like having a security guard at the front door who’s actually on the payroll of the burglars – they’ll let anyone in. This is especially true for things like secure boot processes, which rely on the root of trust to verify that the operating system hasn’t been tampered with. Without that verification, malware could load before any antivirus software even has a chance to start up. It’s the bedrock of trust for the entire system.
Motivations Behind Root of Trust Exploitation
Why would someone go through the trouble of trying to exploit a root of trust? Well, the payoff can be huge. For cybercriminals, it means they can potentially gain persistent, low-level access to a system, bypass all sorts of security controls, and steal valuable data like financial information or intellectual property. For nation-state actors, it could be about espionage, gaining a foothold in critical infrastructure, or disrupting enemy systems. Sometimes, it’s just about demonstrating a capability or creating a sophisticated piece of malware that’s incredibly hard to detect. The motivations really boil down to gaining deep, often undetectable, control and access.
Attack Vectors for Root of Trust Exploitation
So, how do attackers actually get at this ‘root of trust’ we’ve been talking about? It’s not like there’s a big, obvious door labeled ‘Exploit Here.’ Instead, they use a variety of clever methods to get in. Think of it like trying to break into a secure building; you might try picking the lock, finding an open window, or even tricking someone into letting you in. The same kind of thinking applies here.
Exploiting Hardware Vulnerabilities
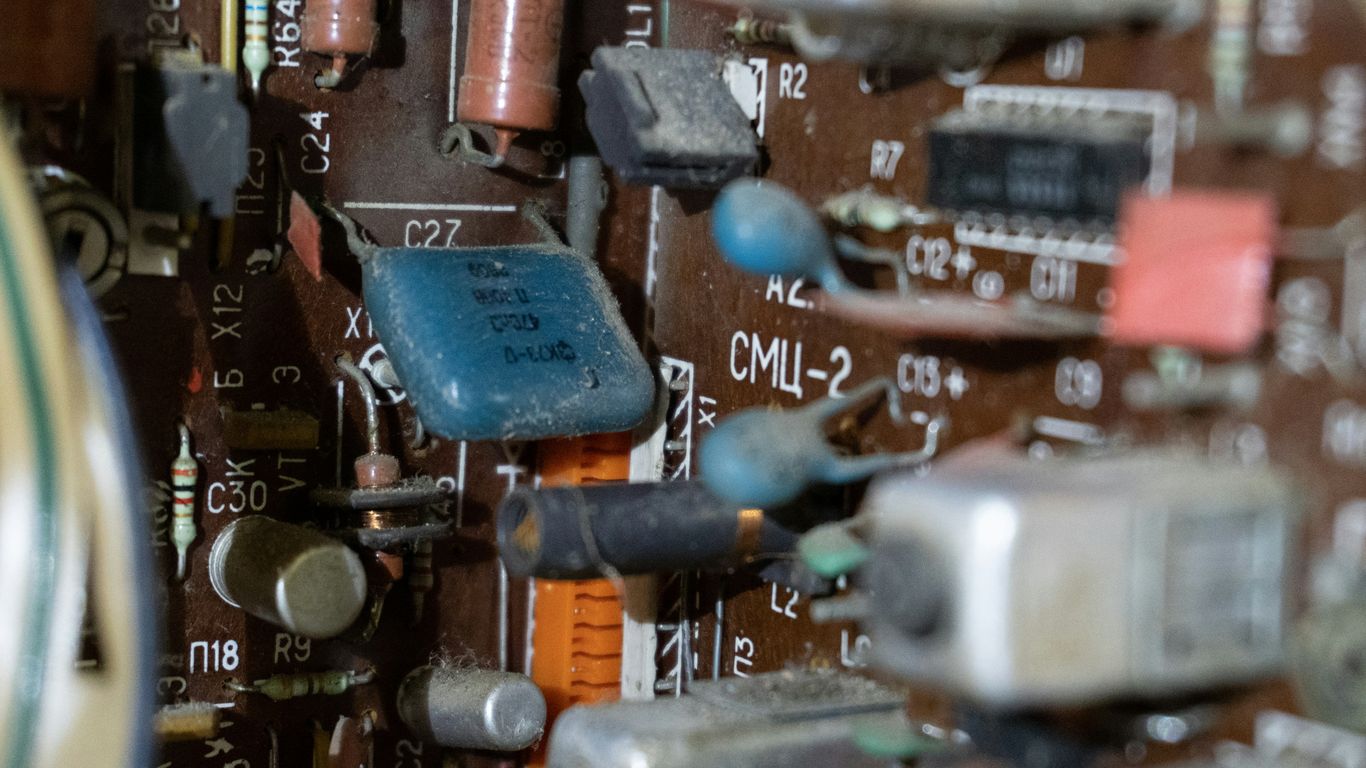
Sometimes, the problem isn’t with the software or the keys, but with the physical chips themselves. Manufacturers try their best, but tiny flaws can creep into the design of processors, memory controllers, or other hardware components. Attackers look for these hardware-level weaknesses. These aren’t always easy to find, and they often require specialized knowledge and equipment to exploit. Imagine a tiny manufacturing defect that, under very specific conditions, could be used to read out secret information or even change how the chip behaves. It’s pretty wild stuff.
Leveraging Firmware Weaknesses
Firmware is like the low-level software that tells hardware how to operate. It’s often stored in chips that are harder to update than your regular operating system. If there’s a bug or a backdoor in this firmware, it can be a goldmine for attackers. They might try to overwrite the legitimate firmware with their own malicious version, or they might find a way to trick the system into running their code through a firmware vulnerability. This is especially tricky because firmware often runs before the main operating system even boots up, giving it a lot of control.
Compromising Cryptographic Keys
Cryptographic keys are the secret ingredients that make encryption work. If an attacker can get their hands on these keys, they can essentially ‘unlock’ all the protected data. This is a big deal. Keys can be stored in various places, from secure hardware modules to software files. Attackers might try to steal them through software exploits, social engineering, or even by physically accessing the device and using specialized tools to extract them. Losing control of cryptographic keys means losing control of the confidentiality and integrity of your data.
Here’s a quick look at some common ways these vectors are used:
- Hardware Flaws: Exploiting timing differences in chip operations, or finding ways to induce errors that reveal secrets.
- Firmware Tampering: Injecting malicious code during the manufacturing process or exploiting update mechanisms.
- Key Extraction: Using side-channel attacks to infer keys from power consumption or electromagnetic emissions, or brute-forcing weak key generation.
The root of trust is designed to be the most secure part of a system. However, attackers are constantly looking for ways around these protections. They understand that if they can compromise this foundational element, the security of the entire system collapses.
Techniques Used in Root of Trust Exploitation
Exploiting a root of trust isn’t usually a smash-and-grab job. Attackers often have to get pretty creative, using a mix of clever tricks to get past the defenses. It’s not just about finding a single flaw; it’s about understanding how the system works and where its weak points are.
Side-Channel Attacks
These attacks don’t target the code directly. Instead, they look at how the hardware operates. Think about things like how much power a chip uses, how long certain operations take, or even the electromagnetic radiation it emits. By carefully measuring these physical characteristics, an attacker might be able to figure out secret information, like cryptographic keys. It’s like listening to the hum of a computer to guess what it’s doing. This indirect approach can be surprisingly effective against even well-protected systems.
- Power Analysis: Measuring the power consumption of a device during cryptographic operations. Different operations consume different amounts of power, revealing patterns.
- Timing Attacks: Analyzing the time it takes for operations to complete. Variations in timing can leak information about secret data.
- Electromagnetic Analysis (EMA): Detecting and analyzing electromagnetic signals emitted by electronic devices. These signals can sometimes be correlated with internal operations.
Fault Injection Techniques
Fault injection is a bit more aggressive. The idea here is to deliberately introduce errors or glitches into the system while it’s running. This could be done by messing with the power supply, using lasers, or even changing the temperature. The goal is to make the system behave unexpectedly, perhaps skipping a security check or revealing sensitive data it normally wouldn’t. It’s a bit like trying to break a lock by hitting it with a hammer, but in a very precise, scientific way.
Introducing controlled errors can force a system to bypass security checks or reveal information it would normally keep hidden. This requires a good understanding of the target hardware and precise control over the faulting mechanism.
- Voltage Glitching: Briefly altering the power supply voltage to cause computational errors.
- Clock Glitching: Manipulating the clock signal to disrupt instruction execution.
- Electromagnetic Fault Injection (EMFI): Using focused electromagnetic pulses to induce faults in semiconductor devices.
Malware Targeting Trusted Execution Environments
Trusted Execution Environments (TEEs), like Intel SGX or ARM TrustZone, are designed to protect sensitive code and data. They create secure enclaves that are supposed to be isolated from the rest of the system. However, attackers are developing sophisticated malware specifically to try and break into these TEEs. This might involve finding vulnerabilities in the TEE’s implementation or using side-channel attacks that can still leak information from within the secure enclave. It’s a constant cat-and-mouse game, with security measures constantly being tested by new malware techniques.
- Enclave Exploitation: Finding and exploiting bugs within the TEE’s software or hardware implementation.
- Data Leakage from Enclaves: Using side-channel methods to infer data processed within a TEE, even if direct access is blocked.
- Attacks on TEE Management: Targeting the mechanisms that manage the creation and destruction of secure enclaves.
Impact of Root of Trust Exploitation
When the root of trust is compromised, the consequences can be pretty severe, rippling through entire systems and affecting everything that relies on that foundational security. It’s not just a minor glitch; it’s like the foundation of a building being weakened, making the whole structure unstable.
Systemic Compromise and Data Breaches
Exploiting the root of trust can give attackers a golden ticket to bypass many security checks. Imagine a scenario where the very first step in verifying a system’s integrity is broken. This allows malicious code or unauthorized access to slip in right from the start. This initial breach can then cascade, leading to widespread compromise across networks and systems. Attackers can move laterally with greater ease, accessing sensitive data that was supposed to be protected. This often results in significant data breaches, where confidential information is stolen or exposed.
Loss of Confidentiality and Integrity
Once the root of trust is undermined, the guarantees of confidentiality and integrity are also at risk. Confidentiality means keeping secrets secret, and integrity means making sure data hasn’t been tampered with. If the root of trust is broken, an attacker could potentially alter data without anyone knowing, or access information they shouldn’t. This could mean anything from changing financial records to stealing personal identities. It really shakes the confidence you have in the information you’re working with.
Erosion of User and System Trust
Perhaps one of the most significant long-term impacts is the erosion of trust. If users can’t trust that their devices and the systems they interact with are secure, they’ll be hesitant to use them. This applies to individuals using their personal devices, as well as businesses relying on their IT infrastructure. Rebuilding that trust after a root of trust compromise can be a long and difficult process. It affects not just the immediate users but also partners and customers who rely on the integrity of the compromised systems. This loss of trust can have lasting effects on reputation and business relationships, making it harder to operate effectively in the digital space. It’s a tough pill to swallow when the very foundation you built your digital interactions upon turns out to be shaky. For more on how attackers gain deeper network access, you can look into lateral movement techniques.
The implications of a compromised root of trust extend far beyond the initial breach. It fundamentally undermines the security assumptions upon which digital interactions are built, leading to a loss of confidence that can be difficult to regain. This necessitates a robust approach to security from the very beginning of any system’s lifecycle.
Real-World Scenarios of Root of Trust Exploitation
It’s one thing to talk about theoretical attacks, but seeing how these things play out in the real world really drives home why a secure root of trust matters so much. We’re not just talking about abstract concepts here; these are actual threats that have impacted systems and people.
Attacks on Secure Boot Processes
Secure boot is supposed to be the first line of defense, making sure only trusted software loads when a system starts up. But attackers have found ways around it. They might exploit a vulnerability in the bootloader itself, or perhaps trick the system into accepting a modified, malicious firmware update. This could allow them to load their own code before any security software even gets a chance to run. Think about it: if the very first step of starting your computer is compromised, everything that follows is built on a shaky foundation.
- Exploiting firmware vulnerabilities during the boot sequence.
- Tampering with bootloader configurations.
- Bypassing signature verification checks.
When the secure boot process is compromised, attackers can effectively gain control from the earliest stages of system initialization, making subsequent detection and mitigation significantly harder.
Compromise of Hardware Security Modules (HSMs)
HSMs are designed to be super secure places to store cryptographic keys. They’re supposed to be tamper-resistant and isolated. However, sophisticated attackers might try to find physical vulnerabilities. This could involve side-channel attacks to glean information about the keys, or even physical tampering if they can get their hands on the device. Imagine an attacker getting access to the keys that protect a company’s entire financial transactions – the damage could be immense.
| Attack Type | Target Component | Potential Impact |
|---|---|---|
| Side-Channel | Cryptographic Key | Key leakage, unauthorized decryption |
| Fault Injection | HSM Firmware | Bypassing security checks, unauthorized access |
| Physical Tampering | HSM Enclosure | Direct access to keys, hardware modification |
Exploitation in IoT and Embedded Systems
This is a big one. So many Internet of Things (IoT) devices and embedded systems, from smart home gadgets to industrial control systems, are built with limited resources and often lack robust security. Their root of trust might be weak or non-existent. Attackers can exploit these weaknesses to take over devices, use them in botnets, or gain access to the networks they’re connected to. It’s a constant battle because these devices are often deployed in large numbers and are hard to update or manage securely.
- Default or weak credentials on devices.
- Unpatched firmware with known vulnerabilities.
- Lack of secure update mechanisms for the root of trust.
These scenarios highlight that even specialized security hardware and processes aren’t immune. Attackers are constantly looking for the weakest link, and often, that link is found in the foundational trust mechanisms of a system.
Mitigation Strategies Against Exploitation
So, how do we actually stop these root of trust exploits from happening in the first place? It’s not like you can just flip a switch. It really comes down to building things right from the start and then keeping a close eye on them. Think of it like building a house; you need a solid foundation, strong walls, and then you need to maintain it.
Secure Hardware Design Principles
When we’re talking about hardware, the root of trust needs to be baked in from the very beginning. This means designing chips and components with security as a top priority, not an afterthought. We’re talking about things like making sure the physical hardware is resistant to tampering and that sensitive operations happen in isolated parts of the chip. It’s about creating a hardware foundation that’s inherently trustworthy.
- Physical Tamper Resistance: Designing hardware to detect and resist physical intrusion attempts.
- Hardware Root of Trust (HRoT): Embedding a secure, immutable core within the hardware that boots first and verifies subsequent components.
- Secure Element Integration: Utilizing dedicated secure chips for storing cryptographic keys and performing sensitive operations.
Robust Firmware Development Practices
Firmware is like the operating system for hardware, and if it’s not secure, the whole system is at risk. This means developers need to follow strict coding rules, avoid common mistakes, and test their firmware thoroughly. It’s about writing code that’s clean, predictable, and doesn’t leave any obvious doors open for attackers. We need to treat firmware with the same seriousness as any other software component.
- Secure Coding Standards: Adhering to guidelines that prevent common vulnerabilities like buffer overflows and injection flaws.
- Regular Auditing and Testing: Performing static and dynamic analysis, fuzzing, and penetration testing on firmware.
- Minimizing Attack Surface: Removing unnecessary features and services from the firmware to reduce potential entry points.
Advanced Cryptographic Implementations
Cryptography is the backbone of trust, but only if it’s done right. This involves using strong, modern encryption algorithms and, perhaps more importantly, managing the cryptographic keys very carefully. Keys are like the master keys to your kingdom, so losing them or having them stolen is a disaster. We need to make sure keys are generated securely, stored safely, and rotated regularly. It’s a whole lifecycle management process that’s absolutely critical for maintaining trust. You can find more information on secure key management here.
The goal is to create layers of defense, so even if one part is compromised, the entire system doesn’t collapse. It’s about building resilience into the very fabric of our digital systems.
Defensive Measures for Root of Trust
Protecting the root of trust isn’t a one-and-done deal; it’s an ongoing effort. Think of it like maintaining a fortress – you don’t just build the walls and walk away. You need to constantly check for weak spots, update your defenses, and keep an eye on who’s coming and going.
Regular Security Audits and Testing
Regular checks are super important. This means bringing in outside experts or using internal teams to poke and prod at your systems, looking for any cracks in the armor. They’ll try to break in, just like a real attacker would, to see what happens. This isn’t about finding blame; it’s about finding problems before they become big issues.
- Penetration Testing: Simulating real-world attacks to find exploitable vulnerabilities.
- Vulnerability Assessments: Regularly scanning systems for known weaknesses.
- Code Reviews: Having developers or security experts look over the code for potential flaws.
- Configuration Audits: Checking that all system settings are secure and as intended.
It’s easy to get complacent when things seem to be working fine. But the threat landscape changes daily, and what was secure yesterday might not be today. Proactive testing helps you stay ahead of the curve.
Secure Key Management Lifecycle
Cryptographic keys are like the master keys to your digital kingdom. If someone gets their hands on them, all bets are off. So, managing these keys properly from the moment they’re created until they’re no longer needed is critical. This involves a lot of careful planning and strict procedures.
- Generation: Creating strong, random keys using secure methods.
- Storage: Keeping keys safe, often in specialized hardware security modules (HSMs).
- Distribution: Getting keys to where they’re needed without exposing them.
- Rotation: Regularly changing keys to limit the impact if one is compromised.
- Revocation: Disabling keys that are no longer needed or are suspected of being compromised.
Continuous Monitoring of Trusted Components
Once you’ve got your root of trust set up and secured, you can’t just forget about it. You need to keep watching it. This means monitoring the hardware, firmware, and any software that’s considered part of that trusted foundation. If something unexpected happens – a change in configuration, an unusual access attempt, or a performance anomaly – you need to know about it right away.
- Integrity Checks: Verifying that critical components haven’t been tampered with.
- Access Logging: Keeping a detailed record of who or what accessed trusted components.
- Behavioral Analysis: Looking for patterns that deviate from normal, expected activity.
- Alerting: Setting up systems to notify you immediately when suspicious events occur.
The Evolving Threat Landscape

The world of cybersecurity is always shifting, and when it comes to protecting our root of trust, things are no different. Attackers aren’t standing still; they’re constantly finding new ways to poke holes in our defenses. It feels like every time we get a handle on one threat, two more pop up. This constant evolution means we can’t afford to get complacent.
Emerging Attack Sophistication
We’re seeing attackers get smarter, more organized, and frankly, more patient. It’s not just about random script kiddies anymore. We’re dealing with sophisticated groups, sometimes backed by nations, who have serious resources. They’re not just looking for a quick win; they’re planning long-term campaigns. Think about Advanced Persistent Threats (APTs) – these guys can stay hidden in a network for months, even years, slowly siphoning off data or setting up for a major disruption. They’re also getting really good at combining different attack methods. One minute they might be using a phishing email to get a foothold, the next they’re exploiting a zero-day vulnerability that nobody even knew existed yet. It makes detecting them incredibly difficult because they don’t always stick to one playbook.
Challenges in Securing Modern Architectures
Our tech is getting more complex, too. We’ve got cloud computing, the Internet of Things (IoT), and more devices connecting all the time. Each of these brings its own set of security headaches. For instance, many IoT devices are built with cost in mind, not security. They often lack basic features like strong passwords or ways to update their software, making them easy targets. Then there’s the cloud – while it offers a lot of benefits, misconfigurations are a huge problem. A simple mistake in setting up access controls can leave sensitive data wide open. It’s a constant race to keep up with securing these new environments before attackers figure out how to exploit them.
The Role of Supply Chain in Root of Trust Security
This is a big one that people sometimes overlook. We rely on a lot of different companies and software components to build our systems. A supply chain attack happens when attackers go after one of these trusted partners instead of attacking you directly. Imagine a software vendor gets compromised, and then the malicious code gets pushed out to all their customers through a seemingly legitimate update. Suddenly, thousands of organizations are affected. This is particularly worrying for root of trust because the very components that are supposed to be secure might be compromised before they even reach you. It means we have to trust not only our own security practices but also those of everyone involved in making the hardware and software we use.
Here’s a quick look at some common threats we’re seeing:
- Ransomware: It’s not just about encrypting files anymore. Attackers are stealing data first and then demanding payment, threatening to release it if you don’t pay (double extortion). Some even add a third layer, like launching denial-of-service attacks.
- Phishing & Social Engineering: These attacks prey on human trust. They’re getting more personalized, using AI to create convincing fake emails or even voice messages to trick people into giving up sensitive information or clicking malicious links.
- Zero-Day Exploits: These are attacks that use vulnerabilities nobody knows about yet, meaning there are no patches available. They’re highly valuable to attackers and tough to defend against using traditional methods.
The landscape is always changing. What worked yesterday might not work tomorrow. We need to be proactive, not just reactive, and constantly reassess our defenses.
Best Practices for Maintaining Root of Trust Integrity
Keeping your root of trust solid is like making sure the foundation of your house is strong. If that part gets shaky, everything built on top is at risk. It’s not a one-and-done thing, either; it needs constant attention.
Implementing Zero Trust Principles
This is a big one. The whole idea behind Zero Trust is simple: don’t trust anyone or anything by default, even if they’re already inside your network. Every access request needs to be verified, every time. Think of it like needing to show your ID every time you enter a room, not just at the front door. This means continuously checking user identities, device health, and the context of the access request. It assumes that breaches are going to happen and focuses on limiting the damage when they do.
- Verify explicitly: Always authenticate and authorize based on all available data points.
- Use least privilege access: Give users and systems only the access they absolutely need to do their job, and nothing more.
- Assume breach: Minimize the blast radius of any potential compromise by segmenting networks and applications.
Enforcing Least Privilege Access
This ties directly into Zero Trust. Least privilege means that a user, program, or process should have only the bare minimum permissions necessary to perform its intended function. If an account or system component gets compromised, the attacker’s ability to move around and cause damage is severely limited. It’s about reducing the potential impact of any single point of failure.
- Role-Based Access Control (RBAC): Assign permissions based on job roles rather than individual users.
- Regular Access Reviews: Periodically check who has access to what and remove any unnecessary permissions.
- Just-In-Time (JIT) Access: Grant elevated privileges only when needed and for a limited duration.
Comprehensive Incident Response Planning
Even with the best practices in place, incidents can still happen. Having a well-defined and practiced incident response plan is critical for minimizing downtime and data loss. This plan should outline the steps to take when a security event occurs, from detection and containment to eradication and recovery. It’s about being prepared to act quickly and effectively when the unexpected happens.
- Define roles and responsibilities: Clearly state who is responsible for what during an incident.
- Establish communication channels: Ensure clear and rapid communication among all stakeholders.
- Develop playbooks: Create step-by-step guides for common incident types.
- Practice regularly: Conduct tabletop exercises or simulations to test the plan’s effectiveness.
Maintaining the integrity of your root of trust isn’t just a technical challenge; it’s an ongoing commitment that requires a layered approach. By adopting principles like Zero Trust, strictly enforcing least privilege, and having a robust incident response plan ready to go, you build a much stronger defense against those who would seek to exploit your systems.
Wrapping Up: The Ever-Present Root of Trust Challenge
So, we’ve talked a lot about how attackers try to mess with the core of our digital systems, the ‘root of trust.’ It’s not just one thing; it’s a whole bunch of ways they try to get in, from tricking people with fake emails to finding tiny flaws in software that haven’t been fixed yet. And once they’re in, they try to get more control, like climbing a ladder to reach the top. This stuff can really mess up businesses, leading to stolen data or systems that just stop working. The main takeaway here is that staying safe means keeping systems updated, being careful about who gets access to what, and always keeping an eye out for weird activity. It’s a constant battle, and you can’t just set it and forget it. You have to keep working at it.
Frequently Asked Questions
What is root of trust exploitation?
Root of trust exploitation is when attackers break into the basic security system that a device or network relies on. This root of trust is supposed to make sure only trusted software and users can access important parts of a system. If it gets hacked, all security can fall apart.
Why is a secure root of trust so important?
A secure root of trust is like the foundation of a house. If it’s weak, everything built on top can be broken into or destroyed. It keeps your data safe and makes sure that only trusted programs can run on your computer or device.
How do attackers exploit hardware vulnerabilities?
Attackers find weaknesses in the physical parts of a computer or device, like chips or circuits. They might use special tools or signals to get secret information or make the hardware do things it shouldn’t.
What are some common ways the root of trust is attacked?
Some common ways include hacking into the firmware, stealing secret keys, using malware to trick the system, or even using physical attacks like shining a bright light or sending electrical shocks to a device.
What happens if the root of trust is compromised?
If the root of trust is broken, attackers can control the whole system. They could steal data, install malware, or make the device do harmful things. It can also make people lose trust in the system or device.
How can organizations protect their root of trust?
Organizations can protect their root of trust by using strong hardware, keeping firmware updated, using strong passwords and encryption, and checking their systems regularly for problems.
What are some real-life examples of root of trust exploitation?
Examples include hackers breaking secure boot processes, stealing keys from hardware security modules (HSMs), or attacking smart devices in homes and factories to take control or steal data.
What should I do if I think my device’s root of trust has been attacked?
If you think your device has been attacked, disconnect it from the network, tell your IT or security team, and don’t use it until it has been checked and fixed. It’s important to act quickly to stop further damage.
