Ever feel like someone’s looking over your shoulder when you’re online? That’s kind of what man-in-the-browser attacks are all about. They’re sneaky ways criminals get in between you and the websites you use, often without you even knowing. It’s like having an unwanted guest in your digital house, messing with your mail and maybe even your bank account. We’re going to break down what these attacks are, how they happen, and what you can do to keep them from happening to you. It’s important stuff for anyone who uses the internet.
Key Takeaways
- Man-in-the-browser attacks involve a malicious program secretly sitting inside your web browser, letting attackers spy on or change your online activity.
- These attacks can happen through bad browser extensions, shady downloads, or even compromised software updates.
- Attackers use these methods to steal your login details, grab your personal info, and even mess with your online transactions.
- For users, this means risks like financial loss, identity theft, and a big hit to privacy.
- To stay safe, keep your browser and software updated, be careful with extensions, and use strong security practices like multi-factor authentication.
Understanding Man-in-the-Browser Attacks
The Nature of Man-in-the-Browser Attacks
Man-in-the-Browser (MitB) attacks represent a particularly insidious form of cyber threat. Unlike traditional Man-in-the-Middle attacks that intercept traffic between a user and a server, MitB attacks happen within the user’s own web browser. This means the malicious code is already on the victim’s machine, actively manipulating what the user sees and what data is sent to websites. The core danger lies in the attacker’s ability to silently alter transactions or steal credentials without the user’s knowledge. It’s like having a spy sitting right next to you, looking over your shoulder as you use your computer, but one that can also reach out and change what you’re doing.
Distinguishing Man-in-the-Browser from Other Interception Attacks
It’s important to know how MitB attacks differ from other common interception methods. Man-in-the-Middle (MITM) attacks, for instance, typically occur at the network level. An attacker might set up a rogue Wi-Fi hotspot or compromise a router to intercept data flowing between your device and the internet. They see the traffic, but they aren’t necessarily inside your browser’s execution environment. MitB, on the other hand, involves malware that has already infected the user’s system. This malware then injects malicious code directly into the browser process itself. This allows for a much deeper level of control, enabling the attacker to modify web pages, inject data into forms, or even alter transaction details after they’ve been submitted by the user but before they reach the intended server. Think of it this way: MITM is like tapping a phone line, while MitB is like having a mole inside the phone company who can change the conversation as it happens.
Core Mechanisms of Browser Compromise
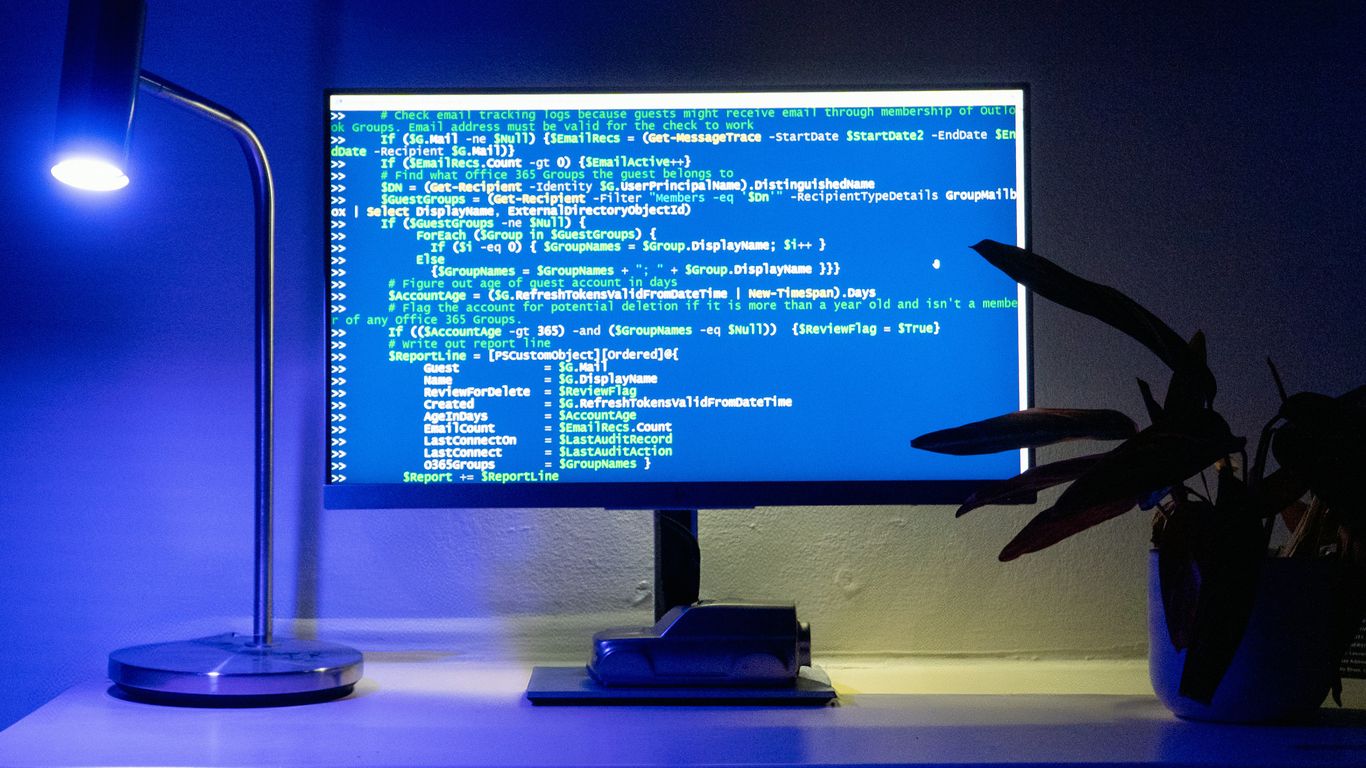
Getting malicious code into a user’s browser is the first hurdle for an attacker. This often happens through familiar vectors. One common method is through malicious browser extensions or plugins. Users might install these thinking they offer useful features, only to find they contain hidden malware. Another significant pathway is via drive-by downloads, where simply visiting a compromised website can trigger an automatic download of malware, often exploiting unpatched vulnerabilities in the browser or its plugins. Watering hole attacks are also a concern, where attackers compromise websites frequently visited by a specific target group. Finally, fake software updates or downloads from untrusted sources can also deliver the payload. Once the malware is on the system, it typically establishes a foothold and then injects its malicious code into the running browser processes, gaining the ability to interact with web content and user input.
Attack Vectors for Browser Exploitation
So, how do these attackers actually get their malicious code into your browser in the first place? It’s not like they can just walk up and plug a USB drive into your screen. They have to be a bit more clever.
Malicious Browser Extensions and Plugins
Think of browser extensions like little apps that add extra features to your web browser. Most of the time, they’re super helpful, right? But here’s the catch: they often need pretty broad permissions to do their job. This is where attackers see an opening. They might create an extension that looks useful, maybe a coupon finder or a PDF converter, and get it listed in the official browser stores. Once you install it, it can do all sorts of sneaky things in the background. It could be logging your keystrokes, redirecting you to fake login pages, or even injecting ads where they don’t belong. Because they run within your browser, they have a direct line to the websites you visit.
Drive-By Downloads and Watering Hole Attacks
These two are a bit different but share a common goal: getting you to download something nasty without you really realizing it. A drive-by download happens when you visit a website that’s been compromised. The site itself has been infected with malicious code, and just by loading the page, malware can start downloading onto your computer automatically. No clicking, no agreeing to anything – just visiting the site is enough. A watering hole attack is more targeted. Attackers figure out which websites a specific group of people (like employees at a certain company or members of an organization) tend to visit regularly. They then compromise one of those trusted sites. It’s like setting a trap where they know their prey is likely to show up. When the targeted individuals visit the infected site, they fall victim to whatever the attackers have set up, often a drive-by download.
Compromised Software Updates and Downloads
We all know it’s important to keep our software updated, right? Those updates often fix security holes. But what if the update itself is the problem? Attackers can try to trick you into downloading fake software updates. They might send you an email that looks like it’s from a popular software company, telling you to update immediately. Or, they might compromise a legitimate software download site. When you go to download what you think is a legitimate program or update, you’re actually getting malware. This is especially dangerous because we tend to trust software from known sources, making it easier for attackers to exploit that trust. It’s a classic bait-and-switch, but with potentially serious consequences for your system and data.
Techniques Used in Man-in-the-Browser Attacks
Man-in-the-browser (MitB) attacks are pretty sneaky. They don’t just sit outside your network; they get right inside your browser, where all your sensitive stuff happens. Think of it like someone hiding in your house instead of just trying to pick the lock. This allows attackers to do some pretty nasty things.
Credential Harvesting and Session Hijacking
One of the main goals for attackers is to get your login details. They can do this in a few ways. Sometimes, they’ll inject fake login fields into legitimate websites. You type in your username and password, thinking it’s the real deal, but it goes straight to the attacker. This is a form of credential harvesting. Once they have your credentials, they might also try to steal your session cookies. These cookies are like a temporary pass that keeps you logged in. If an attacker gets hold of one, they can use it to hijack your active session, pretending to be you without even needing your password. It’s a quick way to gain unauthorized access to your accounts.
- Fake login forms injected into websites
- Stealing session cookies to impersonate users
- Gaining access to accounts without needing passwords
Form Grabbing and Data Injection
Beyond just stealing what you type into login fields, MitB attacks can grab data from any form you fill out. This could be anything from personal details on a registration page to credit card information on an e-commerce site. The malware running in the browser can intercept this data before it’s even sent to the server. Even more concerning, attackers can also inject data into forms. Imagine you’re filling out a form to send money to a friend, and the attacker changes the recipient’s account number to their own. This kind of manipulation can lead to significant financial losses. It’s a direct alteration of your intended actions.
Transaction Manipulation and Redirection
This is where things get really serious, especially for online banking and shopping. Attackers can intercept financial transactions. They might alter the amount you intend to send, change the recipient, or even add extra fees. Sometimes, they’ll redirect you to a completely different, but convincing, website. You think you’re on your bank’s site, but you’re actually on a fake one controlled by the attacker. This allows them to capture all your details and manipulate transactions in real-time. It’s a sophisticated way to exploit the trust you place in your browser and the websites you visit. Staying safe online often means being aware of these hidden threats, and understanding how these attacks work is the first step toward better online security.
Attackers aim to make your browser do things you didn’t intend, whether it’s giving up your passwords or sending money to the wrong place. They exploit the trust between you, your browser, and the websites you interact with.
Impact of Man-in-the-Browser Attacks on Users
Man-in-the-Browser (MitB) attacks can really mess things up for regular folks. It’s not just about some abstract digital threat; it directly affects your money, your identity, and your peace of mind. When an attacker gets into your browser, they can see and do things without you even knowing. It’s like having a sneaky person looking over your shoulder while you do your online banking or shopping, but way worse.
Financial Fraud and Identity Theft
This is probably the most common and damaging outcome. Attackers can grab your login details for banks, credit card sites, or online stores. Once they have that, they can start making unauthorized purchases, transferring money out of your accounts, or even opening new lines of credit in your name. It’s a huge hassle to sort out, and the financial losses can be substantial. Imagine trying to explain to your bank why thousands of dollars are missing from your account – it’s a nightmare scenario.
Unauthorized Account Access and Control
Beyond just financial accounts, MitB attacks can give attackers access to almost any online service you use. This includes email, social media, cloud storage, and even work-related platforms. They can read your private messages, post on your behalf, steal sensitive documents, or lock you out of your own accounts. This loss of control can be incredibly disorienting and damaging, both personally and professionally. It’s a serious invasion of privacy.
Erosion of User Trust and Privacy Violations
When these attacks happen, it shakes your confidence in using the internet. You start to question which websites are safe and whether your personal information is truly protected. This erosion of trust makes people hesitant to engage in online activities, which can limit their ability to work, shop, or connect with others. The feeling that your online life is no longer private is a significant psychological burden. It makes you feel vulnerable.
Here’s a quick look at what can happen:
- Credential Theft: Your usernames and passwords are stolen.
- Session Hijacking: Attackers take over your active online sessions.
- Data Injection: Malicious information is inserted into your transactions.
- Transaction Manipulation: Legitimate transactions are altered or redirected.
The core problem with MitB attacks is that they happen after you’ve authenticated yourself to a website. The attacker is already inside your trusted session, making it incredibly hard for you to detect that anything is wrong. They exploit the trust between you and the website, turning your own browser against you. This makes it a particularly insidious form of cybercrime, exploiting human trust as a primary vector.
It’s a constant battle to stay ahead of these threats, and staying informed is key to protecting yourself. Keeping your browser and software updated is a good start, but understanding the risks is the first step to avoiding them.
Impact of Man-in-the-Browser Attacks on Organizations
Man-in-the-browser (MitB) attacks pose significant threats to organizations, extending far beyond individual user compromise. These attacks can lead to substantial financial losses, damage to reputation, and a breakdown of trust with customers and partners. When an organization’s systems are compromised through MitB tactics, the consequences can be far-reaching and difficult to recover from.
Financial Losses and Reputational Damage
One of the most immediate impacts is direct financial loss. MitB attacks can facilitate fraudulent transactions, redirecting funds or enabling unauthorized purchases. This can happen through credential harvesting, where attackers steal login details for banking or e-commerce platforms, or through transaction manipulation, where the attacker alters transaction details in real-time. Beyond the direct monetary loss, the reputational damage can be severe. Customers who experience fraud due to a breach in an organization’s systems may lose faith in the company’s ability to protect their information and assets. This erosion of trust can lead to customer attrition and difficulty in attracting new business. The cost of recovering from such incidents, including forensic investigations, system remediation, and potential legal fees, can also be substantial.
Compromised Customer Data and Intellectual Property
MitB attacks are a potent tool for data exfiltration. Attackers can intercept sensitive customer information, such as personally identifiable information (PII), financial details, or health records. This stolen data can then be sold on the dark web, used for identity theft, or leveraged in further social engineering attacks. For organizations, the loss of customer data can result in significant regulatory fines, especially under regulations like GDPR or CCPA. Furthermore, intellectual property (IP) can also be targeted. If an employee’s browser is compromised, attackers might gain access to proprietary information, trade secrets, or strategic plans, giving competitors an unfair advantage or enabling industrial espionage. Protecting sensitive data is paramount, and MitB attacks represent a direct threat to this objective.
Disruption of Business Operations and Services
While not always the primary goal, MitB attacks can indirectly lead to significant operational disruptions. If an attacker gains control of an employee’s account, they might use that access to launch further attacks within the organization’s network, potentially leading to system outages or data corruption. For instance, compromised credentials could be used to deploy ransomware or initiate denial-of-service attacks, halting critical business functions. The need to investigate and remediate such incidents can pull resources away from core business activities, leading to lost productivity and missed opportunities. The complexity of modern web applications and the increasing reliance on third-party integrations mean that a single point of compromise can have cascading effects throughout an organization’s digital infrastructure.
Defending Against Man-in-the-Browser Threats
So, how do we actually fight back against these sneaky man-in-the-browser attacks? It’s not just about hoping for the best; we need a solid plan. Think of it like building a fortress – you need strong walls, watchful guards, and educated citizens.
Implementing Strong Authentication Measures
First off, making it harder for attackers to get in is key. This means going beyond just a password. Multi-factor authentication (MFA) is a big one. It’s like needing two different keys to open a door, not just one. Even if someone steals your password, they still can’t get into your account without that second factor, like a code from your phone or a fingerprint. We also need to watch out for how people are logging in. Are there weird login times or locations? Systems that flag suspicious activity can alert us to potential trouble before it gets out of hand. Strong authentication is your first line of defense against unauthorized access.
Securing Web Applications and APIs
For the folks building websites and apps, security needs to be baked in from the start. This isn’t an afterthought. We’re talking about writing code that doesn’t have obvious holes, like making sure user input is handled properly to stop things like injection attacks. APIs, which are like the communication channels between different software parts, also need to be locked down tight. If these aren’t secure, they can become easy entry points. It’s about building robust applications that can withstand attacks, not just look pretty. Think about using tools that scan your code for weaknesses before it ever goes live. You can find more on securing web applications here.
User Education and Awareness Training
Honestly, a lot of these attacks prey on people not knowing any better. That’s where education comes in. We need to teach users about the risks, like not clicking on suspicious links or downloading files from untrusted sources. Phishing emails are still a huge problem, and a well-informed user is much less likely to fall for them. It’s about making people aware of common tricks, like fake software updates or urgent requests for personal information. Regular training sessions, even short ones, can make a big difference. It’s not just about telling people what not to do, but why it’s dangerous. A little knowledge goes a long way in preventing these kinds of attacks.
Technical Defenses Against Browser Exploitation
When we talk about keeping our online activities safe, the browser is a big part of the picture. It’s our main window to the internet, and unfortunately, that makes it a prime target for attackers. So, what can we actually do on a technical level to make our browsers tougher to crack?
Browser Hardening and Security Settings
First off, just using your browser out of the box isn’t always enough. You’ve got to tweak some settings to make it more secure. Think of it like reinforcing the locks on your house. Most browsers have built-in features designed to block malicious sites, manage cookies, and control what extensions can do.
Here are a few things to look at:
- JavaScript Control: While essential for many websites, JavaScript can also be a vector for attacks. Consider adjusting your browser’s JavaScript settings to block scripts from untrusted sources or to require permission before they run. This can break some site functionality, but it’s a trade-off for better security.
- Pop-up Blockers: These are pretty standard now, but make sure yours is enabled. Unwanted pop-ups can sometimes be used to trick you into downloading malware or visiting fake sites.
- Tracking Prevention: Most modern browsers offer some level of tracking prevention. Enabling these features can limit how websites and advertisers follow your online activity, which indirectly helps by reducing the attack surface for personalized social engineering.
- Safe Browsing Features: Services like Google’s Safe Browsing or Microsoft Defender SmartScreen warn you about dangerous websites and downloads. Keeping these active is a no-brainer.
It’s also a good idea to regularly review your browser’s privacy and security settings. What’s considered secure today might be less so tomorrow. Staying updated on browser security best practices is key.
Endpoint Protection and Malware Detection
Beyond the browser itself, the device you’re using needs protection too. This is where endpoint protection comes in. We’re talking about antivirus software, anti-malware tools, and more advanced endpoint detection and response (EDR) systems. These tools work by scanning files, monitoring processes, and looking for suspicious behavior that might indicate a man-in-the-browser attack is underway.
- Real-time Scanning: Make sure your security software is set to scan files and network traffic in real-time. This way, it can catch threats before they even get a chance to execute.
- Regular Updates: Malware evolves constantly, and so do the tools to fight it. Keep your antivirus and anti-malware software updated with the latest definitions and program updates. This is non-negotiable.
- Behavioral Analysis: Modern security solutions often use behavioral analysis to spot unusual activity, even if the specific malware hasn’t been seen before. This is particularly useful against zero-day exploits that might be used in sophisticated attacks.
Think of your endpoint protection as the security guard for your computer. It’s constantly watching for trouble and can stop threats before they cause real damage. For organizations, robust endpoint security is a foundational element of their defense strategy.
Web Application Firewalls and Intrusion Detection
While browser hardening and endpoint protection focus on the user’s side, web application firewalls (WAFs) and intrusion detection systems (IDS) work on the server side to protect the websites and applications themselves. A WAF acts like a shield in front of your web application, filtering out malicious traffic and blocking common attacks like SQL injection or cross-site scripting (XSS). An IDS, on the other hand, monitors network traffic for suspicious patterns that might indicate an ongoing attack, alerting administrators to potential problems.
- WAFs for Input Validation: WAFs can be configured to enforce strict input validation rules, which helps prevent malicious scripts or commands from being injected into web applications. This is a direct countermeasure against many common web attack vectors.
- IDS for Anomaly Detection: By analyzing network traffic, an IDS can identify deviations from normal behavior that might signal an attack, such as unusual data transfer volumes or connection attempts from suspicious IP addresses. This helps in detecting threats that might bypass other security layers.
- Layered Security: Combining WAFs and IDS creates a layered defense. The WAF stops known threats at the application level, while the IDS monitors for broader network anomalies, providing a more comprehensive security posture. This approach is vital for protecting against complex threats like Advanced Persistent Threats.
These server-side defenses are critical for organizations to protect their users and their own infrastructure from the various ways attackers try to compromise web applications and the data they handle.
Advanced Man-in-the-Browser Attack Trends
Man-in-the-browser attacks aren’t standing still; they’re evolving right alongside our digital tools. Attackers are getting smarter, using new tricks to get past our defenses. It’s not just about old-school malware anymore. We’re seeing a shift towards more sophisticated methods that are harder to spot.
AI-Driven Social Engineering Tactics
Artificial intelligence is really changing the game for attackers. They’re using AI to craft incredibly convincing phishing messages that are tailored to specific individuals. Think about it: an email that sounds exactly like it’s from your boss, using language and details only they would know. AI can also generate realistic-sounding voice or video for scams, making it much harder for people to tell what’s real. This makes social engineering attacks far more effective and scalable than ever before.
Exploitation of Single-Page Applications
Modern web applications, especially single-page applications (SPAs), present new opportunities for attackers. SPAs load content dynamically without full page reloads, which can sometimes create unique vulnerabilities. Attackers might look for ways to inject malicious scripts or manipulate data as it’s being loaded or processed. This is different from older websites where attacks might have been more straightforward.
Cross-Platform and Mobile Browser Attacks
Attackers aren’t just focusing on desktop browsers anymore. They’re increasingly targeting mobile browsers and even cross-platform applications. This means that a vulnerability found in one type of browser or operating system might be adapted to work on others. The sheer variety of devices and platforms out there makes it a challenge to secure everything. It’s a constant game of catch-up to protect users wherever they are accessing the web.
Mitigating Browser-Based Interception Risks
Secure Development Practices for Web Applications
When building web applications, it’s really important to think about how attackers might try to get in between your users and your service. One big area is how the application handles data and user sessions. If you’re not careful, attackers can exploit weaknesses to intercept or change what’s going on. This means we need to build things with security in mind from the start, not as an afterthought. Think about things like making sure every sensitive action requires a re-authentication, or using specific security features in your code.
- Implement Anti-CSRF Tokens: These are unique, secret, unpredictable values sent to the client and included in subsequent state-changing requests. The server then checks if the token matches, preventing attackers from forcing a user’s browser to make unwanted requests.
- Utilize Same-Site Cookies: This browser feature helps mitigate CSRF by controlling when cookies are sent with cross-site requests. Setting them to
StrictorLaxcan significantly reduce exposure. - Validate All State-Changing Requests: Don’t just trust that a request came from your user. Always validate that the request is expected and legitimate before performing any action that changes data or state.
Building secure web applications is an ongoing effort. It requires a deep understanding of potential attack vectors and a commitment to implementing robust defenses at every stage of the development lifecycle.
Continuous Monitoring and Threat Intelligence
Even with the best security practices in place, new threats pop up all the time. That’s why keeping an eye on what’s happening and staying informed is so important. Continuous monitoring means actively watching your systems for any unusual activity that might signal an attack. Threat intelligence is about gathering information on current and emerging threats so you can get ahead of them. It’s like having a security guard who’s always watching and a detective who’s always researching.
| Monitoring Area | What to Look For |
|---|---|
| Network Traffic | Unusual connection patterns, unexpected data flows |
| Application Logs | Failed login attempts, error spikes, suspicious input |
| User Behavior | Abnormal access times, unusual activity sequences |
| Certificate Anomalies | Expired or untrusted certificates, unexpected changes |
Incident Response Planning for Browser Compromises
So, what happens if, despite all your efforts, a browser-based attack does succeed? Having a solid plan for how to respond is key. This isn’t just about fixing the immediate problem; it’s about minimizing damage, understanding what happened, and making sure it doesn’t happen again. A good incident response plan should cover everything from how to detect a compromise to how to recover and learn from the event. It’s about being prepared for the worst-case scenario.
- Define Roles and Responsibilities: Clearly outline who is responsible for what during an incident. This avoids confusion and speeds up the response.
- Establish Communication Channels: Determine how internal teams and external stakeholders (like customers or regulators) will be notified and updated.
- Develop Containment Strategies: Plan how to isolate affected systems to prevent the attack from spreading further.
- Outline Recovery Procedures: Detail the steps needed to restore systems and data to a secure state.
- Conduct Post-Incident Analysis: After the dust settles, thoroughly review the incident to identify root causes and implement improvements.
Wrapping Up: Staying Ahead of the Game
So, we’ve looked at how attackers can get right into the middle of things, messing with your online chats and transactions. It’s a bit like someone listening in on your phone calls, but way more technical. The bad news is, these kinds of attacks aren’t going away anytime soon. They keep finding new ways to trick us and sneak past defenses. The good news? We’re not totally helpless. By staying aware, using strong security habits like unique passwords and two-factor authentication, and keeping our software updated, we can make it a lot harder for these attackers. It’s really about being a little more careful online, like double-checking who you’re talking to before you share anything important. Think of it as locking your doors – you do it every day because it just makes sense.
Frequently Asked Questions
What exactly is a Man-in-the-Browser attack?
Imagine someone secretly sitting between you and your favorite website, like your online bank. A Man-in-the-Browser attack is when bad guys get into your computer and can see or even change what you do online, like when you log in or make a purchase, without you knowing. They’re like a sneaky spy in your web browser.
How do attackers get into my browser?
Attackers often trick you into letting them in. They might send you an email with a bad link or attachment, or create fake websites that look real. Sometimes, they can even sneak in through harmful browser add-ons or by tricking you into downloading unsafe software that seems okay at first.
What can attackers do once they’re in my browser?
Once they’re inside, they can do a lot of damage. They might steal your usernames and passwords, especially for important sites like banking or email. They can also change the details of online shopping orders, trick you into sending money to the wrong place, or steal your personal information to pretend to be you.
How is this different from other online spying?
Unlike other spying methods that might happen on the network, Man-in-the-Browser attacks happen directly on your computer, inside your web browser. This means they can see and change things right as you’re doing them, making it harder to detect than someone just listening in on your internet connection.
What are the biggest dangers for regular people like me?
The main worries are losing money from your bank account, having your identity stolen, or someone taking over your online accounts. It can also make you feel unsafe and worried about using the internet, which is a big problem for your privacy.
How can companies protect their websites and customers?
Companies need to build their websites very securely, making sure they check all the information users send. They should also use strong ways to check who is logging in, like asking for more than just a password. Keeping their systems updated and watching out for strange activity is also key.
What can I do to protect myself?
Always keep your web browser and computer updated with the latest security patches. Be very careful about clicking links or downloading files, especially from emails you weren’t expecting. Using strong, unique passwords and enabling two-factor authentication whenever possible adds extra layers of safety.
Are these attacks getting more advanced?
Yes, attackers are always finding new ways. They’re using smarter tricks, like making fake messages that seem very personal, and finding ways to attack browsers on phones and other devices. They’re also getting better at hiding what they’re doing, making them harder to catch.
