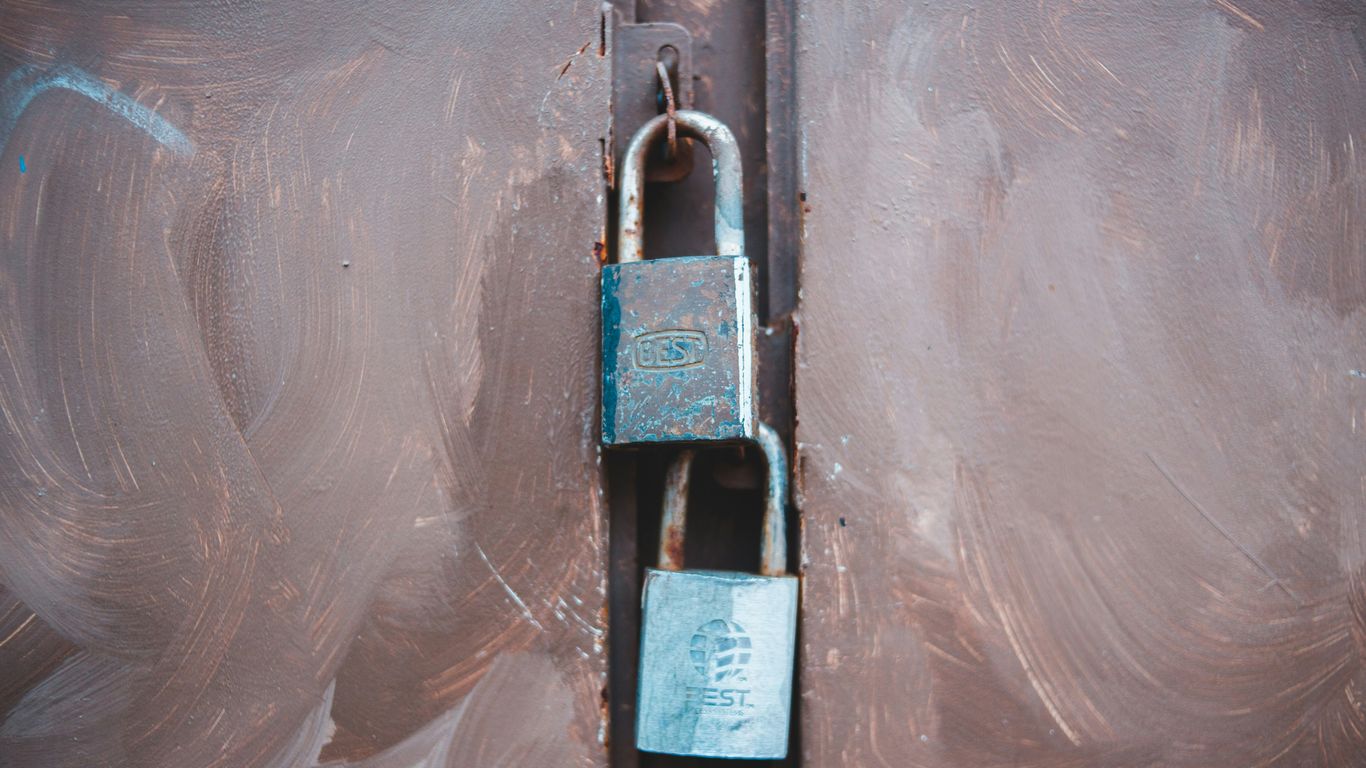
In today’s digital world, keeping your online accounts safe is a big deal. Passwords alone just don’t cut it anymore. That’s where multi-factor authentication, or MFA, comes in. It’s like adding extra locks to your digital doors, making it way harder for bad actors to get in. We’ll break down what multi factor authentication is, how it works, and why it’s become such a common tool for protecting your information.
Key Takeaways
- Multi-factor authentication (MFA) means using more than just a password to log in, making accounts much harder to break into.
- The core idea behind MFA is combining different types of verification: something you know (like a password), something you have (like a phone), and something you are (like a fingerprint).
- Common ways to use MFA include codes sent to your phone, special apps, or even your fingerprint, offering various levels of convenience and security.
- Using MFA significantly lowers the chance of your accounts being hacked, which is a huge win for both individuals and businesses.
- While MFA is great, attackers are finding new ways to get around it, like tricking people into approving login requests (MFA fatigue) or taking over phone numbers (SIM swapping).
Understanding Multi-Factor Authentication
Definition of Multi-Factor Authentication
Multi-Factor Authentication, or MFA, is a security method that requires more than one way to prove you are who you say you are when you log into something. Think of it like needing a key, a special code, and maybe even a fingerprint to get into a really secure building. It’s not just about having a password anymore. The goal is to add extra layers of protection so that even if someone gets their hands on your password, they still can’t get into your accounts. It’s a big step up from just using a single password, which, let’s be honest, can sometimes be pretty weak.
How Multi-Factor Authentication Works
So, how does MFA actually work? It’s pretty straightforward. When you try to log in, you first enter your usual password, which is the ‘something you know’ part. Then, the system asks for a second piece of proof. This could be a code sent to your phone via text message, a special code generated by an app on your phone, or even a physical security key you plug into your computer. This second step verifies that you not only know the password but also have access to a specific device or code. This makes it much harder for unauthorized people to get in, even if they have your login details. It’s a common practice for securing online accounts today.
Expanded Explanation of Multi-Factor Authentication
Let’s break down MFA a bit more. The core idea is to use at least two different categories of proof to confirm your identity. These categories are generally:
- Something You Know: This is typically your password or a PIN. It’s information only you should possess.
- Something You Have: This refers to a physical item you possess, like your smartphone (which receives codes), a hardware security key, or a smart card.
- Something You Are: This involves unique biological traits, such as your fingerprint, facial scan, or iris pattern. These are biometrics.
By requiring verification from at least two of these distinct categories, MFA creates a much more robust security posture than relying on a single factor alone. For instance, a common setup is a password (something you know) combined with a code from an authenticator app on your phone (something you have). This layered approach significantly reduces the risk of account takeover, even if one factor is compromised. It’s a key part of modern identity management and helps protect against various credential stuffing attacks.
MFA is not just a technical solution; it’s a strategic approach to security. By layering different verification methods, organizations can dramatically reduce the likelihood of unauthorized access and protect sensitive data from a wide range of threats, from simple password guessing to more sophisticated social engineering tactics. It’s about making it inconvenient for attackers and more secure for legitimate users.
Core Components of Multi-Factor Authentication
Multi-factor authentication, or MFA, isn’t just about adding an extra step to logging in. It’s built on a simple, yet powerful, principle: using multiple, distinct types of proof to confirm you are who you say you are. Think of it like needing more than just your house key to get into a secure building. Each component taps into a different category of evidence, making it much harder for unauthorized individuals to gain access, even if they manage to steal one piece of information.
Something You Know
This is the most common factor, and it’s what most people think of first when they hear ‘authentication’. It’s information that only you should possess. The classic example is a password or a PIN. Because it’s based on knowledge, it’s also the most vulnerable. Passwords can be forgotten, guessed, or, more commonly these days, stolen through phishing attacks, data breaches, or brute-force attempts. The security of this factor relies heavily on its complexity and uniqueness.
Something You Have
This factor involves a physical item that you possess. It’s something tangible that proves your identity. Examples include a smartphone that receives a one-time code via SMS or an authenticator app, a hardware security key (like a YubiKey), or even a smart card. The idea here is that an attacker would need to physically obtain this item in addition to knowing your password. This makes it significantly more difficult to compromise your account remotely. However, these items can be lost, stolen, or damaged, which is why having a backup method is often recommended.
Something You Are
This category, often referred to as biometrics, uses unique biological characteristics to verify identity. This could be your fingerprint, your face (facial recognition), your iris (iris scan), or even your voice. These are inherently tied to your physical self, making them very difficult to replicate or steal. While convenient and generally secure, biometric data can sometimes be spoofed with advanced techniques, and privacy concerns are often raised about how this sensitive data is stored and managed.
The strength of MFA comes from combining at least two of these independent factors. For instance, using a password (something you know) along with a code from your phone (something you have) creates a much more robust security barrier than relying on just a password alone.
Common Multi-Factor Authentication Methods
When we talk about making sure only the right people get into our accounts, multi-factor authentication (MFA) is the name of the game. It’s not just about passwords anymore; it’s about adding extra layers of security. Think of it like having multiple locks on your front door instead of just one. This section breaks down some of the most common ways MFA is put into practice.
Authenticator Applications
These apps, like Google Authenticator or Microsoft Authenticator, are pretty popular. They generate a time-based, one-time password (TOTP) that changes every 30 to 60 seconds. When you log in, after entering your password, you’ll be prompted to enter the current code from your authenticator app. It’s a step up from SMS codes because the codes aren’t sent over a potentially less secure network. Plus, you don’t need cell service to generate the codes, which is handy when you’re traveling.
- How it works: The app and the server share a secret key and use an algorithm to generate the same changing code.
- Pros: Generally more secure than SMS, works offline, codes refresh frequently.
- Cons: Requires installing an app, can be a hassle if you lose your phone.
Hardware Security Keys
These are small physical devices, often looking like a USB drive, that you plug into your computer or tap on your phone. They use cryptography to verify your identity. When prompted, you insert the key and might have to touch a button on it. Hardware security keys are considered one of the most secure MFA methods available because they are resistant to phishing and can’t be easily duplicated or stolen remotely. Companies like YubiKey and Google Titan are well-known for these. They often support standards like FIDO2, which is designed for strong, phishing-resistant authentication.
- Types: USB-A, USB-C, NFC, Bluetooth.
- Verification: Often involves a physical touch or PIN entry on the key itself.
- Security: High resistance to phishing and man-in-the-middle attacks.
Biometric Verification
This method uses your unique biological traits to confirm who you are. Think fingerprint scanners on your phone, facial recognition (like Face ID), or even iris scans. It’s convenient because you don’t need to remember anything extra or carry a separate device. However, the security of biometrics can vary. While generally harder to fake than a password, there have been instances where sophisticated methods could bypass them. It’s often used as a second factor after a password or PIN, or to unlock a device that then provides access to other services.
- Examples: Fingerprints, facial scans, voice recognition, iris scans.
- Convenience: High, as it uses personal characteristics.
- Considerations: Privacy concerns and potential for sophisticated spoofing.
SMS and Voice Codes
This is one of the older and more widely used MFA methods. When you try to log in, a code is sent to your registered phone number via text message (SMS) or a voice call. You then enter this code on the login screen. It’s easy to set up and most people have a mobile phone. However, it’s also considered one of the less secure options. SMS messages can be intercepted, and SIM swapping attacks, where an attacker takes over your phone number, are a significant risk. Many security experts recommend avoiding SMS-only MFA when other options are available. This method is widely adopted but has known vulnerabilities.
- Delivery: Via text message or automated phone call.
- Ease of Use: High, requires only a phone.
- Security Concerns: Vulnerable to interception and SIM swapping.
While convenient, relying solely on SMS for multi-factor authentication introduces significant security risks that can be exploited by attackers. It’s generally advisable to opt for more robust methods when possible.
Advanced Multi-Factor Authentication Strategies
While standard multi-factor authentication (MFA) methods provide a solid security baseline, the landscape of cyber threats is always changing. To stay ahead, organizations are looking at more sophisticated ways to implement and manage MFA. This involves not just adding more factors, but making the authentication process smarter and more resilient.
Adaptive Multi-Factor Authentication
Adaptive MFA, sometimes called risk-based authentication, is pretty neat. Instead of asking for the same second factor every single time, it looks at the situation. If you’re logging in from a familiar device and location, maybe it only needs your password. But if you’re logging in from a new country on a public computer? It’ll likely ask for that extra verification step. This approach balances security with user convenience. It aims to reduce friction for legitimate users while increasing hurdles for potential attackers. This kind of system often uses machine learning to figure out what’s normal and what’s suspicious. It’s a big step up from just blindly asking for a code every time. You can learn more about boosting online security with these kinds of habits.
Context-Aware Access Policies
Building on adaptive MFA, context-aware policies take the decision-making a step further. These policies consider a wider range of factors beyond just the user and device. Think about things like the time of day, the sensitivity of the resource being accessed, or even the user’s recent activity. For example, an employee might be allowed to access company email from their work laptop during business hours, but accessing the same email from a personal device late at night might trigger a more rigorous authentication process or even be blocked entirely. This granular control helps prevent unauthorized access even if an attacker manages to obtain some legitimate credentials.
Phishing-Resistant Multi-Factor Authentication
Phishing remains a persistent threat, and even MFA isn’t always immune. Some MFA methods, like SMS codes, can be intercepted or tricked through social engineering. Phishing-resistant MFA methods are designed to be much harder for attackers to compromise. Hardware security keys, for instance, require a physical device that the attacker would need to possess. FIDO2/WebAuthn standards are also leading the way, offering strong authentication that is resistant to phishing attacks. Implementing these methods is key for protecting against sophisticated attacks that aim to steal credentials or trick users into revealing their second factors. For online stores, implementing MFA is a critical step to prevent account takeovers.
Implementing Multi-Factor Authentication Effectively
So, you’ve decided to roll out multi-factor authentication (MFA), which is a really smart move. But just having it isn’t the whole story, right? You’ve got to put it in place the right way to actually get the benefits. It’s like buying a fancy lock for your door – it’s only useful if you install it properly and actually use it.
Best Practices for Multi-Factor Authentication Deployment
When you’re setting up MFA, think about making it as smooth as possible for people while keeping it secure. Nobody likes a system that’s a pain to use, because then they’ll look for ways around it. Here are some things to keep in mind:
- Choose the right factors: Don’t just grab the first MFA option you see. Think about what makes sense for your users and your systems. For example, using an authenticator app is generally better than SMS codes because it’s less prone to certain types of attacks.
- Roll it out gradually: Instead of flipping a switch for everyone at once, try a pilot group first. See what works, what doesn’t, and gather feedback. This helps you iron out any kinks before a full launch.
- Provide clear instructions: Make sure everyone knows why MFA is being implemented and how to use it. Simple guides, maybe even short videos, can go a long way.
- Offer support: Have a plan for when users get stuck. Whether it’s a help desk or a dedicated support channel, people need to know where to turn if they have trouble with their second factor.
Enforcing Multi-Factor Authentication Across All Accounts
This is a big one. You can have the best MFA system in the world, but if people only use it for their email and not their other important accounts, you’ve still got weak spots. It’s really about making sure that every account that matters has MFA turned on. Think about it: if an attacker can get into your accounting software with just a password because MFA wasn’t enabled there, all that other security you put in place might not matter much.
The goal is to create a consistent security posture. Leaving accounts unprotected is like leaving a back door unlocked while you’ve bolted the front door shut. It’s an invitation for trouble.
Avoiding SMS-Only Implementations
Okay, so SMS codes are better than nothing, but they’re really not ideal for serious security. Why? Because of things like SIM swapping. An attacker can trick your mobile carrier into transferring your phone number to a SIM card they control. Once they have your number, they can intercept those SMS codes and bypass your MFA. It’s a pretty common way for attackers to get around this layer of security. So, while you might use SMS as a fallback in a pinch, it shouldn’t be your primary or only method. Pushing users towards authenticator apps or hardware keys is a much safer bet for long-term security.
Detecting and Responding to Multi-Factor Authentication Issues
Even with multi-factor authentication (MFA) in place, things can still go sideways. It’s not just about setting it up; you’ve got to keep an eye on how it’s working and be ready to jump in if something looks off. Think of it like having a security guard – they’re there to help, but you still need to check in with them and make sure they’re doing their job right.
Monitoring Failed Multi-Factor Authentication Attempts
Seeing a lot of failed MFA attempts from a single user or a group of users can be a red flag. It might mean someone is trying to brute-force their way in, or maybe a user is having trouble with their authentication method. It’s important to track these to spot potential attacks early. A sudden spike in failures, especially from unusual locations or times, needs a closer look.
Alerting on Unusual Authentication Requests
Your systems should be set up to flag anything that seems out of the ordinary. This could be a login attempt from a new device, a location far from where the user normally works, or at a time when they’re usually offline. These alerts are your early warning system. They give you a chance to investigate before a real problem develops. It’s about being proactive rather than just reacting after a breach.
Resetting Authentication Factors and Reviewing Activity
If you do spot suspicious activity, or if a user reports a lost or compromised authentication factor (like a phone with an authenticator app), you need a clear process. This usually involves temporarily disabling the account, forcing a reset of the authentication method, and then reviewing recent login activity. This helps ensure that any unauthorized access is stopped and that the user’s account is secure again. It’s a good idea to have a checklist for these situations so nothing gets missed.
When an MFA issue arises, the immediate goal is to contain any potential compromise. This means quickly revoking access for the affected factor or account and then thoroughly investigating the circumstances. A structured response plan can significantly reduce the time it takes to secure the environment and restore normal operations.
The Role of Multi-Factor Authentication in Security Frameworks
Multi-factor authentication (MFA) isn’t just a standalone security feature; it’s a cornerstone that supports and strengthens broader security frameworks. Think of it as a vital building block that makes other security measures more effective. Without robust identity verification, many other controls can falter.
Multi-Factor Authentication and Compliance Requirements
Many regulations and industry standards now mandate or strongly recommend MFA. This isn’t just about ticking a box; it’s about meeting a recognized level of security. For instance, frameworks like PCI DSS for payment card data, HIPAA for health information, and various ISO standards often point to MFA as a key control for protecting sensitive data. Failing to implement it can lead to audit failures and penalties.
Here’s a look at how MFA fits into common compliance needs:
| Standard/Regulation | MFA Relevance |
|---|---|
| PCI DSS | Protects cardholder data from unauthorized access |
| HIPAA | Safeguards protected health information (PHI) |
| GDPR | Supports data protection and user consent |
| NIST | Recommended for identity assurance |
| SOC 2 | Demonstrates strong access controls |
Multi-Factor Authentication as a Foundational Control
In many security models, MFA is considered a foundational control. This means it’s one of the first and most important layers of defense you put in place. It directly addresses the risk of compromised credentials, which is a leading cause of data breaches. By requiring more than just a password, MFA significantly raises the bar for attackers. It’s a practical way to implement the principle of defense in depth, adding a critical layer of verification.
MFA acts as a gatekeeper, ensuring that even if one security credential is stolen, an attacker still needs to overcome additional verification steps to gain access. This makes it a highly effective barrier against many common cyber threats.
Multi-Factor Authentication in Zero Trust Architectures
Zero Trust is a security model that operates on the principle of "never trust, always verify." In this environment, MFA is absolutely critical. Instead of assuming trust based on network location, Zero Trust requires continuous verification for every access request. MFA provides a strong, verifiable identity signal that is essential for making dynamic access decisions. It helps confirm that the user attempting to access a resource is indeed who they claim to be, regardless of where they are connecting from. This constant re-verification is key to limiting the blast radius if a single credential or device is compromised.
Threats Targeting Multi-Factor Authentication
Even with multi-factor authentication (MFA) in place, attackers are finding ways to try and get around it. It’s not a magic bullet, unfortunately. While it’s a huge step up from just passwords, understanding how these defenses can be attacked is key to staying ahead. We’re seeing a rise in clever tactics designed specifically to bypass MFA, which means we need to be aware of them.
Understanding MFA Fatigue Attacks
MFA fatigue attacks, sometimes called push-bombing, are pretty straightforward but can be really effective. The attacker floods the user’s device with repeated authentication requests, hoping the user will eventually get annoyed and just approve one of them to make the notifications stop. It plays on human exhaustion and the desire to get rid of constant interruptions.
Here’s how it typically goes:
- An attacker obtains or guesses a user’s username and password, often through a data breach or phishing.
- They initiate a login attempt, triggering an MFA prompt (like a push notification to a mobile app).
- The attacker then repeatedly triggers new MFA requests. This can be done by canceling the previous request and immediately starting a new login attempt.
- The goal is to overwhelm the user with notifications, making them more likely to accidentally approve a malicious request just to get peace.
This type of attack highlights why users need to be trained to never approve MFA requests they didn’t initiate. It’s a good reminder that even strong security measures rely on human vigilance. For more on how MFA works and its limitations, check out this explanation.
The Impact of SIM Swapping
SIM swapping is a nasty trick where an attacker convinces your mobile carrier to transfer your phone number to a SIM card they control. Once they have your phone number, they can intercept SMS codes sent for MFA, effectively taking over your accounts. This is why relying solely on SMS for MFA is risky. It’s a direct attack on the ‘something you have’ factor when that ‘something’ is tied to your phone number. This can lead to significant account takeovers and various security problems.
Compromised Authentication Applications
Sometimes, the apps we use for MFA can themselves become targets. This could happen if the app itself has a vulnerability that attackers can exploit, or if the user’s device is compromised with malware that can intercept or manipulate the codes generated by the app. While generally more secure than SMS, no system is entirely foolproof. Attackers are always looking for the weakest link, and that can sometimes be the software or the device it runs on.
Attackers are constantly evolving their methods to bypass security controls. While MFA significantly strengthens security, it’s not impenetrable. Understanding these specific threats allows organizations and individuals to implement more robust defenses and user training programs, moving beyond basic MFA to more resilient strategies.
Business Impact of Multi-Factor Authentication
Implementing multi-factor authentication (MFA) isn’t just about adding another security step; it has real, tangible effects on how a business operates and its overall health. Think of it as a robust shield that protects more than just data. It directly impacts the likelihood of experiencing a costly data breach, helps keep the company in line with various regulations, and safeguards the critical systems that keep the business running.
Reducing Breach Likelihood with Multi-Factor Authentication
This is probably the most talked-about benefit. Passwords alone are surprisingly weak. People reuse them, they’re often simple, and they can be stolen through various means like phishing or data dumps. MFA adds a significant hurdle for attackers. Even if they manage to get a password, they still need that second factor – like a code from a phone app or a physical key – which they usually don’t have. This dramatically cuts down the chances of unauthorized access. A study by the U.S. Government Accountability Office found that MFA can block over 99.9% of automated account compromise attacks. That’s a huge number when you consider how many attacks happen daily.
Protecting Critical Systems Through Multi-Factor Authentication
Certain systems within a company hold the keys to the kingdom, so to speak. These could be financial databases, customer records, intellectual property repositories, or the core infrastructure that runs operations. If these systems are compromised, the damage can be catastrophic. MFA acts as a gatekeeper for these high-value targets. By requiring multiple verification methods, it makes it much harder for malicious actors to gain access, even if they’ve already breached less sensitive parts of the network. This protection is vital for maintaining business continuity and preventing operational shutdowns.
Improving Compliance Posture with Multi-Factor Authentication
Many industries are subject to strict regulations regarding data protection and security. Think about HIPAA for healthcare, PCI DSS for payment card information, or GDPR for personal data in Europe. These regulations often mandate or strongly recommend multi-factor authentication, especially for accessing sensitive information. Implementing MFA helps organizations meet these requirements, avoiding hefty fines and legal trouble. It demonstrates a commitment to security that regulators look for. It’s not just about avoiding penalties, though; it’s about building trust with customers and partners who expect their data to be handled responsibly.
Future Trends in Multi-Factor Authentication

The world of digital security is always changing, and multi-factor authentication (MFA) is no exception. As threats get more sophisticated, so do the ways we protect ourselves. We’re seeing some pretty interesting shifts happening right now, and they’re worth paying attention to.
The Rise of Passwordless Authentication
Let’s be honest, remembering a bunch of complex passwords is a pain. That’s why passwordless authentication is gaining serious traction. Instead of typing in a password, you might use your fingerprint, a face scan, or a special security key. This approach aims to make logging in both more secure and way easier for everyone. It cuts down on the risk of stolen passwords, which is still a huge problem.
Here’s a quick look at how it’s shaping up:
- Biometrics: Using your unique physical traits like fingerprints or facial recognition. It’s convenient because you always have yourself with you.
- Hardware Security Keys: Small devices, often USB, that generate codes or confirm your presence. Think YubiKey or similar.
- Passkeys: A newer standard that uses cryptography to link authentication to a device, offering a more secure and user-friendly alternative to passwords.
Increasing Adoption of Biometric Multi-Factor Authentication
Biometrics are becoming a go-to for MFA. Your fingerprint scanner on your phone or laptop? That’s biometric authentication in action. It’s convenient because, well, you can’t forget your finger or face. As the technology gets better and more affordable, expect to see it pop up in more places, not just on your personal devices but also for accessing work systems or sensitive applications.
Evolution Towards Adaptive Multi-Factor Authentication
This is where things get really smart. Adaptive MFA, sometimes called risk-based or context-aware authentication, doesn’t just ask for multiple factors every single time. Instead, it looks at the situation. If you’re logging in from a familiar device, at your usual location, during normal work hours, it might only ask for one factor. But if something looks a bit off – maybe you’re logging in from a new country or at 3 AM – it’ll step up the security and ask for more verification. This approach balances security with user experience, reducing friction for legitimate users while keeping a close eye on potential threats.
The goal is to make security work for us, not against us. By understanding the context of a login attempt, systems can make smarter decisions about how much verification is truly needed, cutting down on unnecessary steps for everyday access while beefing up security when it matters most.
Wrapping Up: Making Security a Habit
So, we’ve talked a lot about multi-factor authentication, or MFA. It’s not just some techy buzzword; it’s a really important step to keep your accounts safe. Think of it like having a deadbolt on your door in addition to the regular lock. Passwords can get stolen or guessed, but MFA adds that extra layer that makes it way harder for bad actors to get in. Whether it’s a code sent to your phone, a fingerprint scan, or a special key, these methods work together to protect you. Making MFA a standard practice, both personally and in business, is one of the smartest moves you can make in today’s online world. It’s a big step towards better security for everyone.
Frequently Asked Questions
What exactly is Multi-Factor Authentication (MFA)?
Think of MFA as needing more than just your password to get into your online accounts. It’s like needing a key and a special code to open a door. MFA asks for at least two different ways to prove you are who you say you are, making it much harder for bad guys to break in even if they steal your password.
How does MFA make things safer?
It’s safer because even if someone steals or guesses your password (which is the ‘something you know’), they still can’t get in. They would also need the ‘something you have’ (like your phone) or the ‘something you are’ (like your fingerprint). This extra step stops most password-related break-ins.
What are the ‘factors’ in Multi-Factor Authentication?
The factors are the different types of proof you give. The most common ones are: 1. Something you know (like your password or a PIN). 2. Something you have (like your phone, a security key, or a special code sent to you). 3. Something you are (like your fingerprint or face scan).
Are all MFA methods equally secure?
Not really. Using an app on your phone or a physical security key is generally more secure than getting codes through text messages (SMS). This is because text messages can sometimes be intercepted or tricked, while apps and keys are harder to mess with.
What is an ‘MFA fatigue attack’?
This is a tricky way attackers try to get you to approve their login. They send tons of fake login requests to your phone or app, hoping you’ll get annoyed and just tap ‘approve’ without really looking. It’s like someone constantly buzzing your doorbell until you just open the door.
Why is MFA important for businesses?
For businesses, MFA is super important because it stops hackers from getting into company accounts and stealing important information. This helps avoid costly data breaches, keeps customers’ information safe, and makes sure the business follows security rules.
Can MFA stop all types of hacking?
MFA stops a lot of common attacks, especially those that rely on stealing passwords. However, very clever attackers might still find ways around it, like tricking you into giving up your second factor. That’s why it’s important to use strong MFA methods and stay aware of new tricks.
What does ‘passwordless authentication’ mean?
Passwordless authentication means logging in without typing a password at all! Instead, you might use your fingerprint, a face scan, or a special device to prove who you are. It’s a newer, often more convenient, and sometimes more secure way to access accounts.
