You know, clicking on ads used to be pretty harmless, just a way to find stuff online. But lately, things have changed. Malvertising delivery systems are becoming a big deal, and frankly, it’s a bit worrying. These aren’t your typical annoying pop-ups; they’re sneaky ways bad actors get malware onto your computer or steal your information, often without you even realizing it. It’s like a digital wolf in sheep’s clothing, hiding in plain sight on websites we visit every day. Let’s break down how this whole malvertising thing works and what we can do about it.
Key Takeaways
- Malvertising delivery systems use ads on legitimate sites to spread harmful software or steal data, making them hard to spot.
- Attackers use various methods like drive-by downloads, fake updates, and compromised extensions to get malware onto devices.
- These attacks often trick users through deceptive ad content or by impersonating trusted brands to harvest credentials.
- Ad networks struggle to keep up with the rapid spread and complex tactics used in malvertising campaigns.
- Protecting yourself involves using ad blockers, keeping software updated, and being generally cautious about what you click on.
Understanding Malvertising Delivery Systems
Malvertising, at its core, is about using online advertisements as a vehicle for malicious software or scams. It’s not just about annoying pop-ups anymore; these ads are becoming increasingly sophisticated, making it harder for the average person to spot them. The goal is simple: trick you into clicking something you shouldn’t, or sometimes, just visiting a page that has a bad ad on it, which then infects your device without you even doing anything. This whole process relies on the vast, interconnected world of digital advertising, where ads are bought, sold, and displayed across millions of websites every second.
The Evolving Landscape of Malvertising
The way malvertising works has changed a lot over the years. Back in the day, it might have been a simple banner ad that led to a scammy website. Now, attackers are much smarter. They’ve figured out how to sneak malicious code into ads that look perfectly legitimate, often using techniques that exploit vulnerabilities in web browsers or plugins. They also know how to make these ads appear on trusted websites, which is a big part of why it’s so effective. It’s a constant game of cat and mouse, with advertisers and security researchers trying to keep up with the latest tricks.
Leveraging Trusted Platforms for Malicious Aims
One of the most concerning aspects of malvertising is how attackers exploit the trust we place in legitimate websites and ad networks. Think about it: you’re reading a news article or browsing a favorite shopping site, and an ad pops up. You probably don’t think twice about it because it’s on a site you trust. Attackers use this trust to their advantage. They might buy ad space through legitimate channels, making their malicious ads appear alongside legitimate ones. This makes it incredibly difficult for users to distinguish between safe and harmful content. It’s like finding a wolf in sheep’s clothing, but the sheep are your favorite websites.
The Impact of Malvertising on Users and Businesses
For users, the impact can range from annoying adware to serious data theft or financial loss. A single click on a malvertising link could lead to your personal information being compromised or your computer being infected with ransomware. For businesses, malvertising can damage their reputation if their site is unknowingly hosting malicious ads. It can also lead to lost productivity, increased IT support costs, and potential legal liabilities. The interconnected nature of the web means that a problem on one site can quickly spread, affecting many others. It’s a threat that touches everyone, from individual consumers to large corporations, and understanding how these systems work is the first step in defending against them. The sheer volume of ads displayed daily means that even a small percentage of malicious ads can impact millions of users, making ad blocking a common defense strategy.
Common Attack Vectors in Malvertising
Malvertising isn’t just about annoying pop-ups; it’s a serious threat that uses online ads to spread harmful software. Attackers are pretty clever about how they get these bad ads onto websites you actually visit. They don’t just stick them anywhere; they often find ways to sneak them onto trusted platforms, making it harder for regular users to spot the danger.
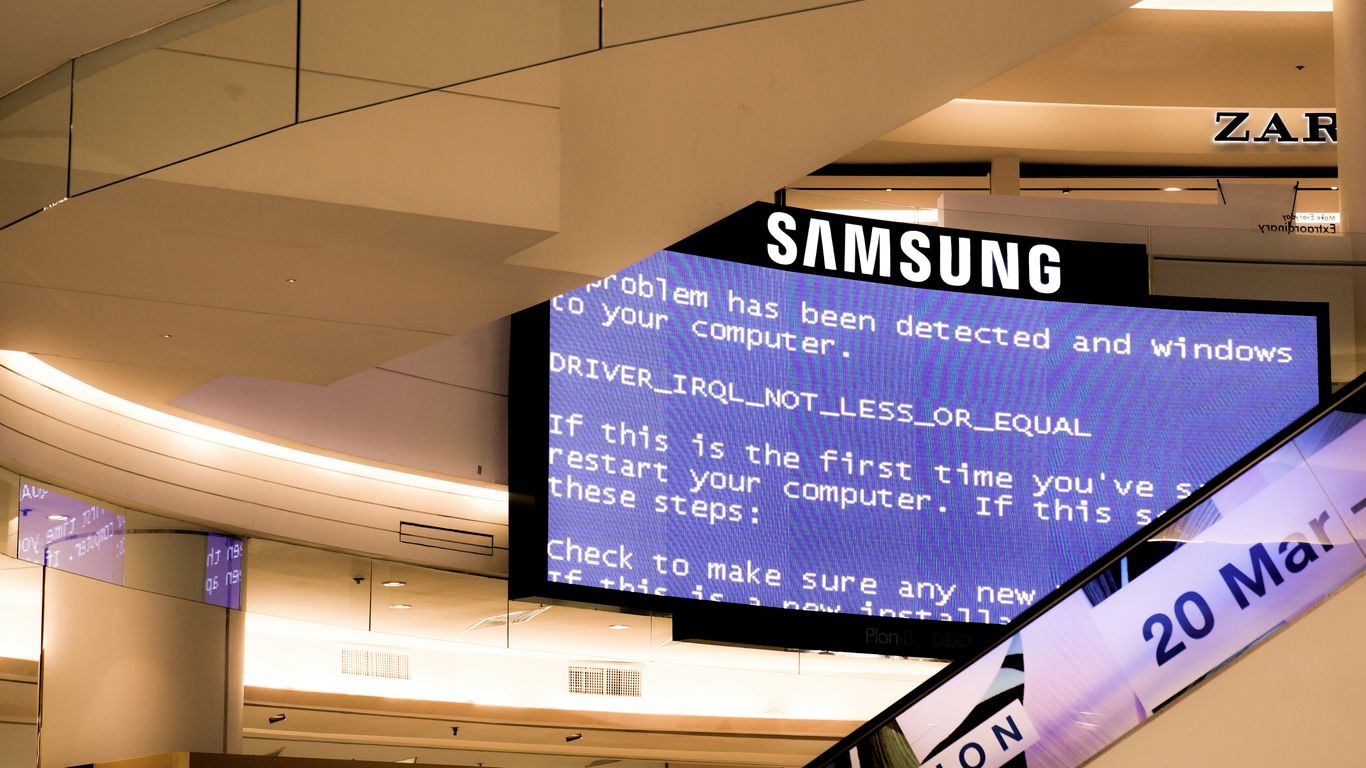
Drive-By Downloads and Malicious Websites
One of the most common ways malvertising works is through "drive-by downloads." This is where you visit a website, and without you even clicking anything, malicious code downloads onto your computer. The ad itself might be the trigger, or the website hosting the ad could be compromised. These ads can exploit vulnerabilities in your browser or its plugins. Sometimes, the ads will redirect you to a completely separate malicious website designed solely to infect your device. These sites often look legitimate, mimicking popular brands or services to trick you into downloading something or giving up information. It’s a bit like walking into a store and having something slipped into your bag without you noticing.
Compromised Software Updates and Installers
Attackers also use malvertising to push fake software updates or installers. You might see an ad claiming to be an update for your browser, an antivirus program, or even a popular game. When you click it, instead of getting a legitimate update, you download malware. This is especially effective because people are often looking for updates and tend to trust them. The ads might look official, using logos and branding that are hard to distinguish from the real thing. This tactic plays on the user’s desire to keep their software current and secure, ironically leading them to a less secure state. It’s a classic bait-and-switch, but with digital consequences.
Malicious Browser Extensions and Typosquatting
Another vector involves malicious browser extensions. Ads might promote a seemingly useful extension, like a coupon finder or a social media tool. Once installed, these extensions can inject more ads, redirect your browsing, or even steal your data. They have a lot of power because they operate within your browser. Then there’s typosquatting. This is where attackers register domain names that are very similar to popular websites, often with a small typo. Ads might be placed on these fake sites, or users might accidentally land on them when they mistype a URL. These sites are then used to serve malicious ads or host phishing pages, hoping to catch users who aren’t paying close attention to the web address they’re visiting. It’s a subtle but effective way to intercept traffic and users. For more on how these attacks work, understanding penetration testing methodologies can offer insight into how attackers probe for weaknesses.
Exploitation Techniques Used in Malvertising
Malvertising isn’t just about putting a bad ad on a page. The way these malicious ads actually cause harm is a mix of technical tricks and psychological manipulation. Cybercriminals try to fly under the radar by exploiting trust, using software bugs, and tricking people into revealing sensitive information. Let’s break down some of the most common tactics they use:
Exploiting Software Vulnerabilities
Hackers design malicious ads to target weaknesses in popular software. Sometimes these weak spots come from outdated browsers, unpatched plugins, or operating systems that haven’t been updated in a while. Here’s what typically happens:
- A user visits a website showing a malicious ad.
- The ad silently checks the user’s system for known vulnerabilities.
- If a weakness is found, the ad launches code that downloads and runs malware on the device—no clicks needed.
The speed of these attacks means even a brief visit to a compromised site can be enough to endanger your data and devices.
Social Engineering Tactics in Ad Content
Some malvertising campaigns don’t rely on software flaws or technical bugs. Instead, the ads are designed to trick people using psychological tricks such as urgency or fake authority. Typical tactics include:
- Ads pretending to be security warnings, saying your computer is infected and you need to act fast.
- Offers that sound too good to be true (“You’ve won!” or unrealistic discounts), catching users off guard.
- Imitation of official software or service alerts, complete with brand logos to boost credibility.
Attackers know that a convincing message is sometimes enough to get someone to click, download, or submit personal info, even if all the systems are up to date.
Credential Harvesting Through Deceptive Ads
A common goal of malvertising is stealing usernames and passwords with fake input forms. These ads often look identical to real login portals or password reset pages. The process usually looks like this:
- The user clicks an ad promising account access or a needed update.
- The ad opens a site that looks exactly like a real login page (often with a familiar logo).
- When the user enters their credentials, the data goes straight to the attacker.
| Technique | Attacker’s Goal | User Action Required |
|---|---|---|
| Exploiting Software Bugs | Install malware silently | None |
| Social Engineering in Ads | Trick user into clicking | Click or download |
| Credential Harvesting | Steal usernames/passwords | Enter info on page |
Each of these methods is a variation on one theme: attackers use the ad delivery infrastructure to reach everyday users where they least expect it.
Dealing with malvertising isn’t just about technology. It’s about understanding how attackers blend technical exploits with human manipulation. If you’re running a business, staying on top of both software updates and user training can make these tactics less effective.
The Role of Ad Networks and Exchanges
Ad networks and exchanges are the plumbing of the digital advertising world. They connect advertisers who want to show ads with publishers who have space for them on their websites and apps. It sounds straightforward, but this system is also a major pathway for malvertising. Because these networks operate at such a massive scale, and often automate the process of placing ads, it can be really hard to keep bad actors out.
Automated Ad Placement and Targeting
Think about how many ads you see every day. Ad networks use complex systems to figure out which ads to show to which people, based on things like browsing history, location, and demographics. This automation is super efficient for advertisers, but it also means that malicious ads can get placed very quickly and widely before anyone notices. The sheer volume of ads processed means that even a small percentage of malicious ones can reach millions of users.
Challenges in Ad Network Security
Keeping these networks secure is a huge challenge. There are so many players involved – advertisers, ad agencies, publishers, and the networks themselves. It’s a complex supply chain. Security measures often struggle to keep up with the speed and sophistication of attackers. Sometimes, legitimate advertisers might unknowingly buy ad space through a compromised intermediary, or a publisher might unknowingly display an ad that was approved by the network but later found to be malicious. The decentralized nature and rapid pace of digital advertising make robust security incredibly difficult to maintain.
The Supply Chain of Digital Advertising
Malvertising often exploits weaknesses in this supply chain. An attacker might compromise a single point, like an ad agency or a third-party ad tech vendor, to inject malicious code into ads that then get distributed across many different websites. This means that even if a publisher has good security on their own site, they can still be affected if the ads they display come from a compromised source. It’s like a virus spreading through a shared resource.
Here’s a look at the typical flow:
- Advertiser: Creates an ad campaign.
- Ad Agency/DSP (Demand-Side Platform): Buys ad space on behalf of the advertiser.
- Ad Network/Exchange: Facilitates the buying and selling of ad inventory.
- Publisher Website/App: Displays the ad space.
- User: Sees and potentially interacts with the ad.
Attackers often target the less scrutinized parts of this chain, like smaller ad agencies or third-party data providers, to gain a foothold. Once inside, they can push malicious creatives that bypass initial checks.
Advanced Malvertising Strategies
Redirect Chains and Obfuscation Techniques
Malvertisers are getting pretty clever about hiding what they’re up to. Instead of a direct link from an ad to a malicious site, they often use a series of redirects. Think of it like a shell game; each redirect bounces you to another page, making it harder to trace the final destination. These chains can involve multiple servers, sometimes legitimate ones that have been compromised, to further muddy the waters. The actual malicious payload might only be loaded after several hops, and often, it’s hidden using obfuscation techniques. This means the code is deliberately made difficult to read and understand, even for security software. It’s like trying to read a book written in a secret code – you need the key to figure out what’s really going on.
Exploiting User Trust and Brand Impersonation
One of the most effective ways attackers trick people is by pretending to be someone trustworthy. They’ll create ads that look exactly like they’re from well-known brands – think big tech companies, popular retailers, or even government agencies. This is called brand impersonation. The ads might promise a special deal, a free giveaway, or an urgent security alert. The goal is to make you click without thinking twice. Because the ad looks legitimate, users are more likely to trust it and proceed, often leading them to fake login pages or sites that try to download malware. It’s a classic social engineering trick, just done through advertising.
Fileless Malware and Living-Off-The-Land Tactics
Attackers are also moving away from traditional malware files that get saved to your computer. Instead, they’re using fileless techniques. This means the malicious code runs directly in your computer’s memory, or it uses legitimate system tools that are already installed on your machine to carry out its tasks. This is often called ‘living off the land’. Since it doesn’t create new, suspicious files, it’s much harder for antivirus software to detect. Imagine a burglar using your own tools to break into your house – it’s much harder to spot than someone bringing their own crowbar. These methods are stealthy and can persist on a system for a long time without being noticed, making them particularly dangerous.
Mitigation and Defense Against Malvertising
Dealing with malvertising means we need a few layers of defense. It’s not just one thing, but a combination of tools and smart habits that help keep you and your systems safe from those sneaky ads. Think of it like building a fortress – you need strong walls, watchful guards, and educated citizens.
Ad Blocking and Browser Hardening
First off, using ad blockers is a pretty straightforward way to stop a lot of malicious ads before they even load. These tools can prevent the ad code from running, which often stops the malvertising script in its tracks. Beyond just ad blockers, tweaking your browser’s security settings can also make a big difference. This might involve disabling certain scripts by default, managing cookies more carefully, or using browser extensions that specifically focus on privacy and security. The goal here is to reduce the attack surface your browser presents to the web.
- Ad Blockers: Install and configure reputable ad-blocking extensions.
- Browser Settings: Regularly review and adjust privacy and security settings (e.g., JavaScript execution, third-party cookies).
- HTTPS Enforcement: Ensure your browser prioritizes secure HTTPS connections.
- Pop-up Blockers: Keep pop-up blockers enabled to prevent unexpected windows.
Sometimes, even with the best blockers, a malicious ad can slip through. This is why it’s important not to rely solely on one method. Staying vigilant is key.
Endpoint Security and Network Monitoring
On the system level, good endpoint security software is non-negotiable. This includes up-to-date antivirus and anti-malware solutions that can detect and remove threats. For businesses, more advanced endpoint detection and response (EDR) systems provide deeper visibility and faster reaction times. Network monitoring also plays a role. By watching traffic patterns, security teams can sometimes spot unusual activity that might indicate a malvertising campaign is underway, like unexpected redirects or connections to known malicious servers. This helps catch threats that might bypass individual user defenses.
- Antivirus/Anti-Malware: Keep software updated and run regular scans.
- EDR Solutions: Deploy advanced endpoint protection for real-time threat detection and response.
- Firewalls: Configure and maintain firewalls to control network traffic.
- Intrusion Detection/Prevention Systems (IDPS): Implement systems to monitor for and block malicious network activity.
User Education and Awareness Training
Honestly, a lot of malvertising relies on tricking people. That’s where education comes in. Teaching users to be skeptical of ads, especially those that seem too good to be true, or that appear suddenly and aggressively, is super important. Knowing what to look out for – like suspicious links, urgent calls to action, or requests for personal information within an ad – can prevent many infections. Regular training sessions can help keep these risks top of mind for everyone using a device or network.
- Recognize common social engineering tactics used in ads.
- Understand the risks associated with clicking on unexpected or suspicious advertisements.
- Know how to report suspicious ads or potential security incidents.
- Practice safe browsing habits, including verifying website legitimacy before interacting.
The Impact of Malvertising on Security Posture
Malvertising doesn’t just annoy users with pop-ups; it actively degrades an organization’s overall security stance. When malicious ads slip through, they create new entry points, making the digital environment more vulnerable. This means more work for security teams trying to keep everything locked down.
Increased Attack Surface Exposure
Every ad displayed on a legitimate site, especially through compromised ad networks, effectively widens the potential entry points for attackers. Think of it like leaving more doors unlocked in a building. These ads can lead users to malicious sites, trigger drive-by downloads, or even attempt to exploit browser vulnerabilities directly. The sheer volume and reach of online advertising mean that even a small percentage of malicious ads can significantly expand the attack surface for any organization whose employees or customers might encounter them. This exposure is particularly concerning as it often bypasses traditional perimeter defenses, reaching users directly on their devices.
Challenges in Threat Detection and Response
Spotting malvertising campaigns can be tricky. The ads themselves often look legitimate, and the malicious payload might be hidden behind multiple redirects or obfuscated code. This makes it hard for standard security tools to flag them. When an incident does occur, tracing it back to a specific ad can be a complex investigation. It requires correlating network traffic, endpoint logs, and potentially even ad network data, which isn’t always readily available. This complexity can slow down response times, giving attackers more opportunity to cause damage or move deeper into a network.
Maintaining Compliance and Regulatory Adherence
Many cybersecurity regulations, like GDPR or HIPAA, require organizations to protect user data and maintain secure systems. A malvertising incident that leads to a data breach or system compromise can result in significant regulatory penalties. Proving that adequate measures were in place to prevent such incidents, especially when they originate from third-party ad content, can be a legal and technical challenge. Organizations need robust policies and technical controls to demonstrate due diligence in protecting against these evolving threats, which often involves a combination of technical solutions and user awareness training.
Future Trends in Malvertising Delivery
The world of malvertising is always shifting, and keeping up with what’s next is key. We’re seeing some pretty interesting developments that are going to change how these attacks happen.
AI-Driven Ad Content and Targeting
Artificial intelligence is already a big part of how ads are shown to us, and now bad actors are getting in on it. They’re starting to use AI to make ads that are way more convincing. Think about ads that can change based on who’s looking at them, or even ads that use deepfake technology to impersonate trusted brands or people. This makes it much harder for regular people to spot a fake. It’s not just about showing you more ads; it’s about showing you the right ad at the right time to trick you.
Exploitation of Emerging Technologies
As new tech pops up, so do new ways to exploit it. We’re already seeing this with things like the Internet of Things (IoT) devices. These devices often have weak security, and malvertising campaigns could use them to spread malware or launch attacks. Imagine your smart fridge suddenly becoming part of a botnet because of a malicious ad it saw. Plus, as augmented reality (AR) and virtual reality (VR) become more common, we’ll likely see malvertising pop up in those spaces too, maybe through fake virtual storefronts or deceptive in-app ads. It’s a whole new frontier for attackers.
The Evolving Threat Landscape
What we’re up against is constantly changing. Attackers are getting smarter, using more complex methods to hide their tracks. This includes things like redirect chains, where an ad sends you through multiple sites before landing you on a malicious one, making it tough to trace back. They’re also getting better at using legitimate services to host their malicious code, making it harder for security software to flag them. The goal is always to stay one step ahead of defenses.
Here’s a quick look at some of the evolving tactics:
- AI-powered personalization: Ads that adapt to user behavior and demographics.
- Deepfake integration: Using AI-generated media to impersonate trusted entities.
- IoT exploitation: Targeting connected devices with often-weak security.
- Cross-platform attacks: Spreading malvertising across web, mobile, and emerging platforms.
- Supply chain abuse: Compromising ad tech platforms to distribute malware at scale.
The sophistication of malvertising is increasing, moving beyond simple banner ads to more integrated and deceptive forms of digital persuasion. Staying informed and employing robust security measures are more important than ever.
Wrapping Up: Staying Ahead of the Game
So, we’ve looked at a bunch of ways bad actors try to get into systems, from sneaky ads to tricking people with emails. It’s clear that these methods, like malvertising and phishing, are always changing. They use different tools and tricks, sometimes even using legitimate-looking updates or extensions to get in. Staying safe means we all have to keep learning and adapting. Using security software is a start, but being aware of how these attacks work is just as important. It’s not a one-and-done thing; it’s more like a constant effort to stay one step ahead.
Frequently Asked Questions
What exactly is malvertising?
Malvertising is like a nasty surprise hidden in online ads. It’s when bad guys sneak harmful code into ads that look normal. When you click on these ads, or sometimes even just see them, your computer or device can get infected with malware, which is bad software.
How do bad guys get their harmful ads onto popular websites?
They’re pretty sneaky! They often use the same systems that legitimate advertisers use to place ads. Sometimes they trick ad companies, or they might find a way to put their bad ads onto websites that are already trusted by many people. It’s like hiding something bad in plain sight.
What’s the biggest danger of seeing a malicious ad?
The main danger is that your device could get infected with malware without you even realizing it. This malware could steal your personal information, like passwords or bank details, or it could mess up your computer, making it slow or unusable.
Are there different ways malvertising can harm me?
Yes, there are a few ways. Some ads try to trick you into downloading harmful software yourself (like fake updates). Others might automatically download bad stuff onto your device just by you visiting the webpage (this is called a drive-by download). Some ads might also try to steal your login information if you’re not careful.
Can ad blockers stop malvertising?
Ad blockers can definitely help! They work by stopping many ads from showing up on websites in the first place. This means you won’t see the harmful ads, and the chance of getting infected goes down a lot. However, they aren’t perfect, and sometimes new tricks can get around them.
What can I do besides using an ad blocker to stay safe?
Keeping your web browser and computer software updated is super important, as updates often fix security holes. Also, being careful about what you click on and not downloading things from untrusted sources are good habits. Having good security software on your device helps too.
Why is it hard for websites and ad companies to stop malvertising?
It’s tricky because the online ad world is huge and very fast. Ads are placed automatically, and it’s hard to check every single one to make sure it’s safe before it appears. Bad guys are also always finding new ways to hide their harmful ads, making it a constant challenge to catch them.
What happens if a business gets hit by malvertising?
For businesses, malvertising can be a big problem. It can lead to their customers getting infected, which hurts the business’s reputation. It can also cause disruptions to their own websites or systems if the malware spreads, leading to lost time and money.
