So, you’ve got all these cool smart gadgets around your house, right? From your thermostat to your fridge, they’re all connected. It’s pretty neat, but have you ever stopped to think about the security side of things? Turns out, all these handy devices can actually open up some serious risks if we’re not careful. This article is all about those potential problems with IoT security and what we can do about them.
Key Takeaways
- Many smart devices come with weak passwords or no real security checks, making them easy targets for hackers.
- Data sent between devices and the internet often isn’t protected, meaning sensitive info could be seen by the wrong people.
- Managing and updating all these connected devices can be a real headache, especially when they’re hard to reach or old.
- There are risks from people physically messing with devices or from bad parts used when they’re made.
- If a smart device gets hacked, it can cause big problems, like messing up entire networks, stopping important services, or leading to stolen information and money loss.
Inherent Vulnerabilities in IoT Devices
So, let’s talk about why these smart gadgets can be a bit of a security headache right from the start. It’s not always about some super-advanced hack; often, the problems are built right in.
Weak Authentication Systems
This is a big one. Think about it: many IoT devices come with default passwords like ‘admin’ or ‘12345’. Seriously? These are often plastered all over the user manual or easily found online. It’s like leaving your front door wide open with a sign saying ‘Free stuff inside’. Even if you change it, sometimes a single password isn’t enough. Hackers are really good at guessing or finding ways to steal those credentials. It’s the easiest way in for them.
- Manufacturers often use the same default passwords across thousands of devices.
- These default credentials are frequently documented and publicly accessible.
- Even strong user-set passwords can be vulnerable if only one layer of security is present.
Limited Device Processing Power
Many of these devices are designed to be small and cheap, which means they don’t have a lot of computing muscle. This lack of power makes it tough to run complex security software. You can’t exactly install a full antivirus program on your smart toaster, right? This means they often can’t handle things like strong encryption or sophisticated threat detection, leaving them exposed.
The drive for smaller, cheaper devices often means security takes a backseat. Manufacturers prioritize features and cost, leaving security as an afterthought, which creates a perfect storm for vulnerabilities.
Inconsistent Security Standards
There isn’t really a universal rulebook for how IoT devices should be secured. Different companies do their own thing, and some just don’t put much effort into security at all. This patchwork of standards means you never quite know what you’re getting. One device might be reasonably secure, while another, doing a similar job, could be wide open. It makes it really hard for consumers and businesses to know which products are safe to use.
Risks Associated with Data Transmission

When your smart devices start talking to each other, or to the cloud, they send data back and forth. This data can be anything from your daily step count to sensitive industrial control signals. The problem is, how they send it matters a whole lot. If that data isn’t protected, it’s like sending a postcard instead of a sealed letter. Anyone who intercepts it can read exactly what you’re sending.
Unencrypted Data Transmission
This is a big one. A staggering 98% of Internet of Things (IoT) device traffic is unencrypted, leaving nearly all data unprotected. Many devices just don’t bother encrypting the information they send out. This means if someone manages to snoop on your network, they can easily grab login details, personal information, or any other data being exchanged. It’s especially risky when devices are sending data over public networks, where interception is much easier. Think of it like shouting your secrets across a crowded room.
- Network Sniffing: Attackers can use tools to capture data packets traveling across a network.
- Man-in-the-Middle Attacks: An attacker positions themselves between your device and the server it’s communicating with, intercepting and potentially altering data.
- Compromised Network Infrastructure: If the network itself is breached, all traffic passing through it becomes vulnerable.
Protecting data in transit is not just about preventing casual snooping; it’s about stopping determined attackers from gaining access to sensitive information that could lead to identity theft, financial loss, or operational sabotage.
Gaps Between Mobile Networks and Cloud
Even if your IoT device uses a secure cellular network and connects to a secure cloud service, there’s often a weak link in the chain. The journey from the mobile network to the cloud usually happens over the public internet. This part of the trip can be exposed. It’s like having a secure vault at home and a secure bank, but leaving the money on a public bus between the two. Even small vulnerabilities in this connection can compromise the entire IoT deployment. Manufacturers and users need to pay attention to these transition points, often using specialized cloud connectivity solutions to bridge these gaps securely.
Challenges in IoT Device Management
Managing all those smart gadgets connected to your network can feel like herding cats, especially when they’re scattered all over the place. It’s not like managing your usual computers or phones; IoT devices often get deployed in spots that are tough to reach, like remote sensors or equipment deep inside a factory. This makes keeping an eye on them and pushing out updates a real headache.
Difficulties in Remote Monitoring and Updates
When a device is out in the middle of nowhere, or even just in a hard-to-access closet, checking its status or installing a security patch becomes a big job. Sometimes, the network connection itself is too slow or unreliable for remote updates. This means you might have to physically go to the device, which is time-consuming and expensive. This lack of easy remote access is a major roadblock to keeping IoT systems secure.
Lack of Device Visibility and Control
Many organizations don’t really know what’s connected to their network. They might not have a good list of all the IoT devices, what they’re doing, or what security measures they have in place. Without this basic inventory, it’s hard to manage them properly. It’s like trying to secure your house when you don’t even know how many doors and windows you have.
Legacy Asset Incompatibility
Older devices, the ones that were around before IoT security was a big concern, often don’t play well with newer security systems. They might not support modern encryption or authentication methods. Trying to integrate these older pieces into a secure network can be really tricky, and sometimes it’s just not possible without replacing them entirely, which costs money.
Keeping track of IoT devices is a whole different ballgame than managing traditional IT equipment. The sheer number of devices, their varied locations, and the fact that many were never designed with robust security in mind create a complex environment. Without a clear picture of what’s connected and how it’s behaving, it’s easy for security gaps to appear and go unnoticed.
Physical and Supply Chain Security Concerns
Beyond the digital realm, IoT devices face threats that are quite literally in the physical world. It’s not just about code and networks anymore; we’re talking about hardware and how these devices get to us in the first place.
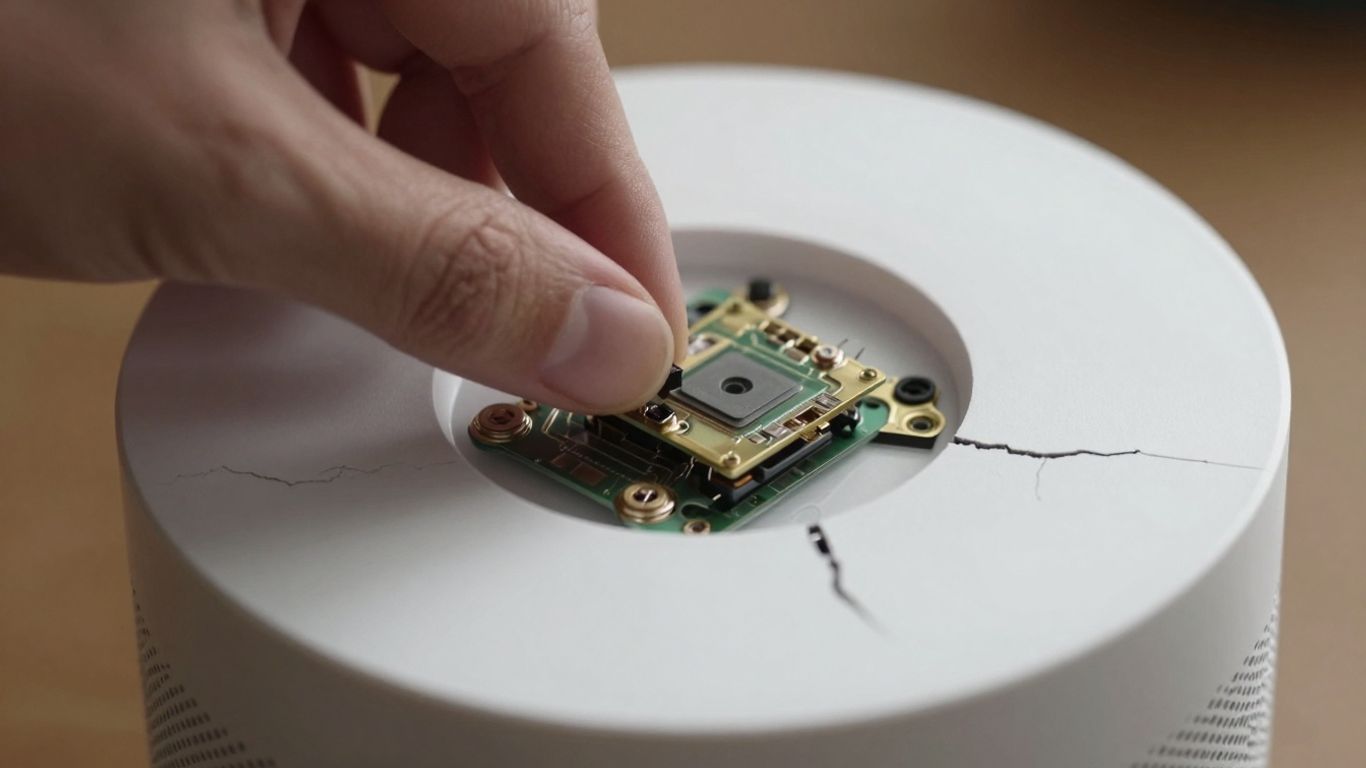
Hardware Attacks and Tampering
Think about it: if someone can get their hands on an IoT device, they might be able to mess with it directly. This could mean trying to physically alter the hardware, perhaps to install malicious software or extract sensitive information. These kinds of direct physical intrusions can bypass many software-based security measures. It’s like trying to secure your house with a strong lock, but then someone just breaks a window.
Physical Access Vulnerabilities
This ties into hardware attacks. Many IoT devices end up in places that aren’t exactly Fort Knox. They might be in public spaces, remote locations, or just easily accessible areas within a building. If an attacker can physically reach the device, they might be able to:
- Access diagnostic ports to gain unauthorized control.
- Replace legitimate firmware with a compromised version.
- Physically remove storage components containing data.
- Tamper with sensors or other operational parts.
Supply Chain Integrity Issues
This is a big one, and it happens before the device even gets to you. The journey from the factory floor to your doorstep is complex, involving multiple manufacturers, component suppliers, and logistics providers. At any point along this chain, something could go wrong:
- Malicious Components: A supplier might intentionally or unintentionally include a compromised component, like a chip with hidden backdoors.
- Tampered Firmware: The device’s initial software could be altered during manufacturing or transit to include malware.
- Lack of Transparency: It can be hard to know exactly where every single part of an IoT device came from and whether it’s been tampered with. This lack of visibility makes it tough to trust the device from the get-go. Securing the entire supply chain is becoming increasingly important for businesses.
The complexity of modern manufacturing means that a single IoT device can have components sourced from dozens of different places. Verifying the integrity of each piece, and the assembly process itself, is a monumental task. Without robust checks, vulnerabilities can be baked in from the very start, making the device a ticking time bomb.
It’s a bit like ordering a custom-built computer; you trust the builder, but do you really know where every single RAM stick or hard drive came from? With IoT, the stakes can be much higher, especially when these devices are connected to critical infrastructure or handle sensitive personal data.
Consequences of Compromised IoT Security
When the security on your smart devices goes south, it’s not just a minor inconvenience. We’re talking about potential domino effects that can ripple through your entire digital life and even impact physical operations. The fallout from unsecured IoT devices can be pretty severe.
Network-Wide Compromises
Think of your IoT devices as tiny doors into your home or business network. If one of those doors is left unlocked, or has a flimsy lock, it’s an open invitation for trouble. Attackers can use a compromised smart bulb or thermostat as a stepping stone to get into more sensitive parts of your network. From there, they can spread like wildfire, accessing personal files, financial information, or even taking control of other connected systems. It’s like letting a fox into the henhouse; once it’s in, it can cause a lot of damage.
Disruption of Critical Operations
For businesses and industries that rely heavily on IoT, a security breach can bring everything to a grinding halt. Imagine a smart factory where the production line is controlled by networked sensors and machines. If those devices are compromised, an attacker could shut down operations, mess with manufacturing processes, or even cause physical damage to expensive equipment. This isn’t just about lost productivity; it can lead to significant financial losses and safety hazards, especially in sectors like energy, healthcare, or transportation. The interconnected nature of these systems means a single weak link can jeopardize critical infrastructure.
Data Leaks and Financial Losses
Many IoT devices collect a surprising amount of data, some of it quite personal or sensitive. Your smart speaker might be listening, your security camera is watching, and your fitness tracker knows your health habits. If these devices are hacked, all that information can be stolen and misused. This can lead to identity theft, financial fraud, or even blackmail. Beyond personal data, businesses can suffer huge financial hits from downtime, the cost of recovering from a breach, regulatory fines for data privacy violations, and damage to their reputation. It’s a costly lesson to learn when security is an afterthought.
Mitigating IoT Security Risks
So, we’ve talked about all the ways things can go wrong with IoT security. It can feel a bit overwhelming, right? But don’t worry, there are definitely ways to make your connected devices safer. It’s not about being perfect, but about putting up good defenses.
Implementing Strong Authentication
This is a big one. Think of it like locking your front door. If you leave it wide open, anyone can just walk in. Many IoT devices come with default passwords that are super easy to guess, like ‘admin’ or ‘12345’. Seriously, manufacturers sometimes make it that simple. The first thing you should do is change those default passwords to something unique and strong. And I don’t mean ‘password123’. We’re talking about a mix of letters, numbers, and symbols.
- Always change default credentials immediately.
- Use complex passwords that are hard to guess.
- Consider multi-factor authentication (MFA) if the device supports it, like using an app or a code sent to your phone.
- Regularly review and update your password policies.
Weak authentication is like leaving a window unlocked. It’s an easy invitation for trouble, and it’s one of the most common ways devices get compromised. Making authentication tougher is a solid first step.
Ensuring Data Encryption
When your IoT devices send information, it’s often like sending a postcard – anyone who intercepts it can read it. That’s not good, especially if it’s sensitive data. Encryption scrambles that information so only the intended recipient can understand it. It’s like putting your message in a sealed, coded envelope.
- Check if your devices support encryption for data in transit.
- Look for devices that encrypt data stored on the device itself.
- Understand the encryption methods used and if they are up-to-date.
Regular Firmware Updates
Manufacturers release updates, called firmware, to fix bugs and patch security holes. It’s like getting a software update for your phone, but for your smart fridge or security camera. Ignoring these updates is like ignoring a recall notice for your car – it leaves you vulnerable. Sometimes, these updates can be a pain, especially if you have a lot of devices or they’re in hard-to-reach places. But keeping firmware current is one of the most effective ways to protect against known exploits. If you’re managing a large number of devices, looking into solutions that help with remote updates can save a lot of hassle. You can find resources that offer strategies to secure IoT devices, which can be really helpful for IT teams. strategies to secure IoT devices
Wrapping Up: Staying Safe in a Connected World
So, we’ve talked a lot about how easily smart devices can be a weak link in our digital lives. From weak passwords that are practically an open invitation to hackers, to data zipping around without any protection, the risks are pretty real. It’s not just about losing your Netflix password; these devices can be entry points into bigger networks, or even used in massive online attacks. Keeping these gadgets secure isn’t just up to the companies that make them, though. We all have a part to play. Changing those default passwords, keeping software updated when we can, and just being aware of what’s connected to our network makes a difference. It’s a bit of a shared job, really, making sure our smart homes and workplaces don’t become easy targets.
Frequently Asked Questions
What makes smart devices easy targets for hackers?
Many smart devices have weak passwords, like the default ones they come with, or they don’t have strong security systems in place. Also, some devices aren’t powerful enough to run advanced security software, making them simpler for attackers to break into.
Why is sending information without scrambling it a problem?
When data travels without being scrambled (encrypted), anyone who intercepts it can easily read it. This is risky because it could include personal details or important commands that hackers could misuse.
What happens if a hacker takes over one smart device?
If a hacker gets control of one device, they might use it as a way to get into your whole home network or even a company’s network. They could also use many hacked devices together to launch attacks on websites or services.
Why is it hard to keep smart devices safe and updated?
It’s tough because many devices are in hard-to-reach places, making it difficult to check on them or update their software. Plus, there aren’t always clear rules for how secure these devices should be, so different companies do things differently.
Can someone physically harm a smart device or its data?
Yes, someone could physically get to a device and tamper with it, install bad software, or steal information. Even the way the device is made or where its parts come from can sometimes have security weaknesses.
What are the main consequences if smart device security fails?
If security fails, sensitive information can be stolen, important services might stop working, and hackers could even take over entire networks. This can lead to big money losses and disrupt everyday life, especially if critical systems are affected.
